Every year, OWASP releases reports on the top 10 most critical web and mobile application security risks, powerful awareness documents for application security that represent a broad consensus about the most critical security risks to apps. The OWASP community believes that “adopting the OWASP Top 10 is perhaps the most effective first step towards changing the software development culture within your organization into one that produces secure code”.
Here are some incredible statistics on the number of data breaches and the financial consequences for organizations that suffer these breaches.
- Forbes reported that in the first 6 months of 2019, there were more than 3,800 publicly disclosed breaches exposing an incredible 4.1 billion compromised records.
- Equifax will pay up to $700M over its data breach.
- British Airways faces $230M GDPR fines for its 2018 web and mobile data breach.
Luckily, whether y0u’re in mobile development, security, or operations (DevSecOps), anybody can implement a comprehensive multi-layered defense using Appdome Mobile App Security and anti-fraud solutions. Using Appdome, you can protect against to protect against OWASP Mobile Top 10 risks and verify the app’s protections using industry-standard best practice testing such as the OWASP Mobile Security Testing Guide (MASVS).
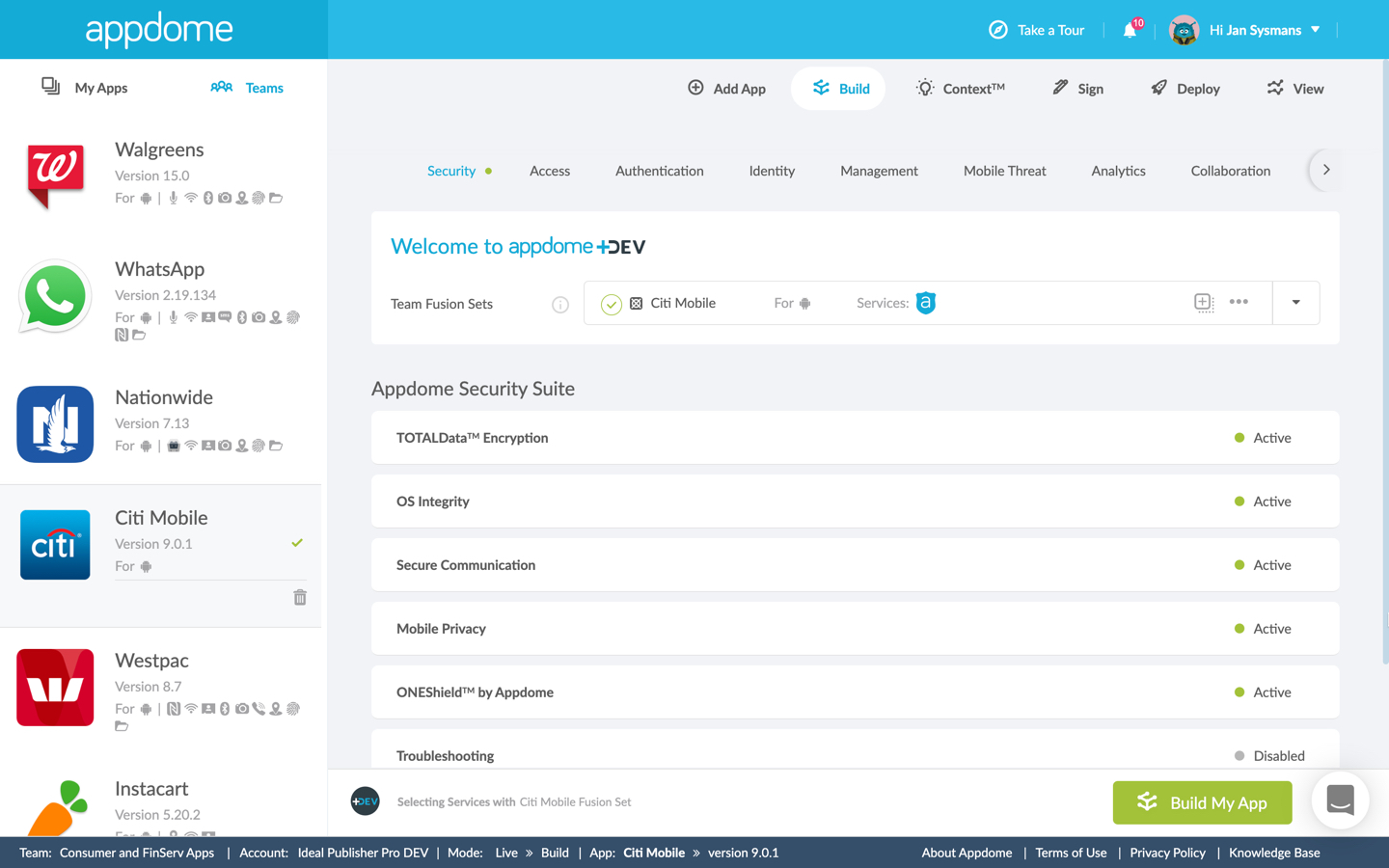
Appdome’s Mobile Security Suite offers no-code, on-demand advanced app protection in 5 distinct categories. Protection against the OWASP Mobile Top 10 risks can be added to any Android and iOS app, developed in any framework including Maui, Xamarin, React Native, Cordova, and others. Developers and non-developers can bring any .ipa or .apk binary to Appdome. There, they select one or multiple features from the list below using a simple point-and-click UI, and click the big green Build My App button to add security to their Android or iOS app in seconds – no code or coding required!
Here’s how Appdome’s Mobile Security Suite protects mobile apps against the OWASP Mobile Top 10 Risks
M1 – Improper Platform Usage
Customers can leverage Appdome to address this requirement by building one or more features from Appdome’s Mobile Security Suite:
- TOTALData Encryption – Encrypt all mobile app data, in-app preferences, string and resources.
- OS Integrity – Detect when a device was Jailbroken/Rooted and prevent installation of the secured app.
