As I wrote in my last blog, at Appdome, we continue to constantly revisit and improve our security features. In this blog, I will discuss how Appdome makes Mobile MiTM impossible.
Attacks can happen on every Wifi network the mobile phone connects to. And what’s most troubling is that Wifi attacks are an attack vector that does not require any physical access to the app or the mobile device.
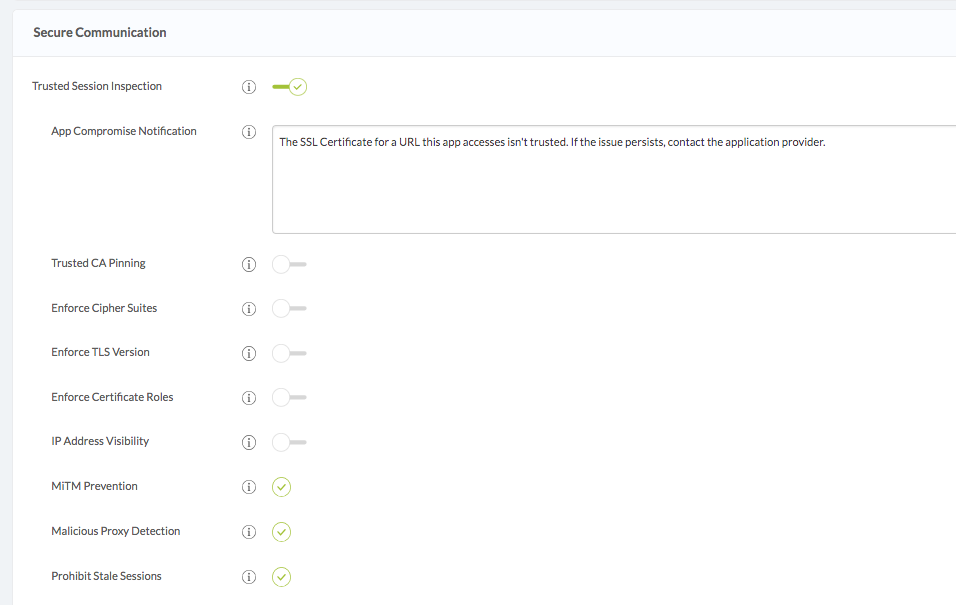
In our most recent release, we put extra emphasis on our Secure Communication solution and added more features, granularity and options to our Trusted Session Inspection implementation. As a result, we are proud to say that Appdome has made mobile MiTM attacks impossible.
How Appdome prevents Mobile MiTM Attacks
We made Mobile MiTM impossible by enforcing the following:
Enforce TLS Cipher-Suites allows our customers to limit the TLS cipher suites used in the secure handshake. Specifically, our customers can designate approved ciphers, selecting from a list of 350 possible cipher suites. As a result, only network connections using the designated approved ciphers will be allowed by our Trusted Session Inspection engine.
Enforce TLS Versions allows our customers to limit the network connections only to approved TLS versions. In contrast, older versions of TLS are susceptible to known networking attacks. Attacks like POODLE and BEAST rely on exploiting weaknesses of older implementations of TLS. For this reason, Enforce TLS Versions lets our customers limit the SSL/TLS versions of the network connections only to the approved versions, as a part of enforcing data in transit encryption.
Enforce Certificate Roles enables our customers to increase their level of trust of server-side certificates. Therefore Appdome’s code verifies that Leaf Certificates will not sign on other Certificates. In the knowledge base, there is a detailed explanation of this attack and the way to defend from it. Using Appdome, our customers can enforce roles for each certificate, for every network connection, thus ensuring that the chain of trust is maintained. As a result, the combination of these features makes MiTM attacks virtually impossible.
We keep updating our security features and standards as new vulnerabilities are found, so more to come.
In the meantime, get started with Appdome and protect your mobile apps from attacks.






