Enterprises and government agencies struggle with giving their employees secure mobile access to resources behind a firewall. Virtual Private Networks (VPN) are well established for giving employees secure remote access from desktop computers and laptops. The landscape is more complicated with regards to access from mobile apps. Enterprise mobile VPN options include always-on, on-demand, per-app and in-app VPN. However, there are some situations where a VPN is either not practical or not an option at all.
For example, most Enterprise Mobile VPN solutions require users to either install a separate VPN app or take some other action before they can access the resources. This introduces end-user friction. Also, most mobile apps are not built to reach VPN gateways out of the box. This functionality (if even possible) needs to be coded in the app, either by implementing an SDK or a management profile. Once the mobile app can launch a VPN tunnel, that tunnel needs to connect to a VPN gateway, and a physical box that has to be installed somewhere in the edge of the enterprise network and integrated with the rest of the network. This introduces more management complexity. Finally, VPNs are also vulnerable to attacks, giving hackers an entry point into the network.
In this blog I will review how remote employees, contractors, distributors, and suppliers can use mobile apps to securely access protected/gated resources (for example, resources protected by a corporate firewall) without the need for a VPN.
Solution: TLS with Mobile Client Certificates
One way to provide secure mobile access to a protected host behind a firewall is a combination of enforcing TLS together with mobile client certificates. The former ensures that the data is encrypted while in transit, and the latter is used to prove that the client/app is legitimate and has not been compromised. Before diving into the solution, let’s discuss each of those technologies just to level-set on some definitions.
What is TLS?
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a public network. For internet traffic, TLS is what ensures the “S” in HTTPS. TLS replaces the now deprecated Secure Sockets Layer (SSL) standard. There have also been several updates to the TLS protocol since it was first defined in 1999. These updates addressed vulnerabilities in SSL and in the early versions of TLS. The current version is TLS 1.3 and all secure network connections should use this latest version. Unfortunately, this is not always the case, which opens a door for hackers. One example is a TLS downgrade attack, where a hacker is able to negotiate the use of a lower version of TLS so that they can take advantage of known vulnerabilities.
What is a Mobile Client Certificate?
Mobile Client Certificates are used by the mobile application to prove its identity and authenticity to the server. The primary use case for this feature is to protect the mobile backend from compromised endpoints such as malicious bots, but in this case the client certificate validates that the connection is coming from a trusted mobile application. Therefore, the connection request should be allowed to pass through the web application firewall (WAF) and connect to the protected host. The trusted client certificates are stored (and should be stored securely) inside the mobile app. For every connection, the application presents its certificate along with a unique password/secret to the WAF for inspection and validation. By only allowing connections from apps whose client certificates it can validate, the WAF can block any unauthorized access to the protected host.
Enforcing TLS with Mobile Client Certificates
Enforcing the latest version of TLS together with mobile client certificates address 2 different and equally important things:
- Enforcing the use of the latest version of TLS, ensures that the payload is protected and cannot be read when intercepted.
- Using mobile client certificates, the WAF validates that the mobile app is a legit app and is allowed to connect to the protected host.
Both solutions are required. Using mobile client certificates with an old version of SSL or TLS (or worse over a non-secured connection) might allow a hacker to hijack the session using a Man-in-the-Middle attack. This might enable the attacker to do all sorts of malicious things, like read/modify/harvest the data being sent across the connection or steal the mobile client certificate. This will allow the hacker to masquerade as a trusted client and launch an attack on the backend.
Building Apps with TLS and Mobile Client Certificates
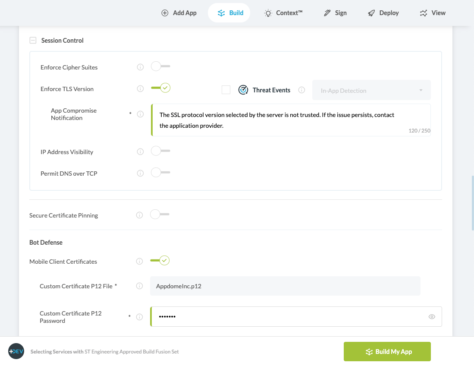
Appdome makes building apps that enforce the use of the latest version of TLS together with the use of Mobile Client Certificates easy (both security features can be built into any iOS or Android apps without any coding). Under the Secure Communications tab in Appdome, toggle on Enforce TLS Version and then add the specific p12 mobile client certificate. Network administrators can create the p12 certificate that the WAF needs to validate the app. Simply click Build my App and that’s it. Distribute your Appdome-secured app via a private or public app store.
Next, work with your DevOps team to configure your WAF to look for the p12 certificate to validate the connection request and allow the app to connect to the protected host.
The Advantage of Using TLS with Mobile Client Certificates
Thus, combining TLS enforcement with Mobile Client Certificates, achieves the same security outcome that a VPN would achieve, can be deployed universally (no app dependencies) and comes without any extra hardware or software components, or the compatibility/inflexibility issues inherent in an Enterprise mobile VPN.
To learn more: download the secure commutations datasheet, start a free trial or request a demo.