- Secure Communication – Appdome MitM prevention verifies the SSL/TLS connection to the secured app.
- Privacy -Govern Copy/Paste protection, blur the application screen, Prevent keyloggers and add in-app Pincode/FaceID/fingerprint to the secured app.
- TOTALCode Obfuscation – Obfuscate native and non-native mobile app code.
In addition, customers could also integrate any leading EMM, UEM, MAM or MDM SDK from within Appdome’s Mobility Management category in lieu of or in addition to Appdome’s security features.
And finally, every app built on Appdome automatically gets advanced app hardening with ONEShield by Appdome. ONEShield includes anti-debugging, anti-reversing, app integrity/structure scanning, obfuscation and more.
M2 – Insecure Data Storage
With TOTALData Encryption, customers can instantly encrypt and protect all three states of mobile app data; data-at-rest, data-in-transit and data-in-use in any mobile app by simply clicking a toggle to enable the feature. When enabled, all data within the app (as well as data on the device created by the app) is encrypted so that it cannot be read in the event of a compromise. Optionally, customers can also exclude certain files or file-types from being encrypted. TOTALData Encryption is one of the easiest ways to protect against the OWASP mobile top 10 risks.
The strings and resources include among other things all the personal identifyable information (PII) of the user. This PII information is the target of most credential theft attacks. On Appdome, it is very easy to encrypt the strings and resources in any Android or iOS app.
M3 – Insecure Communication
Appdome’s Secure Communication validates the authenticity of trusted communication sessions initiated by the app. This includes Man in the Middle (MiTM) attack prevention, malicious proxy detection, prohibiting stale sessions from reclaiming SessionIDs, Enforcing TLS version, Static Client Pinning and more.
M4 – Insecure Authentication & M6 – Insecure Authorization
Under Appdome’s Enterprise Authentication and Mobile Identity category, customers can integrate apps with their existing enterprise authentication and authorization system, choosing from the following options:
- Mobile Enterprise Authentication – Enables apps to leverage authentication schemes such as SAML, OAuth, OpenID Connect, Kerberos, or KCD or a custom IdP when accessing gated resources.
