How to Use Appdome Mobile EDR
How Traditional EDR Offerings Work
Traditional EDR (Endpoint Detection and Response) and MTD (Mobile Threat Defense) products are designed to secure devices by installing agents that monitor and respond to threats. These solutions have been limited to protecting endpoints like computers and laptops from various cyber threats, but they come with several fundamental issues that limit their ability to protect mobile applications:
- Agent-Based Approach: Traditional EDR and MTD systems require the installation of agents or separate apps on the endpoint. This method can create friction as it depends on the user to install, maintain, and actively run the security application.
- User Dependency: These agents’ effectiveness relies heavily on the end user’s keeping them running, which can lead to inconsistent protection if users disable or ignore them.
- Privacy Concerns: In BYOD (Bring Your Own Device) environments, users may be reluctant to install corporate security apps on personal devices due to privacy concerns. This resistance can limit the deployment of traditional EDR solutions.
- Operational Limitations: Many legacy agents need a constant connection to backend servers. If the device loses internet connectivity, the EDR/MTD’s functionality might be compromised, operating “in the blind” or not at all.
- Limited Preventative Actions: Agents typically notify users about potential threats but often cannot prevent the installation of malicious software beforehand. They act more as detectors rather than preventers of initial threats.
What is Appdome Mobile EDR?
Appdome Mobile EDR represents a revolutionary step forward in mobile cybersecurity by integrating directly with mobile apps to deliver EDR and MTD functionalities without the need for traditional agents. This solution addresses the shortcomings of legacy EDR systems by offering the following features:
- Agentless Integration: Appdome Mobile EDR is embedded directly into mobile apps, eliminating the need for separate security apps and reducing user friction.
- Threat-EKG™: Continuous, real-time threat monitoring and assessment is handled within the app, providing a seamless security experience without impacting user privacy or device performance.
For more information on Threat-EKG, please refer to this knowledge base article:
How to use Threat-EKG with Appdome’s Mobile EDR - Broad Threat Detection: The solution detects a wide array of threats, including malware, spyware, network attacks, and policy violations, ensuring comprehensive mobile security.
- Privacy-First Design: The security features are active only when the enterprise mobile app is in use, which means personal user activities remain private and unaffected by the security measures.
- Enhanced Control and Visibility: Enterprises gain extensive control over their mobile security environment with features like Appdome ThreatScope Mobile XTM, which provides detailed telemetry and rapid response capabilities.
In essence, Appdome Mobile EDR offers an integrated, non-intrusive approach to mobile security. It effectively safeguards mobile applications and devices within the enterprise without the drawbacks associated with traditional EDR solutions. This makes it an ideal choice for modern enterprises looking for effective, user-friendly, and privacy-conscious mobile security solutions.
