How to Test Appdome-secured iOS Apps on Browserstack
Learn how to test Appdome-secured iOS Apps using Browserstack’s mobile testing suite. Appdome is 100% compatible with all leading mobile application test automation solutions used by DevSecOps teams. Automated testing of secured iOS apps helps developers and others rapidly deploy comprehensive mobile app security and fraud detection with DevSecOps speed and agility.
This knowledge base article covers the steps needed to test Appdome-secured iOS mobile apps using the BrowserStack mobile test automation suite.
Appdome works with all leading mobile automation testing solutions to help customers achieve comprehensive mobile app security at DevSecOps speed and agility, all within the app’s existing application lifecycle.
Use Appdome’s Build2Test service to test iOS-protected applications on Browserstack for both Live and Automated testing.
Customers with an Appdome SRM license can use Appdome’s Build2Test service to quickly and easily test their Appdome-secured mobile apps by using Browserstack without the need for different Fusion Sets. With Appdome’s Build2Test service, Appdome’s in-app defense model recognizes the unique signature of these testing services and allows for easy testing without issuing a security alert or forcing the app to exit, even if these services use tools such as Magisk or Frida. For details, see How to Use Appdome Mobile App Automation Testing.
General Information about Testing in iOS Apps
The following table describes which Appdome protection features may be triggered and the reason why:
| Appdome feature | Reason | Behavior with Build2Test |
| Prevent App Screen Sharing | BrowserStack allows a live view of the device screen while the test is running. | The app will recognize the screen recording but will continue running without crashing. |
| Detect App is Debuggable | BrowserStack signs the app as debuggable upon installation | The app will acknowledge the debuggable state but will continue operating normally during the testing process |
| Secure App Signature | BrowserStack resigns the app upon installation. | The app will detect the signature change but will not crash, allowing the testing to continue without interruption. |
| Enforce Cipher Suites | BrowserStack supports a variety of cipher suites, which Appdome can restrict to enforce secure communications as per app-specific protocols. | The app will acknowledge the cipher suites but will continue operating normally during testing. |
| Anti Remote Desktop Control | BrowserStack might use remote control tools during tests to trigger this protection. | The app will detect remote control attempts but will not terminate the session, allowing testing to proceed. |
Live App testing – iOS
- Log in to your BrowserStack account. Alternatively, if you do not yet have an account, Create an account.
- Click the Let’s Go button on BrowserStack’s account page.
The website now displays a page with a list of iOS and Android devices on which you can test the app. - Click App Live on the top of the page.
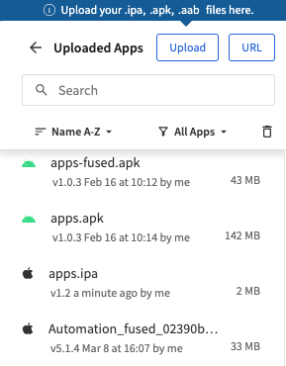
- Click Upload to upload your signed app build.
- After the app upload is complete, select the device to be used to test the app.
To do that, click the device type (iPhone, in the example shown below) and then the device model. The app will be automatically installed on the selected device and then launched.
- Note:
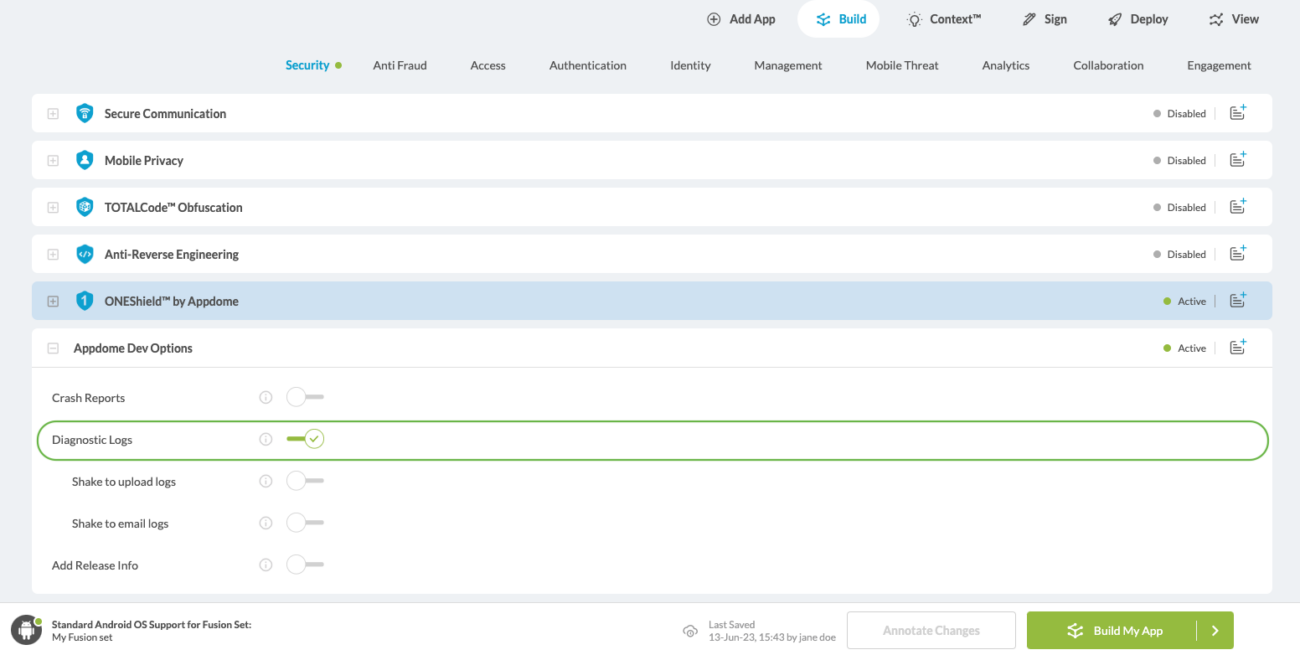
In case of any issues with the app, you need to send the device logs to Appdome Support by following these steps:- Go to Build > Security on Appdome.
