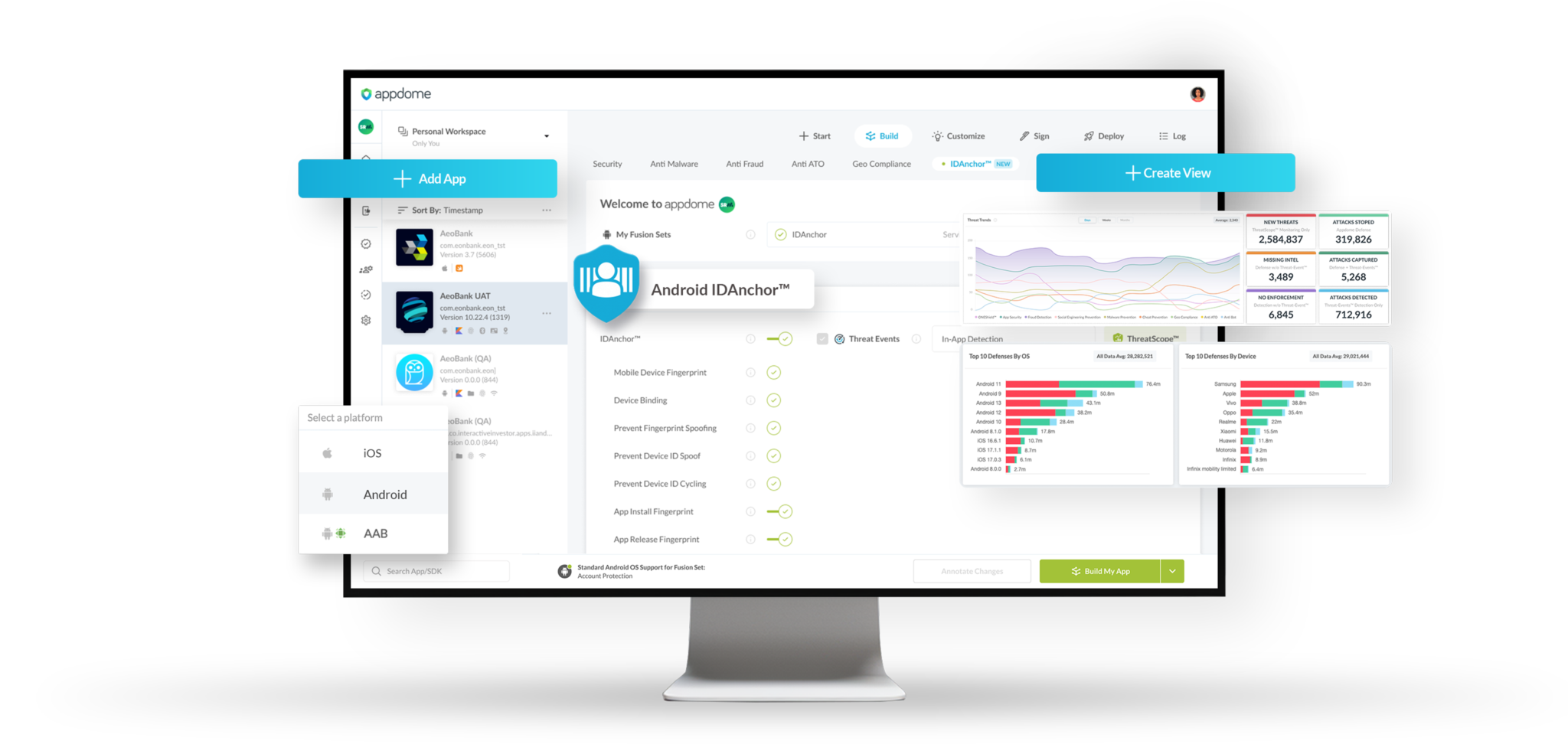
Start a 14-Day free trial of IDAnchor™ and automate the work out of device identity, device binding, and device intelligence in Android & iOS apps. Configure the IDAnchor™ profile on Appdome, initiate the build command, and Appdome codes the IDAnchor implementation in your mobile app for you – no SDK or manual work required. Use the IDAnchor Device, App, and Install IDs with any of Appdome’s 400+ Threat Signals to eliminate risk during application workflows such as onboarding, login, account updates, and payment.
Complete Mobile Identity & Reputation
+400 Real-Time Threat Signals
Trusted Identities for
Mobile Apps & Devices
IDAnchor™ builds trust into every identity assertion in a mobile app by generating a multi-layer, OS-independent, and immutable chain of trust that is tied to the mobile brand, fingerprints each Android & iOS app, install, and device with a unique identity, and binds mobile users, detections, and threats to these identities over time.
Learn More >
Mobile Device Intelligence
& Reputation in ONE
With IDAnchor™, combine Appdome's mobile app, install, instance, and device identities with 400+ threat signals in your production-level mobile apps. Retrieve comprehensive device intelligence and reputation during mobile onboarding, login, account recovery, payment, and more in the app or via your backend call to Appdome APIs.
Learn More >
Detailed Identity &
Threat Data APIs
IDAnchor™ includes powerful APIs to trace the lineage of each device and application change, update, and upgrade. IDAnchor also provides a MobileRISK™ API to gather risk scores and retrieve intelligence on fraud, spoofed devices, cloned installs, and synthetic identities, even if attackers mimic trusted behaviors or reuse valid credentials on known devices.
Learn More >

![[IDAnchor] - Customer Quote](https://www.appdome.com/wp-content/uploads/2025/07/IDAnchor-persona-CX-report-spotlight-768x613.png)