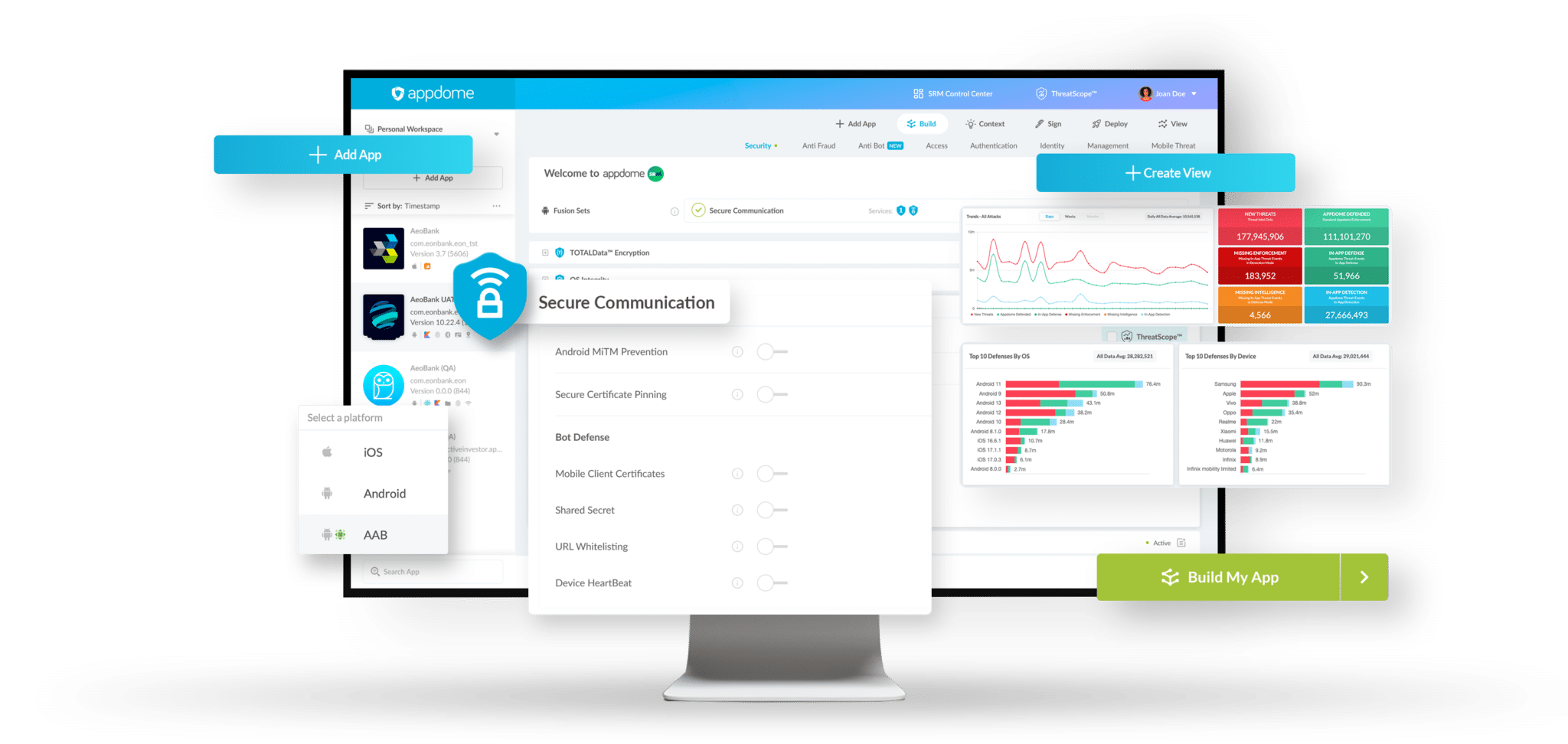
With Appdome, you can meet MitM attack prevention requirements without sacrificing your engineering freedom, development choices, other features, or the user’s experience.
Appdome uses AI to create and build MitM attack defenses that work with the way you’ve built your app, including the coding languages and frameworks used in your Android & iOS apps. Appdome also supports your existing DevOps tech stack, including CI/CD, test automation, release management, and more.
Need to deliver MitM attack prevention features without a lot of work, crashing your app or slowing down your release cycle? We’ve got you covered.

![[MitM Attack Prevention] - Customer Quote](https://www.appdome.com/wp-content/uploads/2025/06/MitM-Attack-D-CX-768x613.png)