How to Use Microsoft Secure Browser and Email in Mobile Apps
Learn how to use ‘open in’ Microsoft Secure Browser and Secure Email in mobile apps.
Microsoft Intune is the leading Mobile App Management (MAM) systems in the market today. In addition to Microsoft Intune, Microsoft offers its customers a secure browser, Email, and document sharing capability. Unlike Microsoft mobile Apps, 3rd party Apps aren’t pre-built to restrict the use of a browser, Email, and document sharing to Microsoft’s secure apps by default. These capabilities are not coded inside non-Microsoft apps.
This Knowledge Base article provides step-by-step instructions for using Appdome’s BoostEMM™ service to add the Microsoft secure browser, Secure Email, and document sharing into non-Microsoft mobile Apps in seconds.
What is Microsoft Secure Browser and Secure Email?
Appdome’s BoostEMM™ service restricts apps to use Microsoft’s Secure Email, Secure Browsers and secure document sharing to mobile Apps automatically. Your app will adhere to Intune’s security policy as if the SDK was natively coded to the app.
Furthermore, for iOS apps, Appdome also supports App Extensions, allowing the fused app to use the secured Microsoft apps services inline.
How to Add Microsoft’s Secure Browser, Email and Document Sharing Using Appdome’s BoostEMM™
To use Appdome’s BoostEMM™ service, follow these simple steps. Note, the same workflow can be used for either an Android or iOS App.
Appdome is a no-code mobile app security platform designed to add security features and 3rd party services and SDKs to Android and iOS apps without coding. This KB shows mobile developers, DevSec and security professionals how to use Appdome’s simple ‘click to build’ user interface to quickly and easily.
Upload a Mobile App to Your Account
Please follow these steps to add a mobile app to your Appdome account.
Once you find the .ipa or .apk or .aab file you intend to use, simply select it. The file will be automatically added to the Appdome platform. Once complete, you’ll see a success message and automatically moved to the next step in the workflow.v
Select BoostEMM™ Features
Click Management under the Build tab.
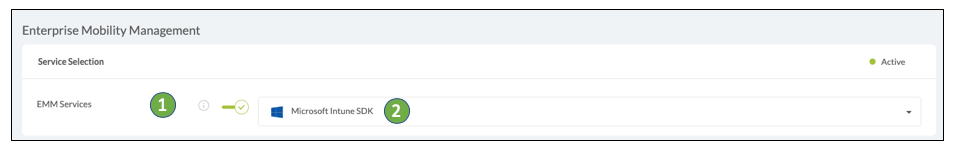
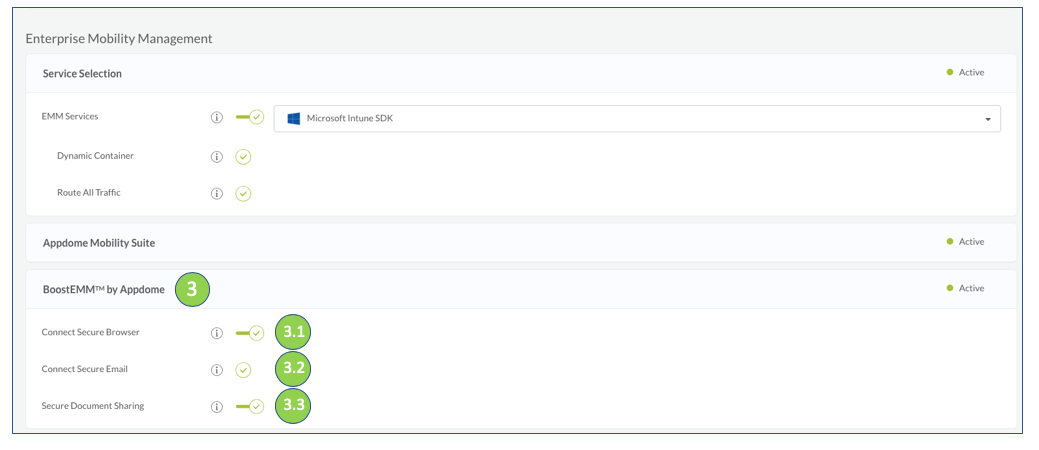
Then, find EMM Services under the Enterprise Mobility Management heading.
- Enable or turn “ON” EMM Services and open the drop-down list.
- Next, choose Microsoft Intune SDK from the dropdown list.