Prerequisites for using Appdome’s Mobile EDR
- Appdome account (create a free Appdome account here)
- A license for Mobile EDR
- Mobile App (.ipa for iOS device or .apk or .aab for Android)
- Signing Credentials (see Signing Secure Android apps and Signing Secure iOS apps)
Overview of Appdome Mobile EDR Features
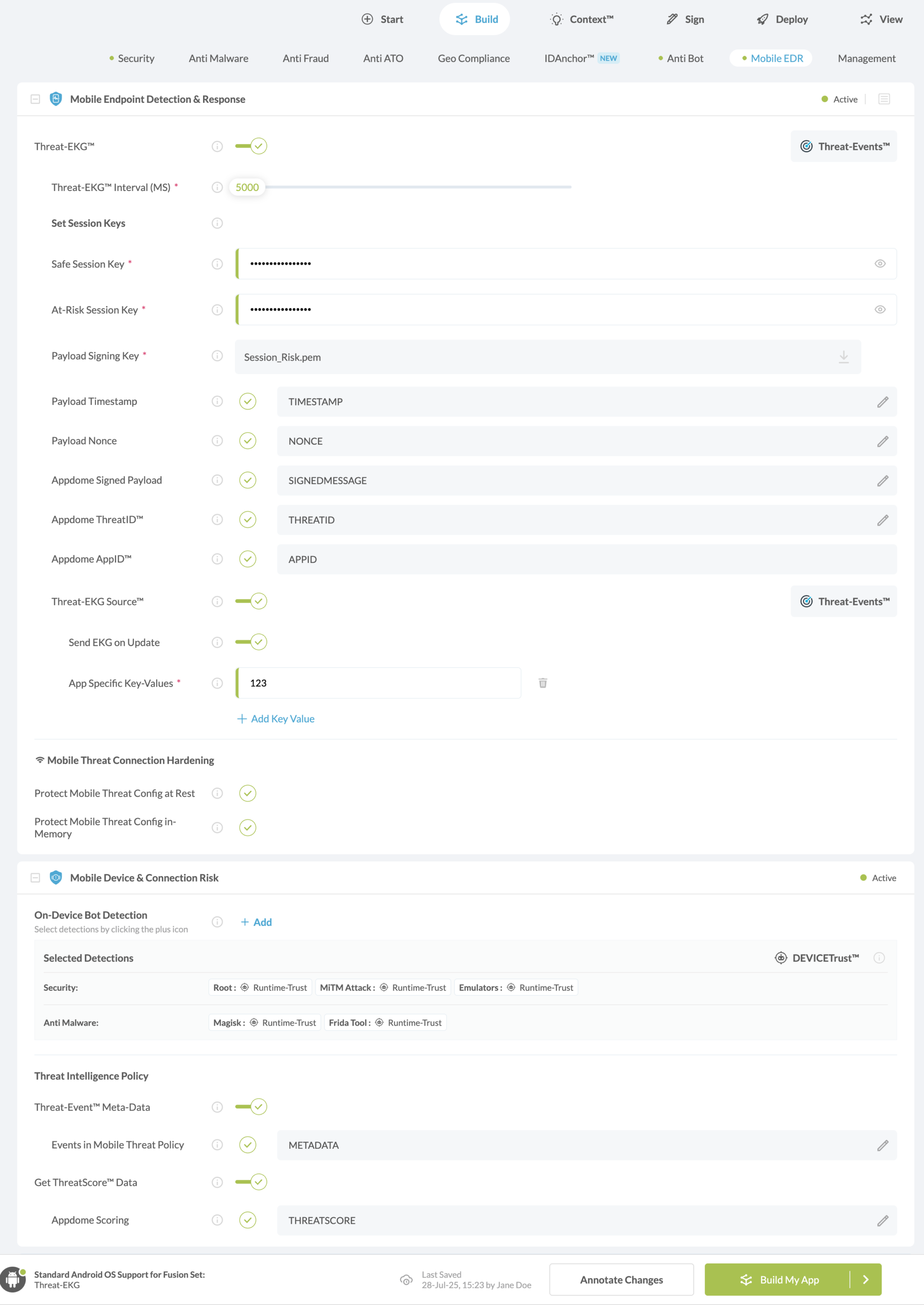
Mobile Endpoint Detection & Response
Threat-EKG™ – Continuous threat assessment for mobile endpoints without an on-device agent.
Learn more about Threat-EKG.
Threat-EKG™ Interval (MS) – Every couple of milliseconds, Appdome sends a health status update to your mobile app, indicating whether the connection is compromised or at risk.
Session Values
Safe Session – Represents sessions that are determined to be safe or not at risk of any threat.
At-Risk Session – Represents sessions that are potentially under threat or have detected anomalies.
Payload Signing Key – The public key that Appdome uses to encrypt the payload.
Payload Timestamp – Marks the specific time at which the payload was created or sent.
Appdome ThreatID™ – Each threat vector detected by the system is assigned a specific Threat ID.
Payload Nonce – A unique, one-time token that a mobile application generates during session initiation or at critical transaction points.
Appdome Signed Payload – Ensures data integrity and security by verifying the digital signature of each payload before connection.
Appdome AppID™ – A unique identifier for each version of an app fused with Appdome’s services, allowing customers to track a request back to the specific Appdome version in use.
Anti-Bot Connection Hardening
To eliminate hijacking and replay attacks, Appdome’s Mobile EDR solution protects all data-in-rest with pre-packaged features such as data-at-rest encryption for all Threat-EKG configurations, secrets, keys, IDs, etc., as well as a protected memory space for all Anti-Bot functions.
Protect Anti-Bot Config at Rest
Encrypts all Mobile Anti-Bot configurations, including host, keys, certificates, etc., at rest to prevent the harvesting.
Protect Anti-Bot Config in Memory
Prevents attackers from harvesting Mobile Anti-Bot configurations, including host, keys, certificates, etc., in memory.
Prevent Session Replay Attack
Appdome detects and prohibits session replay attacks and reclaims SessionID for stale TLS sessions so that hackers cannot reuse them in their attacks.
Prevent Session Hijacking
Appdome detects, prohibits, and protects app connections from session hijacking by validating the server SSL certificate chain’s authenticity and providing authenticity proof to the server on behalf of the client.
Prevent Cookie Hijacking
Appdome detects, prohibits, and protects app connections against cookie hijacking by validating the server SSL certificate chain’s authenticity and providing authenticity proof to the server on behalf of the client.
Malicious Proxy Detection
Appdome detects any attempt to connect to or from unknown, untrusted, or malicious proxies or other intermediary devices.
Deep Proxy Detection
Appdome performs a deep inspection of proxies and proxy techniques, including header manipulation and redirects.
