Earlier this year and in light of the Russia-Ukraine War, U.S. and government agencies from countries around the world issued cyber-defense advisories. CISA and FBI published an advisory warning organizations to protect from destructive malware. These advisories describe malware known as WhisperGate was used to target Ukraine organizations and render targeted devices inoperable. WhisperGate displays a fake ransomware note and encrypts files based on certain file extensions, corrupting a system’s master boot record. In addition to this destructive malware, REvil ransomware has led to turmoil in organizations across industries around the world. Behind the REvil ransomware is the REvil gang, who has demanded over $80M in payment for attacks on organizations including:
- Gas pipeline Colonial Pipeline
- Meat processor JBS
- Remote network management software provider Kaseya
As a result, many companies may be focused on protecting computer systems and backend servers like those attacked by REvil, WhisperGate or other malware. Mobile apps can be the weak link, enabling hackers and fraudsters to do widespread damage for a couple of reasons:
- Mobile apps often do not have adequate protections, enabling hackers to obtain critical information used in back-end attacks.
- Mobile apps themselves are often the targets of malware
If you already know what ransomware is, you can skip to the next section. If you don’t, read on! Ransomware is a type of malware where cybercriminals capture a victim’s data and either threaten to publish the data or encrypt/destroy it unless a ransom is paid, usually via cryptocurrencies. Ransomware attacks usually occur over long periods of time. Its creators also blend multiple attack vectors, techniques and methods in order to create the perfect climate to maximize the effect of their ransomware (and thus maximize their profit or ROI).
Mobile Apps Are the Weak Links in Back-End Attacks
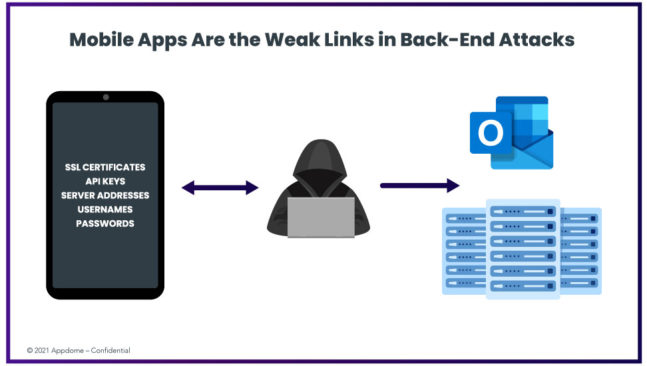
In reality, ransomware hackers use multiple sources to get the information they need to attack. These sources include mobile apps, an easier source to break into to get SSL certificates, server addresses, API keys, usernames, passwords that are then used to attack back-end servers.
Many Mobile Apps Expose More Information Than Necessary
Mobile apps expose more information than necessary in API calls to the app’s backend. For example, 3FUN, an online dating app that exposed too much information in an API call which exposed PII and highly confidential personal information about users, profile info, location, and chat history. Using this information hackers and fraudsters can blackmail or get users to reveal other information used to launch ransomware attacks.
In addition to API calls, passwords stored in the cloud are also used by ransomware attackers to elevate permissions for themselves and make changes to apps. How does this work?
To make mobile apps usable, most apps store passwords, cookies or access tokens for extended periods of time. If an attacker gets access to your Apple ID they can use it to create an iCloud account which can then be used to lock any associated Apple devices remotely or make system level changes.
The malicious code that actually makes the system level changes required to make the ransomware attack effective often makes its way onto mobile devices disguises inside legitimate looking version of apps (called clones). We’ll discuss this in more detail in our next section on how mobile apps themselves are targets for ransomware attackers.
Mobile Apps Themselves Are Targets for Ransomware Attackers
In addition to being the weak links in backend attacks mobile apps themselves are targets for Ransomware. Here are the top two ways ransomware targets mobile:
Fake Apps and Clones Posted on Public App Stores
Ransomware attacks are typically carried out using a Trojan disguised as a legitimate file or program that the user is tricked into downloading or opening. Crypto mining Malware enables attackers to covertly execute calculations on a victim’s device – allowing them to generate cryptocurrency. Crypto mining is often conducted through Trojan code that is hidden in legitimate-looking apps. Other malware include: Tiny Banker, xHelper, Triada, and Hiddad.
Static and Dynamic Analysis
Long before the ransomware attack occurs, cybercriminals will have done a ton of research to understand how a mobile app functions (by running it and interacting with it) or by reading the source code in an effort to understand how the app works. From there, they can find weak points to exploit (for example weak or no encryption). Using dynamic instrumentation tools, fraudsters are able to grant elevated permissions to themselves.
What You Can Do to Prevent Ransomware Attacking Mobile Apps?
The Duty to Protect Has Shifted
While individual users can educate themselves and watch out for signs of ransomware attackers, it is hard for individuals to do as the signs are constantly changing as attackers evolve. At the same time, app makers are now– more than ever– expected to secure mobile apps. In a global survey of over 10,000 mobile consumers around the worldAppdome Releases 2021 Global Mobile Consumer Security Survey , over 72% of consumers said they’d abandon apps if the apps did not protect their data or were breached/hacked. In the same survey, mobile malware is the biggest concern, above man-in-the-middle attacks and compromised credentials.
Build Advanced Security into DevOps with Appdome’s Mobile Malware Prevention
With Appdome, mobile app makers can add mobile malware prevention into their apps and the software development process directly. Existing solutions focused on scanning, detection and response—not prevention, where the greatest impact is. But taking Appdome’s approach of combining mobile app security and fraud prevention, app makers have a solution that is:
1. Comprehensive
Appdome prevents mobile apps from being weaponized to conduct attacks on other apps or users. Appdome prevents mobile malware from sneaking onto devices through clones, fakes, or mods (replicas of popular or useful apps, which contain malware embedded inside).
Appdome also prevents the abuse of highly privileged services like AccessibilityServices, as well as abuse of app permissions that enable fraudsters to take control over devices or apps remotely, or to inject/alter touch events. Appdome prevents key injection by blocking several methods attackers use to inject keys or touch events (Appdome blocks keylogging, malicious keyboards, and also blocks the use of ADB to establish a remote shell access to apps or devices). Appdome-secured apps can detect if other malicious apps are running on the device with out of context app permissions, or with AccessibilityServices enabled for apps that run in the background.
2. Automated
With Appdome, organizations can automate the process of protecting from ransomware attacks targeting mobile apps. They can also Appdome to automate the process of preventing ransomware attackers using mobile apps to get information used in backend ransomware attacks. Instead of waiting until the end of app development, you can code in mobile malware prevention and data protection at any time in your development process with a few simple clicks. No need to code. No SDK.
3. Has Best Practices Baked into DevOps and CI/CD
With Appdome, organizations are using security best practices in a workflow used by the largest companies in the world with hundreds of releases each year. This workflow is so flexible that enables disparate, global dev, security ops teams to work together in a coordinated way that releases secure apps on time.
To embrace mobile DevOps and effectively protect from ransomware, the entire organization must adhere to new, rapid release processes that meld the different disciplines, development, security and operations, into one continuous workflow. In the new security release management workflow, it is critical that (a) actions be held by the group most capable of completing them, and (b) each group is accountable, transparent and, for its part, deliver with certainty in the release process. Appdome comprehensively protects from ransomware at the same time it enables each group in the organization to deliver its part with certainty in the release process.
Learn more on how to prevent mobile malware or request a demo of Appdome’s Mobile Malware Prevention solution.