How to use Device HeartBeat in Android Apps
What is Device HeartBeat?
Device HeartBeat is an Appdome Threat-Events-based method of verification that ensures the health and security of both the device and its connection to the app’s server. This verification process involves the utilization of two secret keys that are sent to the app server in time intervals defined by the user, and confirm the health of the device and the connection . This feature allows continuous validation of the device, enabling the app’s server to react swiftly to a threat and restrict access to confidential resources or to sever the connection to the device, in order to minimize potential damages in the event of a compromise.
The Device HeartBeat process generates and sends three key elements using Appdome Threat-Events. Firstly, a timestamp is included in each HeartBeat event, providing a record of when the event occurred. Secondly, a unique identifier is assigned to each HeartBeat, ensuring that each event can be uniquely identified and tracked. Lastly, the signed HeartBeat state message to be verified by the app’s server.
How to implement Device Heartbeat with Appdome?
The implementation of Device HeartBeat requires the following elements.
Header Message Signing Key: This private RSA key is utilized to sign the heartbeat and should correspond to the RSA public key employed for server-side heartbeat validation.
Protected State Shared Secret: This secret is mutually shared between the protected app and the application server. Its purpose is to indicate that the app is operating within a secure environment. This secret is utilized as long as no detections have been triggered in the Appdome-protected app.
Compromised State Shared Secret: This shared secret serves as an indicator that the app is running in a compromised environment. Any requests made by the app subsequent to a detection being triggered will generate a heartbeat using this secret. The state is determined during the lifespan of the app and will reset in the subsequent launch. Consequently, if the compromised state detected in a previous run is mitigated or no longer present, heartbeats will be generated using the protected state shared secret.
Heartbeat Interval: This parameter allows the user to define the time intervals, in milliseconds, between each heartbeat transmission via ThreatEvents.
Using Device HeartBeat on Android apps by Using Appdome
On Appdome, follow these 3 simple steps to create self-defending Android Apps that Use Device HeartBeat without an SDK or gateway:
1. Upload the Mobile App to Appdome.
-
- Upload an app to Appdome Cyber Defense Automation Build System
- Upload Method: Appdome Console or DEV-API
- Android Formats: .apk or .aab
-
Device HeartBeat Compatible With: Java, JS, C++, C#, Kotlin, Flutter, React Native, Unity, Maui, Xamarin, Cordova and more
2. Build the feature: Device HeartBeat.
-
Building Device HeartBeat by using Appdome’s DEV-API:
- Create and name the Fusion Set (security template) that will contain the Device HeartBeat feature as shown below:
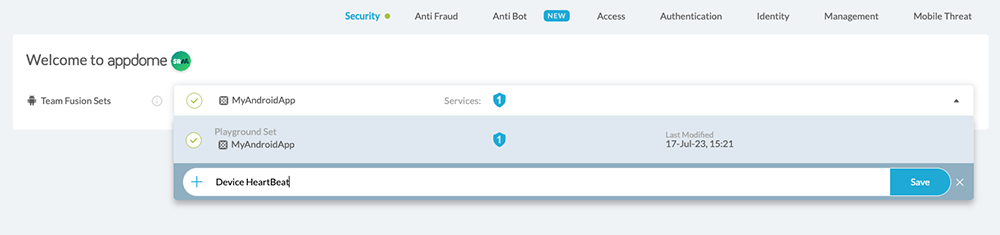
Figure 1: Fusion Set that will contain the Device HeartBeat feature
Note: Naming the Fusion Set to correspond to the protection(s) selected is for illustration purposes only (not required).
-
Follow the steps in the ‘Building the Device HeartBeat feature via Appdome Console’ section to add the Device HeartBeat feature to this Fusion Set.
