How to Make Android and iOS Apps Work with Microsoft ADFS
Learn how to make Android and iOS Apps Work with Microsoft ADFS. No Code. No SDK.
What is Microsoft ADFS?
Active Directory Federation Services (ADFS) is a Microsoft Windows Server component that provides users with single-sign-on access to systems and applications.
This Knowledge Base article provides step-by-step instructions for using Appdome to add ADFS SSO support to any Android and iOS mobile app. By using Appdome to add ADFS SSO, the mobile app will rely on and trust ADFS SSO and include the in-app mechanisms to securely store, use, retrieve and update the authentication credentials passed from ADFS SSO to the mobile app.
We hope you find this knowledge base useful and enjoy using Appdome!
Adding Microsoft ADFS to Any Mobile App Without Coding
Appdome is a no-code mobile app security platform designed to add security features and 3rd party services like Microsoft ADFS to Android and iOS apps without coding. This KB shows mobile developers, DevSec and security professionals how to use Appdome’s simple ‘click to build’ user interface to quickly and easily make mobile apps work with Microsoft authentication.
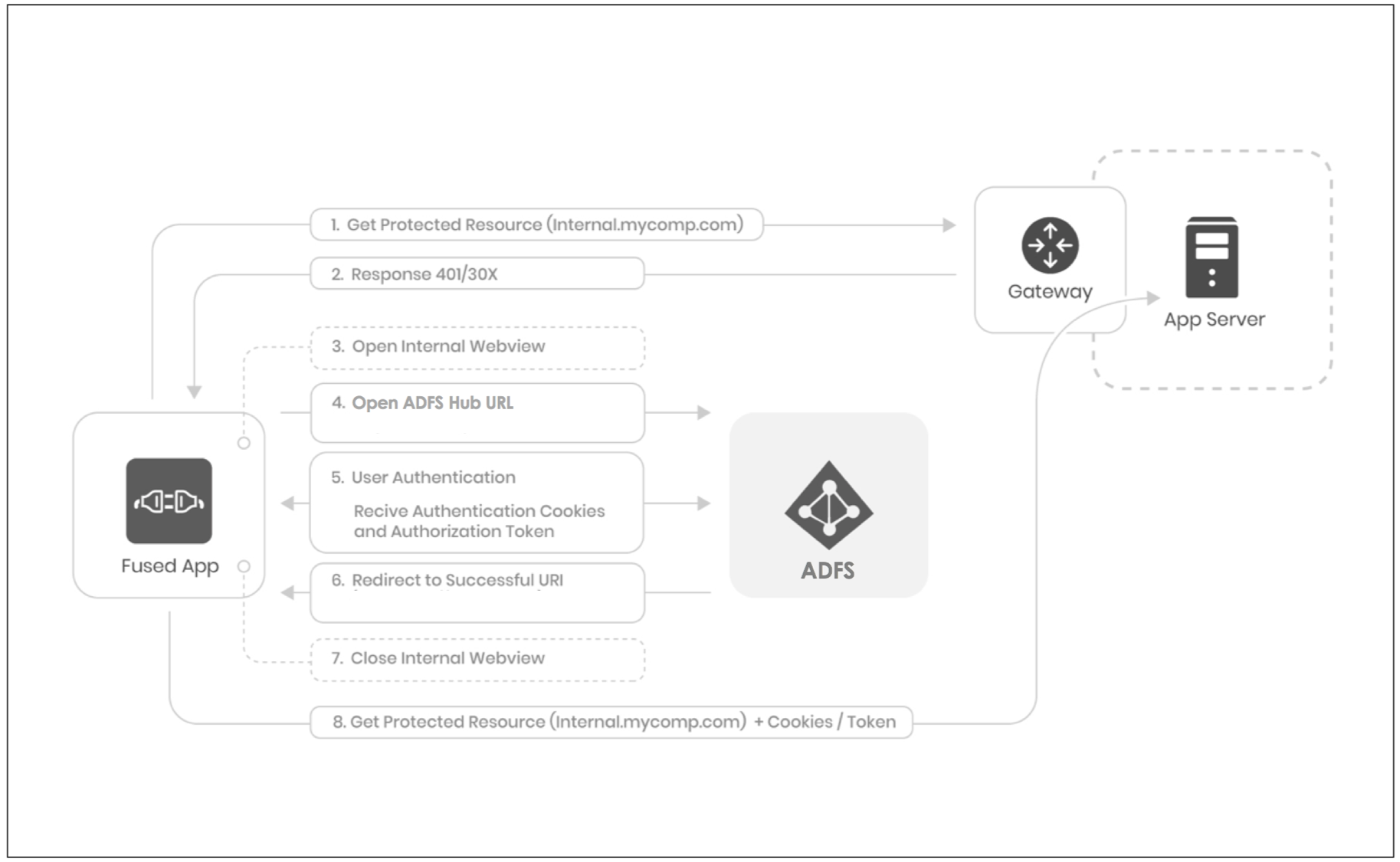
The following diagram illustrates the Single-Sign-On flow within the app when integrating ADFS as an Identity Provider (IdP):Using Appdome, there are no development or coding prerequisites. For example, there is no Appdome SDK, libraries, or plug-ins to implement. Likewise, there are no required infrastructure changes and no dependency on SAML, OAuth, OpenID Connect or any other authentication standard inside the app. The Appdome technology adds ADFS SSO and relevant standards, frameworks and more to the app automatically, with no manual development work at all. Using Appdome, mobile apps will use ADFS SSO to authenticate users as if ADFS SSO was natively coded to the app.
