My friend and co-creator at Appdome published a great blog about EventBot Malware. Avi’s blog covered the technical aspects of this new data harvesting attack as well as the protections mobile developers can use to stop this class of attack.
I want to cover what EventBot teaches us about the nature of hacking mobile apps in today’s mobile ecosystem. Perhaps the most interesting question here is this- “what does EventBot teach us about the business of Malware?” The answer to this question is critical to cybersecurity professionals who need to develop adequate strategies to guard against this threat class.
[Yep,] Anyone Can Be a Hacker
Security used to be akin to samurai warfare. First of all, it used to take a long time, specialized skills and lots of experience to become a hacker. Hackers would choose sides. A black hat hacker would step onto the virtual battlefield, while the defender would set up defenses to block the would-be attacker. These warriors would compete, using digital, network, application and security methods to battle and defend against each other. The number of true hackers, this line of thinking goes, was relatively small because of the time and effort it took to become a true hacker. And security professionals could take some comfort in the fact that such a small and elite group of real hackers might not have time or the desire to target their mobile app. True hackers have better things to do, right?
 Not so fast. Part of this story is true. There are great hackers out in the world. Security professionals have acknowledged for some time that elite hackers don’t operate alone. They operate in groups of elite hackers and are much more organized than ever. Today, the line between hacker and developer and, for that matter, a hacker and everyone else has disappeared. It is surprisingly and incredibly easy to become a hacker. Armed with a browser and Google, anyone can simply search “How to Hack an Android App” or “How to Hack an iOS App” and get 1000s of articles, videos, lessons, tools, etc. to do just that. I’ve added a few examples of videos and tools to make the point.
Not so fast. Part of this story is true. There are great hackers out in the world. Security professionals have acknowledged for some time that elite hackers don’t operate alone. They operate in groups of elite hackers and are much more organized than ever. Today, the line between hacker and developer and, for that matter, a hacker and everyone else has disappeared. It is surprisingly and incredibly easy to become a hacker. Armed with a browser and Google, anyone can simply search “How to Hack an Android App” or “How to Hack an iOS App” and get 1000s of articles, videos, lessons, tools, etc. to do just that. I’ve added a few examples of videos and tools to make the point.
We already know that crowdsource hacking services like BugCrowd emerged specifically to test the premise that hacking has, for some time actually, become a democratized and everyday undertaking. These platforms allow anyone with the desire and interest to hack apps for a living and to make a living doing just that. Going further, we also know that very popular, special-purpose tools like IDA, Hopper and Frida have emerged quickly to make the job of hacking extremely easy. These tools disassemble apps and reveal control flows, methods, file systems, and more with ease. Likewise, development environments have also gotten more robust. The same tools developers use to build, debug, troubleshoot and test apps, can be used to hack apps too. Bottom line, any developer can be a hacker and vice versa, and any person can become developer or hacker with ease. Armed with new tools, code samples and instructions, everyone and anyone can hack or become a samurai mobile app hacker.
Hackers Build Tools to Hack Mobile Apps at Scale
The biggest change in hacking for a living is how hackers attack and hack apps. While the individual battle between black hat attackers and white hat defenders continues, a new threat is emerging. This new breed of hackers don’t hack individual apps or networks. These hackers are building systems to hack apps at scale. With all the automated tools and instructions out there, the learning curve is simply too easy to climb. Hacking an individual app isn’t interesting. Building tools to hack a massive number of apps is.
The chart below can be applied to the modern world of mobile apps and offers the best illustration of what mobile app hackers do today. The chart was published some time ago by Johannes Wiik and Jose J. Gonzalez, Faculty of Engineering and Science Department of Information & Communication Technology Agder University College and Howard F. Lipson and Timothy J. Shimeall at the Software Engineering Institute at Carnegie Mellon University in their research on Dynamics of Vulnerability – Modeling the Life Cycle of Software Vulnerabilities.
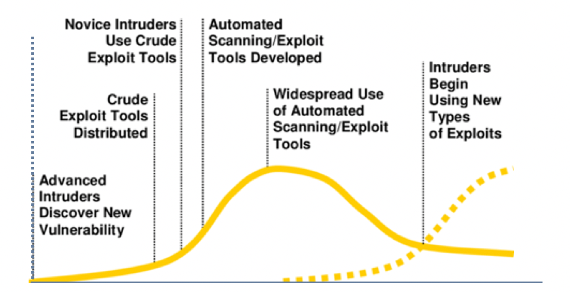
Using this example, assume for a moment that hackers begin as developers of systems that test and exploit large scale vulnerabilities across mobile apps. Consider too that, in this new world, the honor goes to the hacker who builds the best or most popular tool, long before it goes to the hacker who exploits a single app or network. For the cybersecurity professional, the nature of cyberwarfare is changing, from the functional equivalent of matched combat between elite swordsman to machine guns to biological weapons, incredibly fast. Scale is the driving factor, from the start, and you don’t need to be an expert to create the weapon.