-
Open the Fusion Set Detail Summary by clicking the “…” symbol on the far-right corner of the Fusion Set, as shown in Figure 1 above, and get the Fusion Set ID from the Fusion Set Detail Summary (as shown below):
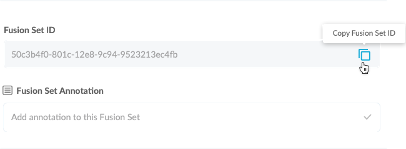
Figure 2: Fusion Set Detail Summary
Note: Annotating the Fusion Set to identify the protection(s) selected is optional only (not mandatory). -
Follow the instructions below to use the Fusion Set ID inside any standard mobile DevOps or CI/CD toolkit like Bitrise, App Center, Jenkins, Travis, Team City, Circle CI or other system:
-
Build an API for the app – for instructions, see the tasks under Appdome API Reference Guide
-
Look for sample APIs in Appdome’s GitHub Repository
-
- Create and name the Fusion Set (security template) that will contain the Device HeartBeat feature as shown below:
- Building the Device HeartBeat feature via Appdome Console:
To build the Device HeartBeat protection by using Appdome Console, follow the instructions below.-
Where: Inside the Appdome Console, go to Build > Security Tab > Secure Communication section
- How: Toggle (turn ON) Device HeartBeat, as shown below.
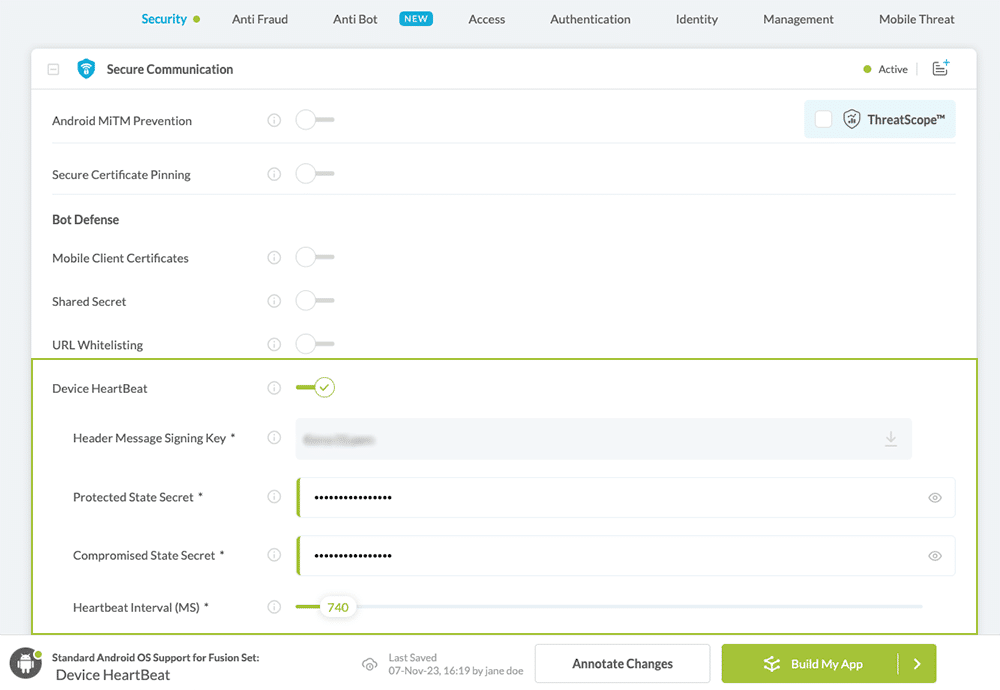
Figure 3: Use Device HeartBeat option.
- When you select the Device HeartBeat you’ll notice that your Fusion Set you created now bears the icon of the protection category that contains Device HeartBeat
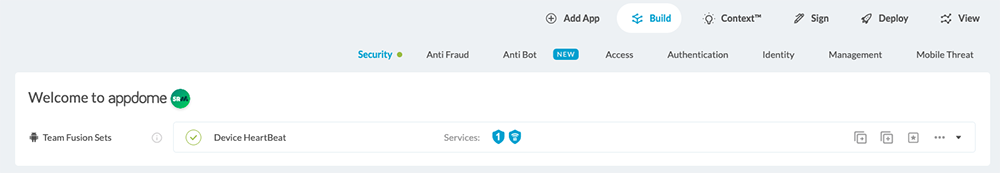
Figure 4: Fusion Set that displays the newly added Device HeartBeat protection.
- Click Build My App at the bottom of the Build Workflow (shown in Figure 3).
