Here at Appdome, we’ve seen a rise in cyber-criminals creating and using screen overlay attacks against mobile apps to commit mobile fraud. On-device malware and mobile fraud have grown to become two of the biggest threats on the mind of mobile consumers. In Appdome’s Global Mobile Consumer survey about mobile app security expectations, mobile fraud took the #1 spot as the biggest fear on the minds of consumers, and malware shot up 121% to take the #2 spot. The best defense against mobile fraud is to prevent it from occurring in the first place. This blog will discuss how overlay attacks work and what mobile developers and cyber professionals can do to detect and defeat overlay attacks.
What is a Screen Overlay Attack?
An overlay attack (aka: screen overlay) is an attack technique in which part of the application screen is covered by a fake (malicious) screen that the user is tricked into clicking on or interacting with. There are a huge number of variants of overlay attacks, but in all overlay attacks the user thinks they are interacting with a legitimate app or service, but they are actually interacting with the overlay screen controlled by the attacker. The classic example of this type of attack is the Cloak & Dagger type of attack. More recent variants include Strandhogg and many others.
Common Screen Overlay Attacks
While the technical methods of achieving an overlay attack vary widely, all most overlay attacks fall into one of the following 3 buckets, each of which is driven by a different motivation on the part of the attacker:
1. Data Harvesting, Input Capture Attack
Data Harvesting or Input Capture Attack is a technique used by an attacker to access and retrieve PII, transaction or other sensitive or valuable data when the user interacts with an exploited mobile app. This can be accomplished by covering part or all of a mobile app screen with a fake screen controlled by the attacker. In this variant, an overlay of a fake screen could transparently cover part or all of the real screen, hide the real screen from the user’s view, or interrupt the mobile app’s workflow, asking the victim to enter information (usually sensitive info like usernames, passwords, pin codes, or answers to “security questions”). The victim thinks they are entering their information into the legitimate mobile app, but in reality, they are entering data into the malicious overlay screen which is under the attacker’s control. Such input harvesting techniques are commonly used by cybercriminals in synthetic ID fraud campaigns to compromise mobile banking, fintech, eWallets, and cryptocurrency apps. When these types of attacks are successful, they may adversely impact Know Your Customer (KYC) compliance efforts, which often require financial institutions to verify customer identities and prove the legitimacy of their users. Because harvested data is often used by attackers to impersonate or masquerade as legitimate mobile users, it behooves organizations to invest in automated ways to prevent such abuse.
2. Mobile Malware Delivery
In other variants of screen overlay attacks, the attacker may not be after information. The attacker might instead want the user to install or enable malware on the device. To make this easier to achieve, attackers often trick users into enabling otherwise legitimate Android functions like Accessibility Services or installing apps from an unknown source. For example, the attacker might present a fake screen with the logo of the exploited app and trick the user into enabling Accessibility Services or Unknown Sources, which are legitimate mobile app functions that the attacker can abuse by using them as an unmonitored pathway to deliver malware to the mobile device. Once either Android feature is enabled, it stays enabled until the user explicitly turns it off. Or the attacker might trick the user into approving mobile app permissions which the malware will then abuse for its own purposes.
3. Mobile Privilege Escalation & Permission Abuse
Attackers can also escalate privileges by tricking users into approving dangerous “app permissions” that the malware app seeks to abuse. With an overlay attack, the user thinks she is approving the permission for the legitimate app but in reality, it is needed and used by the malware app. The permissions granted can be anything the mobile device allows, such as access to the camera, location, microphone, contact lists, SMS, and much more. Once granted, these permissions can be used by a malicious app running in the background. Sometimes the malicious fake app hijacks the real app and pushes itself into the foreground, (by abusing Android tasks in an attack method known as “task hijacking”). It then impersonates the real app and requests permissions from the user. If the user approves the permissions, the permissions can be used by the malware to launch other attacks.
Recent examples of overlay malware discovered by security researchers have used different combinations of attack methods. One such example is an overlay attack whereby users are tricked into installing malware that presents itself as a mandatory security patch that the user must install. In the screenshot below, the user thinks they are clicking ‘Continue’ to install a security patch. But in reality, they are really clicking an ‘Activate’ button (hidden underneath the fake screen overlay) which activates the malware and grants it administrative privileges, which the attacker can then use to (1) lock the user out of their device by changing the passcode and (2) encrypt and/or delete the user’s data. This is a perfect setup for a ransomware attack. 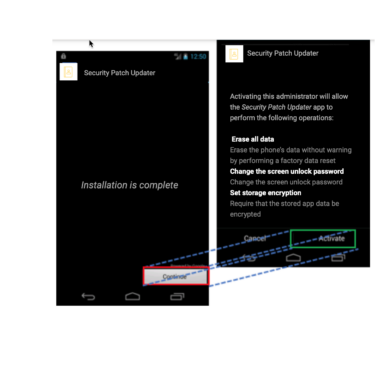
Can API 31 Stop Overlay Attacks?
With Android API 31 (Android 12), Google released a feature to protect mobile apps against overlay attacks. The good news is that using this feature will prevent non-system overlays from obscuring in-app views on recent Android versions. However, to use this feature, the developer of the relevant component must use API 31 (not earlier) and call the method “setHideOverlayWindows(true)” on each activity view to be protected. This makes protecting specific Android activity views tedious and hard to manage, specifically since some of the sensitive workflows are not controlled explicitly by the developer. And, the method itself is not tamper resistant. By itself, the methods can be bypassed using any standard mobile app pen testing or dynamic hacking tool such as Frida or Magisk, which means malware can do the same.
How Does Appdome Stop Overlay Attacks?
Inside Appdome’s automated no-code unified defense automation platform we offer a Mobile Fraud Prevention solution that includes an advanced defense to Block App Overlay Attacks. This offers mobile app developers and cyber professionals a quick, easy, no-code and automated way to stop overlay attacks and mobile fraud at the source, inside the protected mobile app. Appdome’s Block App Overlay Attacks provides all the protection of API 31 across all Android API levels and an active threat-detection method to ward off tampering, injection, hooking and swizzling the defense. Enforcement against overlay attacks can be combined with Threat Scores, ThreatScope, Agentless Mobile XDR threat monitoring and intelligence as well as Threat-Events, advanced UX/UI intelligence and control. Everything is fully automated in the mobile DevOps CI/CD pipeline, eliminating work, complexity and time to defeat overlay attacks.
If you want to learn more about using Appdome to Block App Overlay Attacks, request a demo today.
*note: the Android ‘Allow Unknown Sources’ feature may have a different name depending on the version or device manufacturer.