- Open the BoostEMM™ by Appdome section and toggle “ON” the relevant feature you would like to enable:
- Connect Secure Browser – Appdome’s Connect Secure Browser causes a mobile App to open web links using the Microsoft Intune Browser only. This capability helps to secure your organization’s data when the user opens links inside the App that are not accessible outside of the company’s intranet. Note: Before using this feature, make sure Intune secure browser is installed on the device. Download it from the App store, and activate the App using the Intune login settings.
- Connect Secure Email – Appdome’s Connect Secure Email causes a mobile App to send emails using Intune Secure Mail Client only. When the user selects an email link from your secure App, the secure email client will open allowing them to email to the selected address. Note: Before using this feature, make sure the Microsoft Outlook App is installed on the device. Download it from the App store, and activate the App using the Intune login settings.
- Secure Document Sharing – Appdome’s Secure Document Sharing causes a mobile App to restrict document sharing according to EMM policy. When selecting a file via your Intune-fused App, the file will be opened in an Acrobat for Intune secure App and will be shared via the Microsoft Outlook App only. This will prevent opening and sharing your company files via external Apps. Note: Before using this feature, make sure the Acrobat reader for Intune App is installed on the device. Download it from the App store, and activate the App using the Intune login settings.
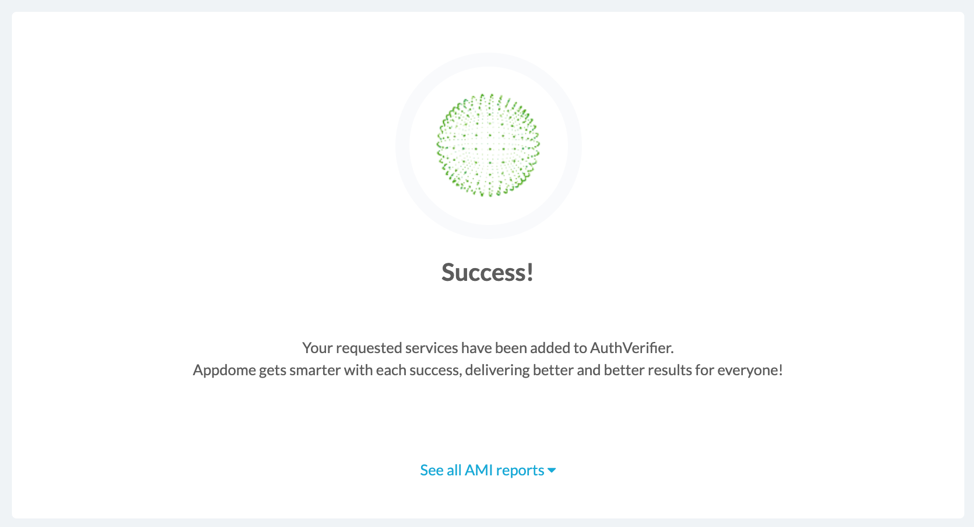
- Click Build My App
The technology behind Build My App has two major elements – (1) a microservice architecture filled with 1000s of code sets needed for mobile integrations, and (2) an adaptive code generation engine that can recognize the development environment, frameworks and methods in each App and match the App to the relevant code-sets needed to add the Microsoft Intune SDK and the requested service to the mobile App in seconds.
Congratulations! When your implementation is complete, you’ll see the notice below. You now have a mobile App fully integrated with Intune SDK and will be able to use Microsoft Secure Browser, Secure Email and secure document sharing as you requested.
Prerequisites
In order to use Appdome’s no-code BoostEMM™ service, you’ll need:
- Appdome account –
- Mobile App (.ipa for iOS, or .apk or .aab for Android)
- Microsoft Intune DLP configuration
- You have a configured and accessible instance of Microsoft Intune (to deploy your App).
How to Activate the Intune Protection Policy on the Built App
In order to verify your built App can use Microsoft’s Secure Browser, Email and Document Sharing, you will need to activate Microsoft Intune Protection Policy on the App using the Intune portal.