-
Congratulations! The Device HeartBeat protection is now added to the mobile app
3.Certify the Device HeartBeat feature in Android Apps.
After building Device HeartBeat, Appdome generates a Certified Secure™ certificate to guarantee that the Device HeartBeat protection has been added and is protecting the app. To verify that the Device HeartBeat protection has been added to the mobile app, locate the protection in the Certified Secure™ certificate as shown below:
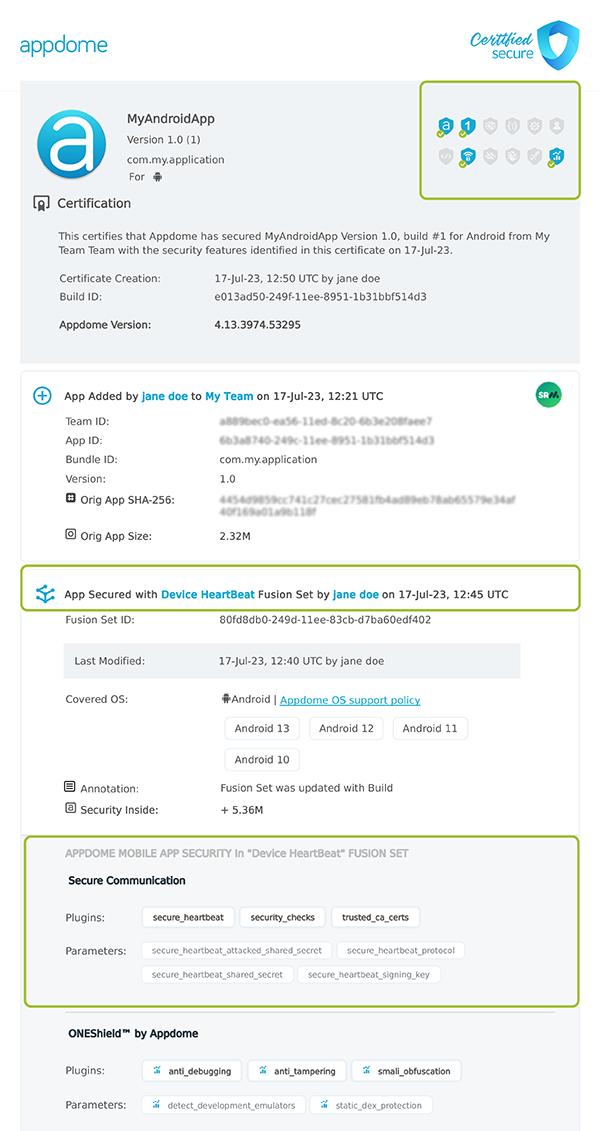
Figure 5: Certified Secure™ certificate
Each Certified Secure™ certificate provides DevOps and DevSecOps organizations the entire workflow summary, audit trail of each build, and proof of protection that Device HeartBeat has been added to each Android app. Certified Secure provides instant and in-line DevSecOps compliance certification that Device HeartBeat and other mobile app security features are in each build of the mobile app.
Prerequisites to Using Device HeartBeat:
To use Appdome’s mobile app security build system to Use Device HeartBeat , you’ll need:
- Appdome account (create a free Appdome account here)
- A license for Threat-Events
- A license for Device HeartBeat
- Mobile App (.apk or .aab For Android)
- Signing Credentials (see Signing Secure Android apps and Signing Secure iOS apps)
Using Appdome, there are no development or coding prerequisites to build secured Android Apps by using Device HeartBeat. There is no SDK and no library to code or implement in the app and no gateway to deploy in your network. All protections are built into each app and the resulting app is self-defending and self-protecting.
Releasing and Publishing Mobile Apps with Device HeartBeat:
After successfully securing your app by using Appdome, there are several available options to complete your project, depending on your app lifecycle or workflow. These include:
- Customizing, Configuring & Branding Secure Mobile Apps
- Deploying/Publishing Secure mobile apps to Public or Private app stores
- Releasing Secured Android & iOS Apps built on Appdome.
Related Articles:
How to Prevent MiTM Attacks in Android Apps
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.