- Cloud-Based authentication – Instantly connect any app with your existing cloud identity provider to achieve native mobile SSO in any app.
- Mobile Identity SDK integration – Integrate any app with mobile SDKs for MFA and Biometrics.
- Private ID – Unique to the Appdome Identity Suite, Private ID encrypts and protects cached identity information, such as cookies and credentials, which might otherwise be stored ‘in the clear’ inside the app.
- Direct Broker – Appdome’s Direct Broker feature enables customers to connect their mobile apps directly to their chosen identity provider, without using publicly resolved brokers (which can easily be hacked).
M5 – Insufficient Cryptography
Appdome customers can choose to implement FIPS140-2 certified cryptographic modules for encrypting data. FIPS140-2 can be combined with Appdome’s TOTALData Encryption feature. Additionally, Appdome uses AES-CTR-256 bit encryption for all Data at Rest and Obfuscation implementations. SSL inspection strongly validates authenticity, protocol and encryption settings for Secure Communication and provides an easy way for mobile developers to ensure their apps are using the most secure and robust cryptography available in all their apps. In-App secrets encryption provides seamless standard encryption to all secrets, keys, URLs and sensitive data located in your app. Many apps store such data in either ‘in the clear’ or using older encryption standards that are not regularly updated or
maintained (due to the difficulty of changing crypto modules inside apps). Finally with TOTALCODE™ Obfuscation, you can obfuscate native code, non-native code, libraries, control flows and application logic to prevent against malicious reverse engineering.
M6 – Insecure Authorization
With Appdome for SSO+, or Appdome for Enterprise Authentication options, customers can integrate any mobile app with their chosen IDaaS or IAM solutions, or they can implement standards like OpenID Connect (which cover both authentication and authorization) inside any mobile app. In addition, customers can also add Complex In-App Pincode or Fingerprint Biometric Identity to Android and iOS apps.
M7 – Client Code Quality
ONEShield™ app shielding is automatically included as part of every build on Appdome. ONEShield includes Anti-Debugging, Anti-Tampering, App Integrity/structure scanning, and Anti-Reversing. Appdome’s TOTALCODE™ Obfuscation fully obfuscates the source code, including obfuscation of native code/libraries, as well as non-native code. You can also obfuscate the application’s logical flows using control flow obfuscation and strip debug info.
M8 – Code Tampering
Anti-tampering is included with ONEShield™. Appdome developed multi-layered Anti-debugging and Anti-Tampering techniques. With Appdome, attempts to use dynamic or static analysis tools to tamper with the application or understand the app’s business logic will force the app to exit (or optionally developers can instrument other enforcement actions using Appdome Threat Events).
M9 – Reverse Engineering
Using anti-reversing and Obfuscation, Appdome obfuscates the application’s code on the binary level, including non-native source code. You can also obfuscate and encrypt DEX files and java classes, encrypt strings (including Java strings, strings.xml, CFStrings). You can also encrypt app preferences (encrypt app preferences in iOS (NsUserDefaults), encrypt shared preferences in Android). To prevent malicious static code analysis, it’s also important to encrypt the applications’ logic flows (control flow obfuscation) and remove debug information. These features complement Appdome’s ONEShield, which prevents dynamic analysis (anti-debugging, anti-tampering, emulator/simulator prevention, etc) to protect against all forms of reversing.
M10 – Extraneous Functionality
This requirement is covered by an app Structure/integrity scan, which is automatically performed for every app uploaded to the platform.
Related Posts
Protect Apps from OWASP Mobile Top 10 Risks with Appdome Mobile Fraud Prevention
Protect All Mobile App APIs Against the OWASP API Security Top 10 Risks
Other Helpful Resources
OWASP MASVS Test Plan for Reverse Engineering prevention – typically used by Appdome customers and penetration testers to validate the application’s defenses and test the app’s resilience to malicious reverse engineering.
For more info on how to protect your mobile apps download the Appdome Developer Guide or request a demo today.





