Tom Tovar, Appdome’s co-creator, published a great byline in DarkReading: Man-in-the-Middle Attacks: A Growing but Preventable Mobile Threat. This blog elaborates more on how to prevent mobile MitM attacks. This blog is intended for anybody looking to broaden their mobile security knowledge.
What Are Mobile MitM Attacks?
Man-in-the-Middle attacks are a popular method for hackers to get between a sender and a receiver. In other words, somebody is trying to intercept the communications between a mobile user and the server the user is connecting to. Because the are invisible and inexpensive to mount, Man-in-the-Middle attacks are one of the most dangerous network threats out there. The 2020 Verizon Mobile Security Index (MSI) states that “MitM attacks are often done through rogue access points, which take advantage of familiar and trusted public Wi-Fi names (SSIDs). Users may see the name of a legitimate company or brand and connect to it without a second thought. While some rogue hotspot names are obviously misspelled (e.g., Starbuckz), many look perfectly legitimate. And users might have the access point already stored in their device, causing it to connect automatically. That might sound like something out of a spy movie, but it’s more prevalent than SQL injection (SQLi)-type attacks, and almost as common as phishing—but it gets far less press; maybe it needs a better agent?”
Our key findings from the Verizon Mobile Security Index blog list a good number of stats on how prevalent mobile MitM attacks are. But the one that I find the most telling is that 55% enterprise users who know that public Wi-Fi is prohibited use it anyway for the sake of convenience. And ironically, that includes many who are responsible for managing the security of mobile devices. In fact the FBI’s advice is clear: “Don’t allow your phone, computer, tablet or other devices to auto-connect to a free wireless network while you are away from home. This is an open invitation for bad actors to access your device. They can load malware, steal your passwords and PINs, or even take remote control of your contacts and camera.”
How to Prevent Mobile MitM Attacks?
The barrier of entry for a cybercriminal looking to launch a Man-in-the-Middle attack is very low. For $109, you can get a WiFi pineapple (no I won’t link to it from this blog) and set up a rogue access point. This allows the criminal to passively view and log all the traffic that goes through their hotspot and spy on communications, steal username and passwords and other sensitive data. There are several more advanced MitM attacks and Tom reviews these in his DarkReading byline.
So how can a developer prevent a MiTM attack on this app and protect their end-users from the malicious intent of the hacker? They essentially have 2 options. Manually code man-in-the-middle protection in their app or use Appdome to add MitM prevention to their apps without code or coding. To quote one of our key engineers, Appdome’s MitM prevention goes beyond where other MitM protections leave off.
Trusted Session Inspection
At the core of Appdome’s MitM Prevention lies Trusted Session Inspection, Appdome’s proprietary mechanism that Appdome first introduces during the initial SSL handshake, to prevent attackers from gaining control over the session before the TLS handshake completes. When the application starts the SSL Handshake with the server, Appdome’s Trusted Session technology inspects the traffic for anything that looks suspicious. When triggered, the Trusted Session will automatically notify the user of the compromise and drop the connection. The message displayed to the user can be customized.
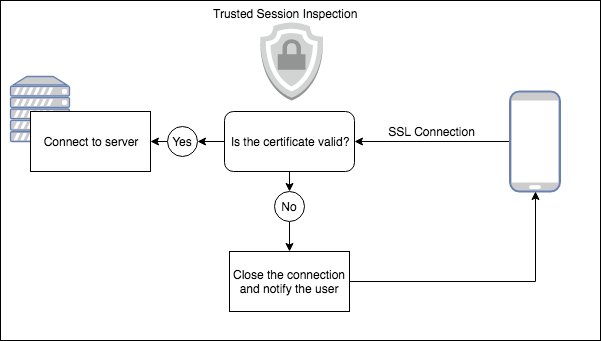
The top two protections that Trusted Session Inspection adds to the app are Preventing MitM Attacks and Detection Malicious Proxies.
- An Appdome protected app prevents MitM attacks by validating the authenticity of the SSL certificate used by the destination server. This protects the application from connecting to untrusted, unknown, or malicious destinations or websites.
- Appdome protected apps also detect and prevent MitM attacks on the application by preventing connections to unknown, untrusted or malicious proxies or other intermediary devices.
And if this was not enough, Appdome MitM Prevention comes with several advanced capabilities that make MitM attacks virtually impossible.
To learn more, download the datasheet, and if you are ready to start protecting your apps now, create your Appdome account now. We’ll get you going in no time.





