How to Manually Deobfuscate Crash Stack Traces for Debugging Android Apps when using Obfuscate App Logic
As part of Appdome’s protection for applications, Appdome offers Obfuscate App Logic to any Android mobile app. Appdome’s de-obfuscation tool allows the application owner to recover the correct stack trace from the crash report.
This Knowledge Base article provides step-by-step instructions for manually deobfuscating stack traces when debugging Android apps using Obfuscate App Logic.
Deobfuscating Android Stack Trace (Crash Reports) with the Appdome Deobfuscation Tool
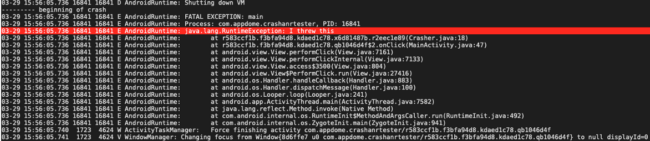
In certain cases, when an app is built with Obfuscate App Logic, the crash stack trace does not provide the reason for the crash. This happens because the classes in the crash stack trace are obfuscated.
Here is an example of a crash stack trace generated by a crash of a sample application called CrashTester. As shown below, it is impossible to understand the class from which the crash originated.
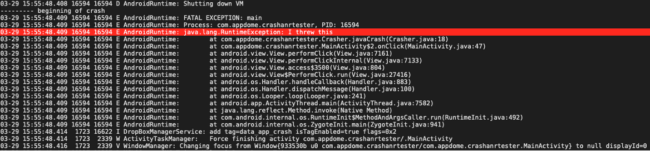
After running Appdome’s deobfuscation tool, the stack trace displays the correct classes of the application:
How to get Appdome’s Deobfuscation Tool for Deobfuscating Android Crash Reports
To get the deobfuscation tool for your fused app:
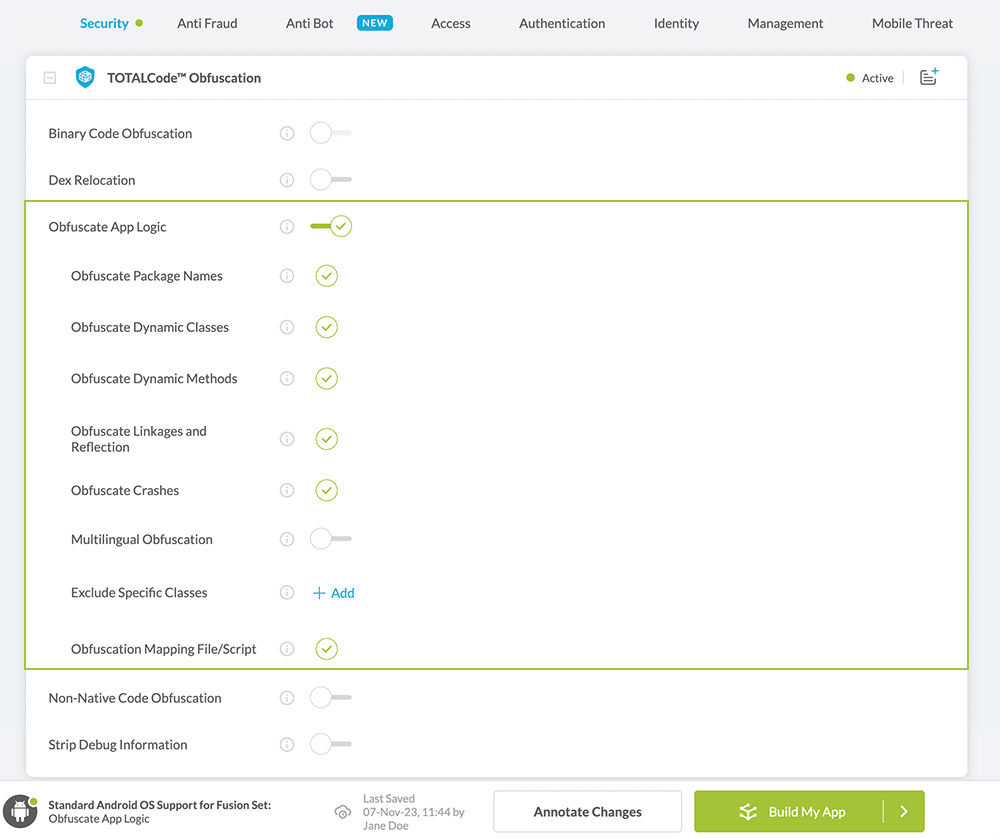
- Build an Appdome app with the Obfuscate App Logic feature turned on.
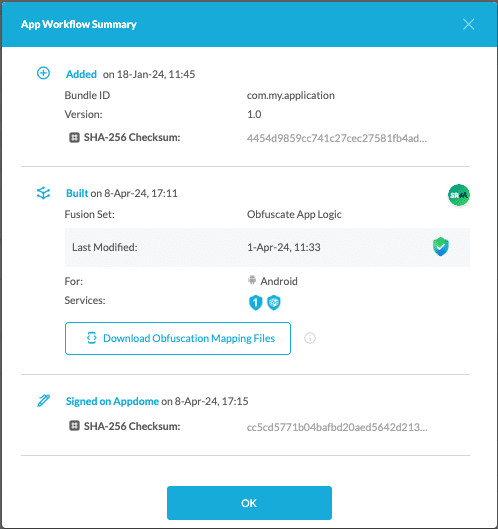
- After completing the entire build, click Workflow Summary.
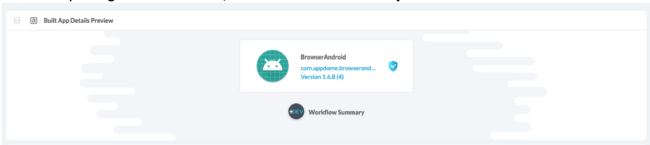
- Click Download Obfuscation Mapping Files to download the Deobfuscation tool.
How to use Appdome’s Deobfuscation Tool on your App Reports to Deobfuscate Stack Traces in Android Apps
The deobfuscation files downloaded from the Workflow Summary contain the following files:
- deobfuscate_mapping_script_<task_id>.py
This is a Python script that will automatically deobfuscate all obfuscated references in logcat logs from the specific Task ID of the app build.
Usage: python deobfuscate_mapping_script_<task_id>.py -f <path_to_obfuscated_log> -
mapping.txt
A file containing a dictionary of the obfuscation names translation.
A mapping file in the same format of ProGuard and R8 format can be uploaded to the Google PlayStore, Crashlytics, Bugsnag, etc. -
unobfuscated_mapping.json
A JSON file that contains the reasons for the names that were not obfuscated.
Related Articles:
- How to Remove Debug Information, Anti-Reversing Android & iOS Apps
- How to Optimize File Size, Code Obfuscation Best Practices in Android & iOS Apps
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.