- The application sends a request to reach an unauthorized resource (protected by a gateway, AD, or the app server itself)
(e.g. https://appservice.mycompany.com) - The server protecting the resource responds with 401 or 30X response since the request is not authorized
- Appdome identifies the response for the protected resource and opens an internal Webview within the built App
- The internal Webview is opened on the ADFS Hub URL
(e.g. https://adfs.mycompany.com/adfs/ls/idpinitiatedsignon.aspx) - The user can now authenticate using any authentication method the hub URL requires, during the authorization session, the cookies and authorization token are received
- The Azure server redirects to the Success URI (e.g. https://successful-authentication-internal-url/portal.html) since the authorization succeeded.
- Appdome identifies the successful URI redirect and closes the internal Webview, thus returning the view to the original app
- Now, when the app tries to reach the protected resource, the authorization header or cookies are attached to the outgoing request. The gateway will trust these credentials and the app will reach the protected resource successfully.
How to Add ADFS SSO to Any Mobile App on Appdome
Follow these step-by-step instructions to add ADFS SSO to Any Mobile App:
Upload a Mobile App to Your Account
Please follow these steps to add a mobile app to your Appdome account.
If you don’t have an Appdome account, click here to create an account.
From the “Build” tab, Add ADFS SSO
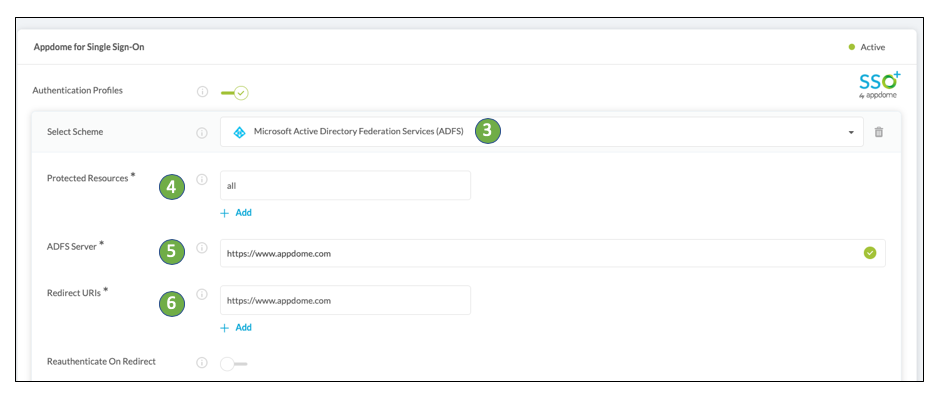
- Click the Build tab
- Click Authentication tab
- Click + Add profile and Select Scheme from the dropdown: Microsoft Active Directory Federation Services (ADFS)
- Type the ADFS Hub URL
- Type the Authentication Successful URI
- Type the Application Service URL Protected Resource
- Click Build My App
The technology behind Build My App has two major elements – (1) a microservice architecture filled with 1000s of code sets needed for mobile integrations, and (2) an adaptive code generation engine that can recognize the development environment, frameworks and methods in each app and match the app to the relevant code-sets needed to add ADFS SSO to the mobile app in seconds.
Congratulations! You now have a mobile app fully integrated with ADFS SSO.
Building Custom ADFS SSO Workflows In Android and iOS Apps
Building Single Sign-On inside Android and iOS apps involves several significant considerations. Perhaps the most significant consideration is “where” and “when” the Single Sign-On workflow will take place inside the app. Usually, an SSO workflow is initiated at the start of a login sequence. In this use case, the client and the server are built to handle the basic authentication sequence (User –> launches app –> enters credentials –> credentials verified by the server –> user issued a token or cookie allowing access to the app).
But, what if the app developer hasn’t or doesn’t want to build the app to support basic authentication? Or, what if the app developer wants more than the username and password provided in the basic authentication workflow (e.g., access to user details available in new authentication methods)? In these cases, Appdome-Threat Events provide a framework to pass user details contained in an OpenID and SAML authentication response to the app developer. This framework allows new flexibility to create custom SSO workflows inside an app using industry-standard methods to retrieve and pass user details between authentication services and mobile apps.
ADFS authentication services usually connect on the backend to a store of user data and use SAML or OpenID to handle authentication requests. Using SAML and OpenID, applications have access to all the user and authentication details returned by the server backend (i.e. any data the backend implements).
Read this KB article to learn more.
Prerequisites for using Appdome for ADFS SSO
In order to use Appdome’s no code implementation of ADFS SSO on Appdome, you’ll need:
- Appdome account – IDEAL or Higher.
- Mobile App (.ipa for iOS, or .apk or .aab for Android)
- ADFS Login (Hub) URL
- Authentication Successful URI
- Signing Credentials (e.g., signing certificates and provisioning profile)
No Coding Dependency
How to Sign & Publish Secured Mobile Apps Built on Appdome
After successfully building your app using Appdome, there are several available options to complete your project, depending on your app lifecycle or workflow. These include:
- Signing Secure iOS and Android apps
- Customizing, Configuring & Branding Secure Mobile Apps
- Deploying/Publishing Secure mobile apps to Public or Private app stores
Or, see this quick reference Releasing Secured Android & iOS Apps built on Appdome.
How to Learn More
Check out Appdome for SSO+ blog or request a demo at any time.
If you have any questions, please send them our way at support@appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project. If you don’t already have an account, you can sign up for free.