- Go to the Appdome Dev Options section.
- Enable(toggle On) the option Diagnostic Logs.
For details, see the Knowledge Base article Appdome Diagnostic Logs for Troubleshooting Secured Apps.
- Go back to BrowserStack and re-run the steps used to upload the app to the selected device.
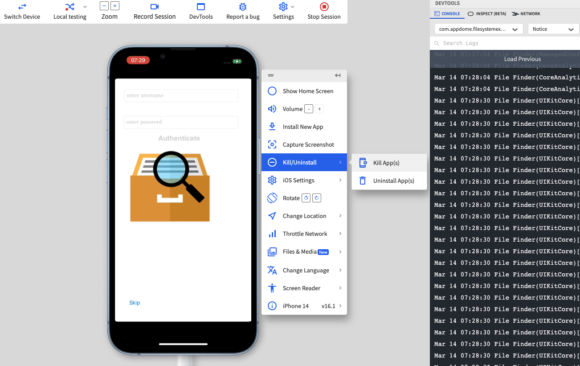
- Click the Kill/Uninstall button on the running app.
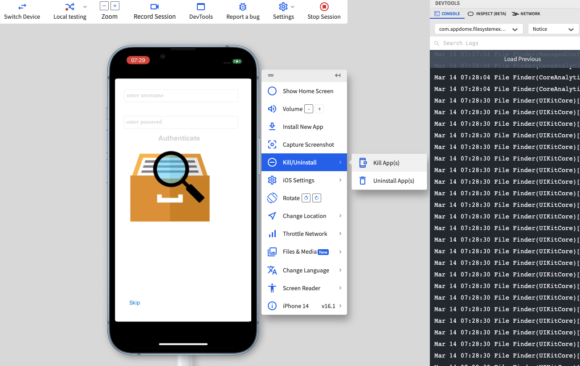
- Select the options All Device Logs and Verbose.
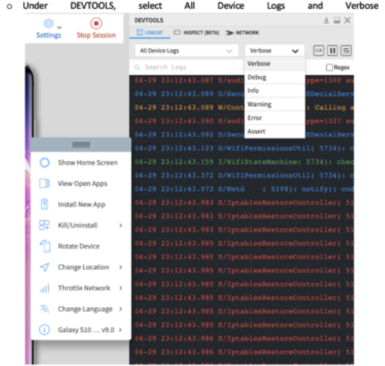
- Clear the log under DEVTOOLS.
- On the device, open the app once more, getting to the point where the issue occurred (and take note of the time).
- Click Download at the top right-hand corner under DEVTOOLS.
- Set a name for the downloaded log, including the time the issue occurred.
- Sent the log by email to support@appdome.com, complete with details on the issue, device model, and OS version used in testing.
Automating App Testing on iOS
| Appdome feature | Reason |
|
iOS MitM Prevention
|
BrowserStack uses a MitM proxy |
| BrowserStack-Specific Appium Capability | Reason |
| networkLog | By default, BrowserStack re-signs the app to enable capturing network logs. |
Troubleshooting Tips
- Most automation test tools can typically be used in one of two modes: emulator mode and real device mode (specific terms may vary according to the testing tool). If you use the automation test tool in “emulator mode” instead of “real device mode,” the Appdome-secured application will not run on the device. This is expected because Appdome ONEShield protects apps from running on emulators/simulators. Instead, it would be best if you run the automation test tool on an actual device.
- If your mobile application closes/exits unexpectedly and/or you see a message such as: “Application has violated security policies and it will be shut down”, this usually means that techniques are present which Appdome protects against, such as emulator mode, tampering, reverse engineering, or root hiding. Below are some of the likely causes:
- The user may be running the testing tool in ’emulator’ mode, which Appdome protects against. To remedy this, run the test in ‘manual’ mode or using real devices.
- BrowswerStack’s VPN uses TCP port 80 (HTTP), which does not encrypt traffic. If you built your application with Appdome’s MitM Prevention or other features from Appdome’s Secure Communication category, the TCP session will be blocked. This is expected and by design.
Related Articles
- How to Test Secured Android Apps on Lambdatest
- How to Test Secured iOS Apps on Lambdatest
- How to Use Appdome’s Build2Test Service
- Test Appdome-secured Android Apps by Using SauceLabs
- Testing Secured iOS Apps by Using SauceLabs
- How to Test Secured Android Apps on BitBar
- How to Test Secured Android Apps on BrowserStack
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.