How to Use Certificate Pinning in Enterprise Mobile Apps
Certificates are usually verified against intermediate CA certificates, which are then verified against root CA certificates. Root CA certificates are normally stored on a device’s trusted CA store. Certificate Pinning is the process in which an app stores specific certificates or public key hashes in the app itself, thereby foregoing the verification process as described above. Instead, the app verifies a server certificate or CA certificate it received directly against the stored certificate or public key hash. This knowledge base article details how to use certificate pinning in enterprise mobile apps.
How to Use Certificate Pinning in Enterprise Mobile Apps
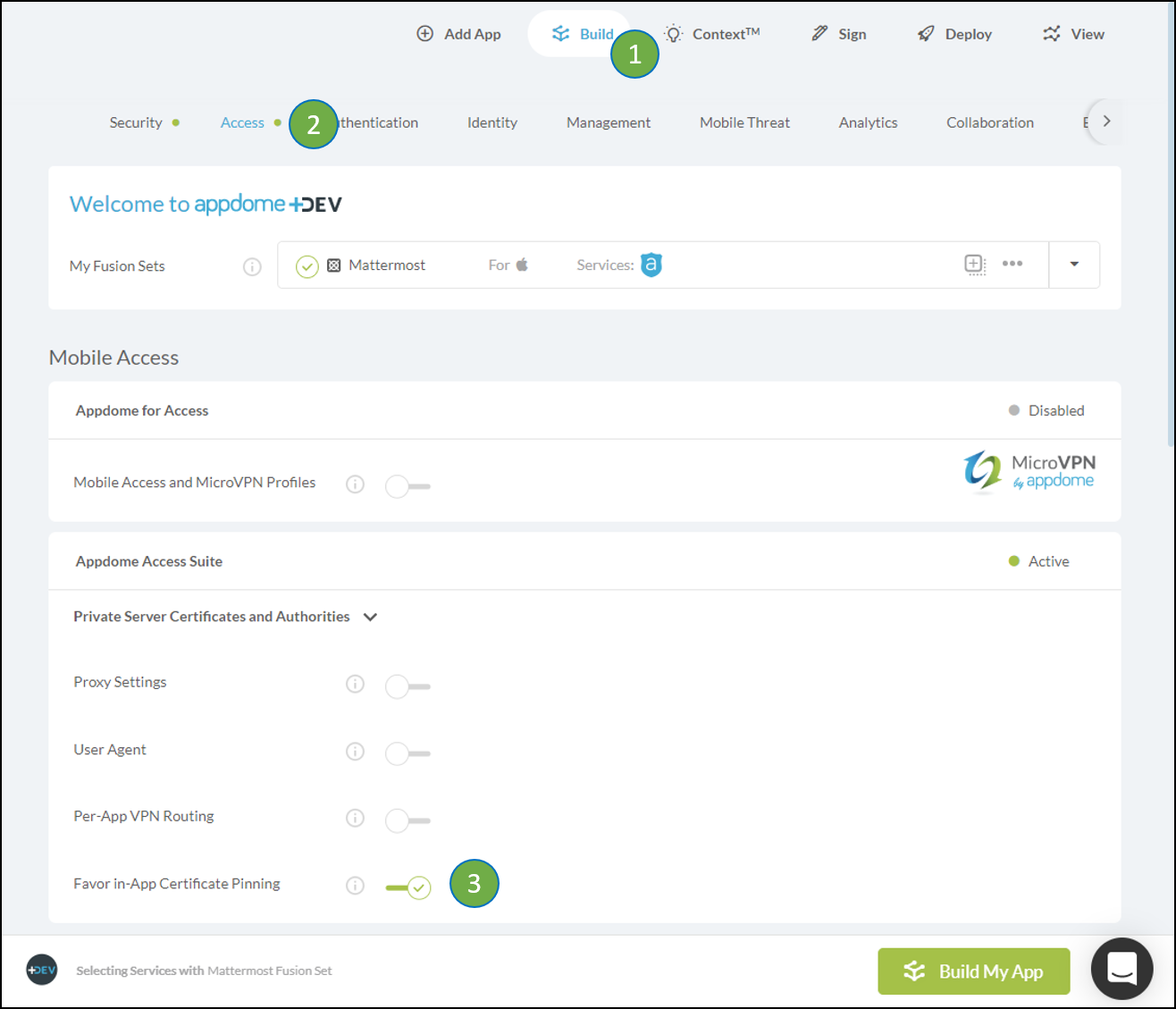
if your app uses an internal Certificate Pinning solution to trust the server, you will need to turn on “Favor Certificate Pinning”:
- Go to the Build Tab
- Select the Access menu
- Turn on Per-App VPN Routing
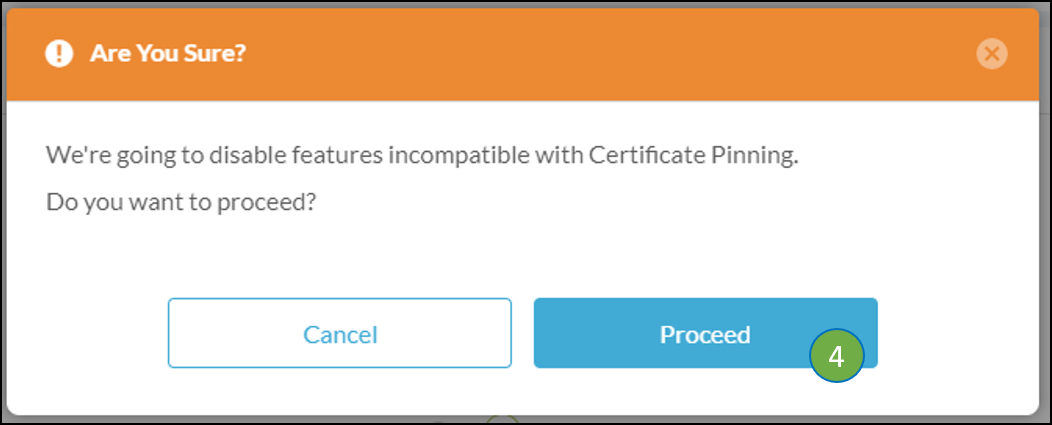
- You will see a warning message that other features are being disabled. Click Proceed.
Favor Certificate Pinning Compatibility
To allow Apple’s Per-App VPN to handle the traffic, some Appdome features will be turned off automatically, or an error will be displayed
Even though Per-App VPN may tunnel an app’s entire network connectivity, you are still able to secure your app by using complementary Appdome features such as:
- Enforce Strong RSA Signature
- Enforce Strong ECC Signature
- Enforce SHA256 Digest
- Enforce Certificate Roles
- Validating Basic Constraints for CA certificates
- Static Client Pinning and Certificate Pinning
- Authentication using NTLM or: Basic authentication, Digest, Ngotiate or an HTML form.
How Do I Learn More?
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project. If you don’t already have an account, you can sign up for free.
