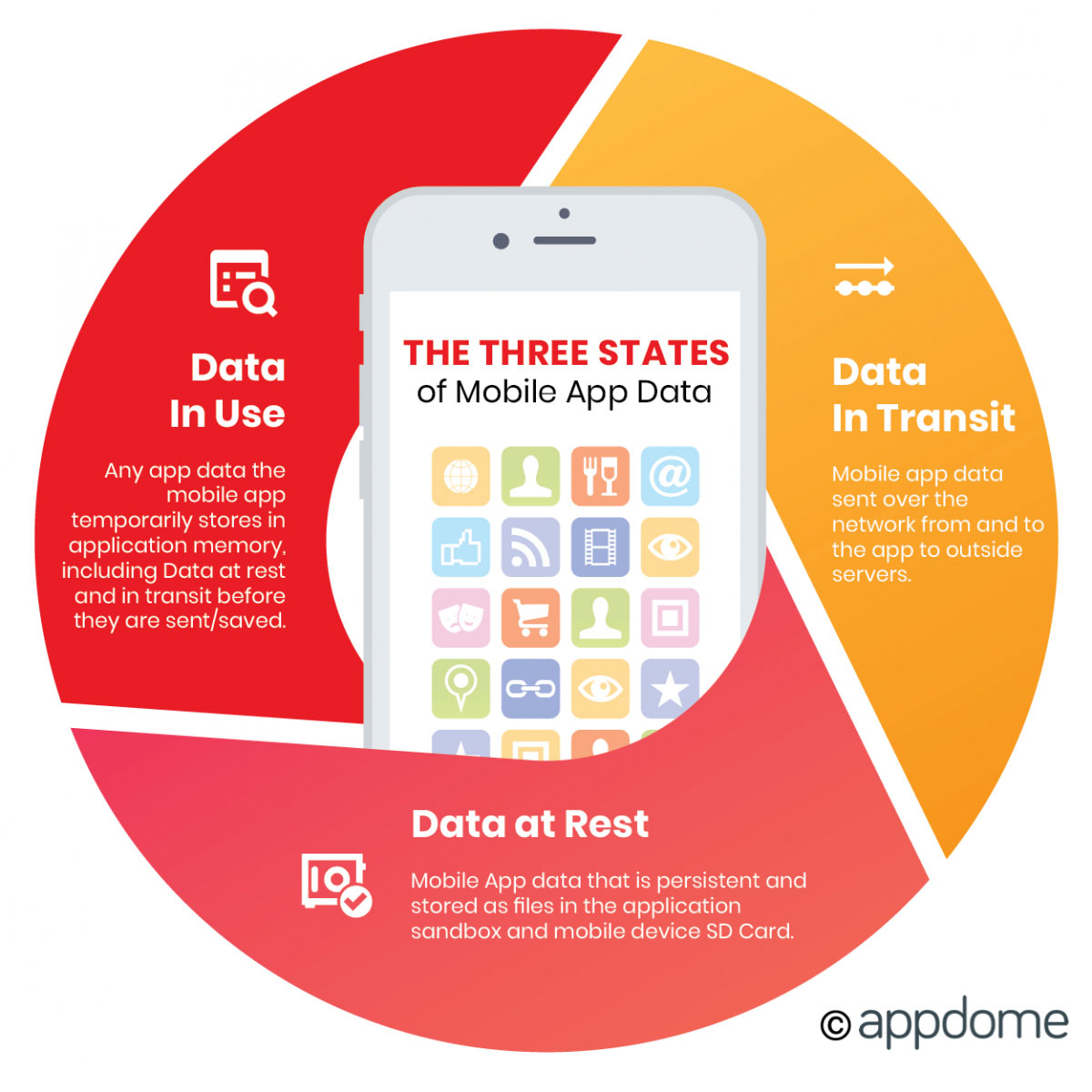
Every mobile app uses three states of digital data – data at rest, data in transit and data in use. Today, in a groundbreaking new addition to Appdome’s TOTALData Encryption lineup, Appdome can now help mobile developers and others encrypt all three states of mobile app data.
The Three States of Mobile App Data
Data at rest is mobile app data that is persistent and stored in the application sandbox.