[Oh My] How the Business of Malware Has Changed
Against this backdrop, consider a very malicious Mobile Banking Trojan – EventBot Malware. EventBot is a very straightforward program built on a simple premise: find unprotected data residing in mobile apps and steal it. EventBot doesn’t break security methods. It doesn’t overcome defenses. It does what a very smart developer would do: look for data that’s valuable and easy to get, build a minimum viable product, launch it fast, and iterate quickly.
As a student of security businesses, I have a completely different take on EventBot. To me, it looks a lot like a venture-funded business. Now, I don’t think any legitimate VC actually funded the creators of EventBot. But someone did. And while it’s totally interesting to learn how EventBot works, where and how it hides, what methods it uses to protect itself, how it gains new permissions, etc., what’s more interesting is watching how it evolves. Its developer clearly has a plan. If you study the evolution, you can see it. They are using a stepped and directional pattern to lay a beachhead for continuous and escalating exploits. For example, SMS interception wasn’t the first priority. Unprotected data was easier, so they started with that. And, the developers waited several versions before trying to obfuscate (hide) their malware. This is lean startup methodology at its best and 100% rational. The MVP has to be fast, not perfect. In a startup business, speed is key.
We can see that the creators of EventBot had financial gain and scale in mind. The first versions included 200 mobile banking, payment and cryptocurrency apps as its targets. There’s no magic here. Stolen credentials for mobile banking, payment, wallet and cryptocurrency services will likely fetch a pretty penny on the Dark Web. If EventBot did only that (sell stolen credentials on the Dark Web), I suspect their investors would be very happy. We also know that EventBot can update its target list remotely. So, the early list of 200 can easily be expanded to create an evergreen business, each time adding 200, 2000 or whatever number of mobile apps to the list. Looking at the list itself, it’s also clear that the builders of EventBot focused their attention on mobile banking and other fintech apps in geographies hardest hit by COVID-19. Of course, we see what I would call “tests” of the malicious program in other geographies too. Like a startup, the builders are “growth hacking,” and validating “product-market fit” in each geography.
Over time, I can envision “new versions” of EventBot that target different market segments and “white label” versions that can be sold to different criminal organizations, perhaps in different geographies. Each of these new versions will no doubt build on the lessons of the others or, and this is the really scary part, the developers will open-source their creation. Just as depicted in the graph above, they’ll unleash their tool to the world. Would-be hackers from everywhere will improve on it and take it in new directions constantly.
Defending Mobile in the New Age of [Automated] Malware
Defending a mobile business in this ‘build-malware-first’ world can’t be won at the network level. EventBot demonstrates how easy and effective a widely distributed data breach can be. EventBot aside, it’s an invitation for others to do the same thing. Right in front of our eyes, hackers are taking the quantum leap forward into writing programs to hack mobile apps before the defenders are doing the same to protect mobile apps. If hackers start with and prefer machines, and derivations of machines (ie: automation) to carry out their tasks and build businesses around breaking into mobile businesses, security teams are at a great disadvantage if they don’t also leverage automation.
Security teams are advised to think of the new breed of hackers as tool-building developers first, or entrepreneurs building mean startups to carry out data breaches, identity theft, mobile fraud and more. These mean startups leverage automation, build lightweight programs to move fast and iterate quickly. To properly defend mobile apps, businesses and users, security professionals need to think like the malicious machine builders in mean startups, using machines to parry and defend where the attackers are; not sit behind castles of network defenses waiting for the attacker to come to them. They don’t have to. As my colleague Avi said in his blog:
“Malicious hackers build code to exploit large scale, systemic, problems in mobile [businesses]. It might not be lucrative to hack an individual app. But, if your app is 1 of 200, 2,000 or 200,000 mobile apps that leave data, like usernames and passwords, in the clear, there will always be bad actors working to take advantage of that opportunity…There is no safety in large numbers. If your mobile app shares the same lack of protections as other apps, that fact gives malicious hackers a perfect reason to target your app.”
Because of this, the job of the security professional is changing too. Good security teams are moving from advisory to operational, embracing “machine culture” to present a unique security posture in mobile apps. These visionaries of mobile security think like hackers and target the weaknesses in the malware presented to them. They use machines to add security features that cause the malware machines to break, to process useless data, or fail to find the required methods for exfiltrating or connecting with your app. Top Security professionals understand if developers can write a program to find or extract “X” from your app, they can use technology too to block the path or protect the “X” quickly, prioritizing the use of machines (automation and tools) to improve speed and iteration in security implementations across the mobile app estate, allowing for rapid iteration of new security methods over time. In the new era of security, agility and speed are key.
I hope you find this blog helpful.
If you would like to know more about Appdome’s automated, no-code mobile app security solution, please visit our website, download the mobile app security summary or request a demo.