Choose New/ Existing Intune Policy
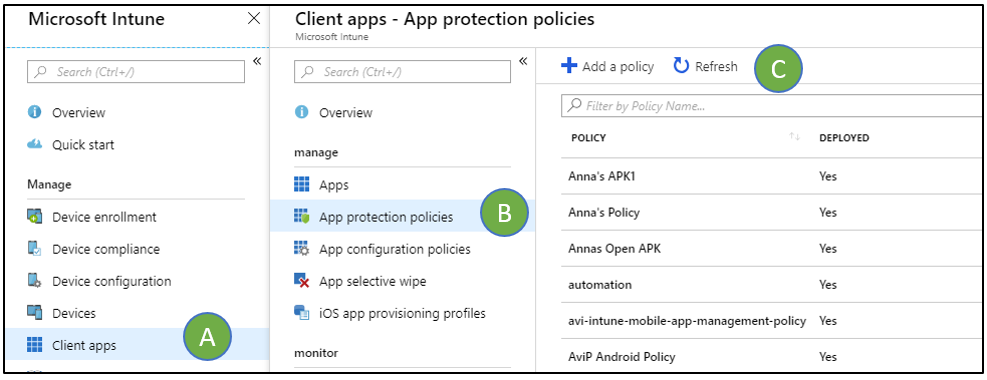
- Login to Microsoft Intune Portal
A. Choose Client Apps
B. Choose App protection Policies
C. Add a new policy or select an existing one. Make sure to create or select a policy according to the app you have selected (iOS/Android).
2. Go to the targeted Apps section and select your App to apply the policy.
Configure the Intune Policy settings to activate your Appdome BoostEMM features
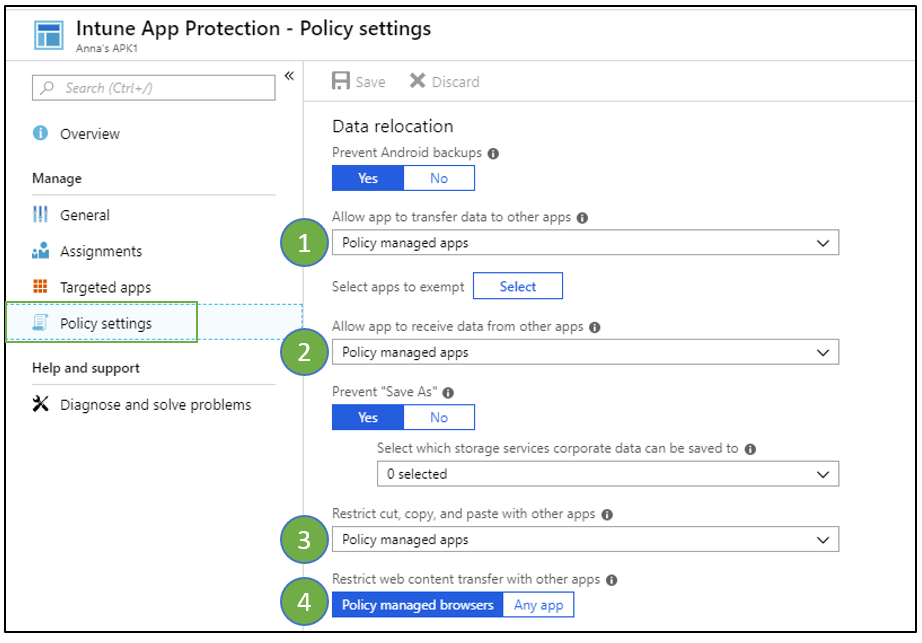
Open the policy settings and set the following configuration:
- Allow app to transfer data to other apps – choose Policy managed apps from the drop-down list
- Allow app to receive data from other apps – choose Policy managed apps from the drop-down listThis will allow the data to be transferred only between policy managed Apps. These settings will activate the Appdome secure email and secure document sharing.
- Restrict cut, copy and paste with other apps – choose Policy managed apps from the drop-down listThis will allow to copy and paste content between policy managed apps only. This setting will activate Appdome copy-paste prevention.
- Restrict web content transfer with other apps – choose Policy managed browsersThis will allow the opening of external URLs with the Intune browser only. This setting will activate the Appdome Secure Browser.
No Coding Dependency
How to Sign & Publish Secured Mobile Apps Built on Appdome
After successfully securing your app using Appdome, there are several available options to complete your project, depending on your app lifecycle or workflow. These include:
- Signing Secure iOS and Android apps
- Customizing, Configuring & Branding Secure Mobile Apps
- Deploying/Publishing Secure mobile apps to Public or Private app stores
Or, see this quick reference Releasing Secured Android & iOS Apps built on Appdome.
How to Learn More
To zoom out on this topic, deploying mobile Apps fused with the Microsoft Intune SDK, read the Appdome for Microsoft Intune datasheet on our website.
Read here to learn more about No-Code Integration of Microsoft Intune SDK Into Mobile Apps and on BoostEMMTM by Appdome.
To ensure your App is properly deployed with Microsoft Intune, make sure to visit Deploying Mobile Apps Fused with the Microsoft Intune SDK.
If you would like to see these features live or start a trial, request a demo. For any questions, please send them our way at support@appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project. If you don’t already have an account, you can sign up for free.