Data in transit is mobile app data sent from the app to outside servers or other app users. In previous posts, we discussed Appdome’s ability to encrypt data at rest and enforce data in transit encryption in Android and iOS apps. Today, Appdome is adding mobile app data in use encryption (aka, ‘data in memory’).
Mobile App Data in Use
Mobile app data stored in memory is not persistent data. Instead, it is “data in use” or “transient data.” Some mistakenly think that it’s not necessary to protect this data state. However, data in use can be anything. From user credentials, encryption keys, and authentication tokens to personally identifiable information (PII), all mobile app data at some point or another exists in memory. For example, before mobile app data is written to the application sandbox or encrypted at rest, it exists in memory. When a mobile app retrieves data from the application sandbox, it temporarily stores it in application memory. Likewise, in sending mobile app data from the app to anywhere in the world, the first step is placing the data in memory. Mobile data in use is everything, at any point in time.
Android and iOS Don’t Offer Data in Use Encryption
Inside native and non-native Android and iOS mobile apps, encrypting data in use is equally critical to protecting data at rest and data in transit. Imagine your developers have done a great job adding data at rest and data in transit encryption to your mobile app. But, a crafty hacker discovers a way to infiltrate and dump your in-app memory data. That hacker could harvest a treasure trove of critical information about your users, your environment and your network. While iOS provides some methods to protect data in use, it does so for specific types of data only. For example, iOS provides security for authentication credentials via the Keychain. However, not all in-memory data is protected via the Keychain. Likewise, Android (to date) does not protect data in use. Android offers developers options for data at rest and data in transit encryption.
Even mobile browsers, web apps, and progressive web apps all utilize data in use. These mobile applications make extensive use of the application cache, filling it with data from previous functions and duplicates of data stored elsewhere. In-memory data in these applications is used to ensure the optimal performance of a mobile app. In other words, ensuring that mobile app data or a user’s login and preference settings can be loaded quickly. Without protection, it’s a treasure trove of unprotected, critical data about your users, your network, and your business.
Appdome’s Data in Use Encryption Solution
At this point you might be asking, if it’s so critical why hasn’t anyone stepped forward to provide data in use encryption for mobile apps until now? The answer: performance. Encryption is, by its nature, a process-intensive function inside a mobile app. To build encryption into mobile apps from scratch takes a lot of work by highly specialized developers. Doing it correctly takes gobs of mobile development. Appdome already simplified data at rest and data in transit use encryption for all users. Using Appdome, developers and others can apply encryption to data in use with extremely minimal impact on mobile app performance.
To truly protect data in use, you have to go beyond traditional encryption methods. To get there, it is important to remember that in-memory data includes all data and, therefore, all “reads and writes” of that data. The number of encrypt-decrypt events needed to protect data at rest and data in transit is a fraction of what’s needed to properly encrypt data in use. Furthermore, how a mobile application processes the encryption and decryption of in-memory data in a mobile app has to be handled differently than other states of data. Our discovery on the path to data in use encryption is what we call Dynamic Memory Segmentation. Dynamic Memory Segmentation refers to the ability of an app to break apart in-memory data and infer which elements of data need to be accessed more often, or when, and during what processes.
Appdome gave the mobile app the ability to encrypt and decrypt the right data at the right time. We also gave the mobile app the ability to learn from experience. This learning allows the app to maintain the optimal encryption model based on the design, data, and “read and write” capabilities in the app. This allows an Appdome-Built app to adjust the encryption model on the fly inside the Appdome framework and achieve optimal in-memory encryption.
360-Degree Mobile App Data Protection
There is no limit on the class of data that can be protected in memory. Appdome users have the same control over which data, files, data classes, and more are encrypted, and which are not. With the addition of encrypting in-memory data, all digital data “states” are protected inside the mobile app; data at rest, data in transit and data in use. As part of Appdome TOTALData Encryption, data in use encryption offers organizations and app developers 360-degree protection for mobile app data.
Data in use encryption is available as part of TOTALData™ Encryption to users with Appdome-DEV accounts only. We look forward to hearing your feedback and, of course, giving Appdome in-memory data encryption a try!