Mobile Device & Connection Risk
Mobile Anti-Bot Policy
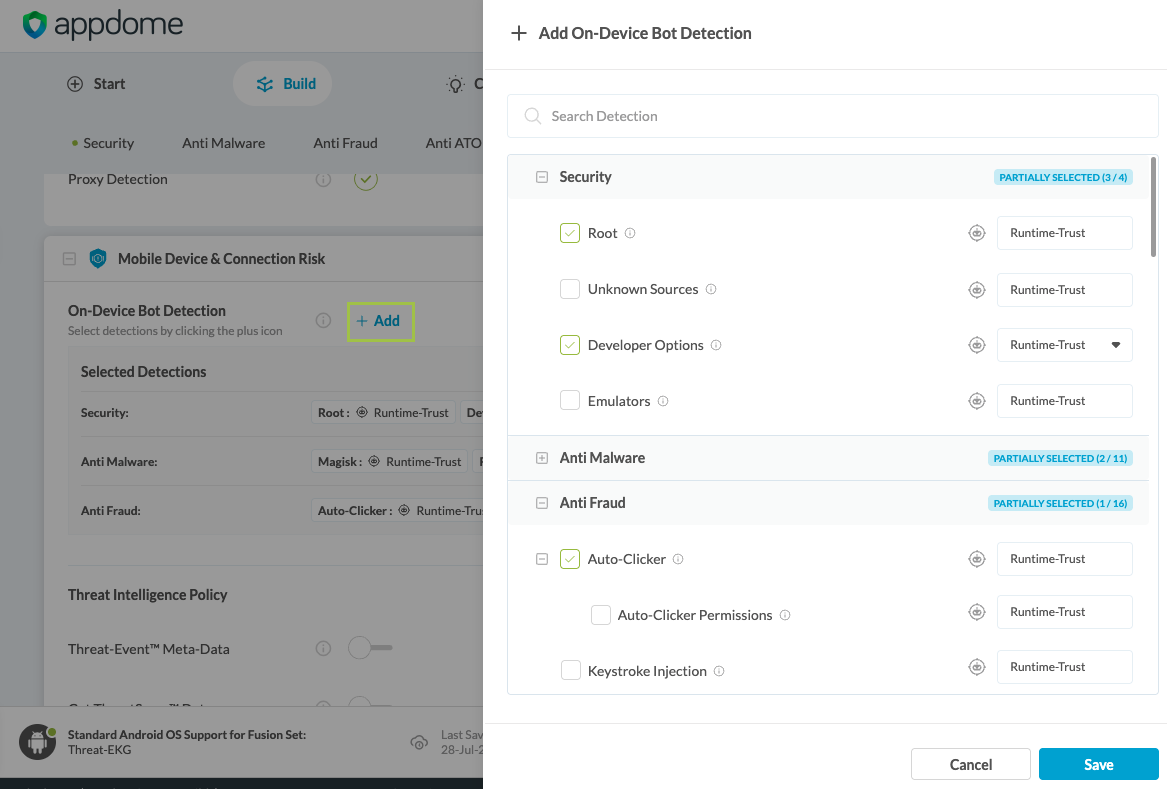
On-Device Bot Detection enables mobile developers to configure which on-device threats—such as Root, Magisk, Emulators, Jailbreak, Fake Location, and more—will contribute to session risk classification in the app. For each detection, developers define a DEVICETrust™ level: Zero-Trust, which delays connection until checks are complete, or Runtime-Trust, which allows assessment during connection. For example, when adding Detect Fake Location as a detection, the session will be classified as compromised based on location spoofing. This configuration feeds into Mobile Device & Connection Risk, which tags each session as Safe or At-Risk and enables WAFs and backend systems to validate session authenticity in real time.
To add additional On-Device Bot Detections, click on the +Add button and select from the right side panel
Note: Please be aware that the MitM Prevention and Mobile Anti Bot Policy features are mutually exclusive. Implementing them together will result in a conflict within the engine. To avoid potential issues, ensure that you use only one method at a time.
Threat Intelligence Policy
Threat-Event Meta-Data is an optional configuration in Mobile Device & Connection Risk that enriches mobile bot detection payloads with additional environmental context, including operating system, device model, manufacturer, and SSL certificate metadata. These metadata fields are used by WAFs to assess whether the mobile session originates from a legitimate safe or at-risk endpoint.
ThreatScore is another optional configuration that adds a numeric risk score to each user and device session, helping backend systems quantify and respond to bot and automation threats. This score reflects the cumulative risk based on detected mobile threats—such as root, Magisk, emulators, or fake location—and provides a simplified value to inform automated policy decisions.
Related Articles:
- Understanding ThreatScope Mobile XTM Threat-Views
- How to use MobileBOT Source™ with Mobile Bot Defense
- How to Use Session Risk in Mobile Bot Defense
- How to Use Payload Timestamps In Mobile Bot Defense
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.