Ransomware attacks on the healthcare industry skyrocketed in 2020, having almost doubled compared to 2019. A 2021 study from Health and Human Services estimates that ransomware attacks were responsible for almost 50% of all healthcare breaches in 2020. These attacks can take down IT systems, prevent patients from accessing their medical records and even put patient’s lives at risk. In the United States alone, estimates put the number of Personal Health Information (PHI) records of patients affected by ransomware at over 18M and the average ransom demand per attack around $170,000. HIPAA Journal estimated in 2020 that ransomware attacks against U.S. healthcare providers have caused over $157 million in losses since 2016.
Ransomware is One of the Top 2022 Cybersecurity Trends in Healthcare
The Pandemic has increased the dependency on mobile phones in every industry segment, including healthcare. In fact, According to MobiusMD, there are over 350,000 mHealth apps available in major app stores and 30% of all smartphone users in the United States use an mHealth app at least once a month. And with the increase in use of mobile devices and mobile apps for healthcare related use, comes a higher risk of ransomware attacks. Doing a Google search on “healthcare ransomware trends 2022” is very telling. For example; Security Mentor lists ransomware as one of its top cyber threats and risks facing the healthcare sector in 2022. And the Journal of mHealth calls out ransomware attacks as an existential threat to healthcare organizations in its Cyber Security in 2022 overview. Furthermore, Kasperky notes in the dangers of “connected” healthcare: predictions for 2022 that “Telemedicine will continue to evolving. This means more applications for doctor consultations and patient health monitoring will appear, and cybercriminals will have the opportunity to discover security holes in a whole slew of new applications created by developers who have never made this kind of products before. What is more, malicious counterfeits of telehealth apps will most likely appear in app stores: fake apps that will imitate the real thing and promise to deliver the same functionality.” And we’ve discussed in several previous blogs that fake and malicious apps are most likely used as the delivery vehicle (trojan) for malware and ransomware.
What Are Ransomware Attacks?
 Ransomware is a type of malware where cybercriminals capture a victim’s data and either (1) cut off access to that data by encrypting it and demand a payment to give it back or (2) steal data and threaten to release it to the public unless they pay. It is ALWAYS about extortion.
Ransomware is a type of malware where cybercriminals capture a victim’s data and either (1) cut off access to that data by encrypting it and demand a payment to give it back or (2) steal data and threaten to release it to the public unless they pay. It is ALWAYS about extortion.
Ransomware attacks usually occur over longer periods of time, usually as part of an organized and concerted effort. They are not a one-time interaction, but rather a long term, multi-touch, multi-actor campaign that is abusing normal human, system and app behavior. Health related ransomware attacks can be conducted against healthcare organizations and individual patients.
Ransomware Attacks on Healthcare Organizations
Healthcare records are a lot more valuable to cybercriminals than other personally identifiable information (PII). According to a recent Trustware report, on the dark web, they are worth up to $250 per record vs $5.40 for a credit card number. It is no surprise then, that ransomware attacks on healthcare organizations are skyrocketing.
Mobile apps are the weak links in ransomware attacks on healthcare organizations. In a previous blog, we made a point that most healthcare apps lack security and discussed the top threats to mHealth apps. In order for a mobile app to connect to a mobile backend, that apps contain very valuable network information such as SSL certificates, API information, server addresses, usernames and passwords. When this network data is not adequately protected, it is relatively easy for a bad actor to harvest all this data and abuse it to gain unauthorized access to a hospital or healthcare organization’s backend servers. Once in, these fraudsters can install malware to be used in a ransomware attack. And ransomware criminal organizations such as Avaddon, Conti and REvil are regularly targeting healthcare organizations.
Ransomware Attacks on Individual Patients
Direct ransomware attacks on patients are a much less publicized problem, largely in part because breaches are only published by the US Dept of Health and Human Services (HHS) if they affect over 500 people and therefore attacks on individual patients are rarely publicly disclosed.
But the impact of ransomware can be really devastating to patients. Healthcare apps store our most private information, which is why it is governed by data protection and privacy regulations such as HIPAA in the USA, GDPR in the EU, Data Protection Act in the UK, and PIPEDA in Canada.
In my discussions with Appdome customers around the world, among the biggest threats they see are mobile phishing attacks, which abuse both human and app vulnerabilities.
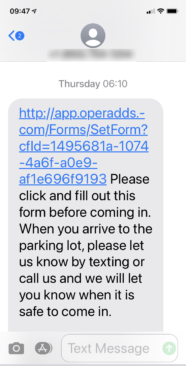 For example, I recently got a text from my dentist to confirm an upcoming visit. To me this looked like a textbook phishing attempt. The link was not a secure link (flag #1); the URL had no reference to my dentist (flag #2) and the message was relatively generic (flag #3). I did not click on the link, but I can see how other people may click on it.
For example, I recently got a text from my dentist to confirm an upcoming visit. To me this looked like a textbook phishing attempt. The link was not a secure link (flag #1); the URL had no reference to my dentist (flag #2) and the message was relatively generic (flag #3). I did not click on the link, but I can see how other people may click on it.
But what could happen if this text message was a malicious phishing attempt? Once a patient clicks the link, it might present the patient with a fake login window allowing the fraudster to capture the username and password for the patient. Or clicking the link might install a malicious app masquerading as a scheduling or check-in app for example. After the app is installed, the patient may be prompted to grant access to calendar, contacts, location information and more. An unsuspecting patient might think that this is a reasonable request for that kind of app and grant the app the permissions the fraudster needs to install malware on the device. Once the malware has been installed, it can scan for healthcare apps already installed on the patient’s device and launch an attack on the unsecured mHealth app. Once the fraudster is successful with their attack, they can launch the ransomware attack on the patient.
This is just one of the many scenarios that would give a fraudster access to patient PHI records and lead to a ransomware attack.
How to Prevent Ransomware Attacks via Mobile Health Apps
Health and wellness organizations can preempt ransomware attacks originating from their mHealth apps by securing their mobile apps with Appdome. Specifically, they can add the following protections in 30 seconds or less without code or coding:
- Encrypt all the data inside the app to comply with different healthcare and data privacy regulations such as HIPAA, GDPR, Data Protection Act and PIPEDA. Health and wellness app makers need protect and secure all patient records with AES-256 data-at-rest at rest encryption.
- Shield the health app and protect it from debugging, tampering or reverse-engineering attempts.
- Obfuscate the code of the app so that fraudsters cannot understand how the app works and use that knowledge to launch their ransomware attacks.
- Prevent the app from running on an untrusted device, typically devices where the operating system has been compromised (aka Jailbroken/Rooted devices).
- Protect the app against network-based attacks and ensure that the connection between the mHealth app and the back-end servers does not get compromised.
- Add FaceID and TouchID to prevent unauthorized access.
- Protect the mHealth apps against automated attacks that interact with the mobile app in a fraudulent way or that use the app in a fraudulent way.
- Protect the app against local, on-device, attacks meant to harm the application or/and its users.
- Prevent the health and wellness app from becoming a trojan and stop fraudsters from creating fakes and mods or from resigning and redistributing the app.
Read the Mobile Healthcare case study to learn more or start a free trial of Appdome today.





