Appdome Mobile Security Suite
Appdome’s Mobile Security Suite is a comprehensive no-code mobile app security solution that delivers best practice mobile security functionality to any iOS/Android app on-demand, with no coding. Appdome’s Mobile App Security Suite includes six categories of security and mobile app protections, covering every major mobile security category.
This Knowledge Base article provides a comprehensive overview of Appdome’s Mobile App Security Suite.
Mobile App Security Made Easy
Using Appdome, there are no development or coding prerequisites. For example, there is no Appdome SDK, libraries, or plug-ins to implement mobile app security. Appdome’s Mobile App Security Suite can be added to any iOS or Android app in seconds, with no code or coding.
On Appdome, users merely upload and Android (.apk or .aab) or iOS (.ipa) app, select the new features, SDKs or APIs needed in the apps, and click “Build My App.” There is no development or coding dependencies, no wrappers and no limitation on the development environment used to build the app. Appdome’s technology adds the new features to the mobile app as if the new features were natively coded to the app. Appdome is compatible with all Android and iOS mobile apps, including apps built natively and in non-native development environments like React Native, Cordova, and Maui, Xamarin.
Generally speaking, using Appdome requires public data only. For example, Appdome users upload mobile app binaries only (not source code) and implement mobile service vendor SDKs and APIs (all of which are publicly available). Even so, Appdome uses several safeguards to ensure that mobile apps are not malicious, user and project data are safe and access is controlled. Our goal is to protect our users and protect the use of Appdome to facilitate the broad adoption of our service.
The Complete List of Appdome Mobile App Security Suite
Below is a comprehensive listing of all categories, features, and options available in the Appdome Mobile App Security Suite.
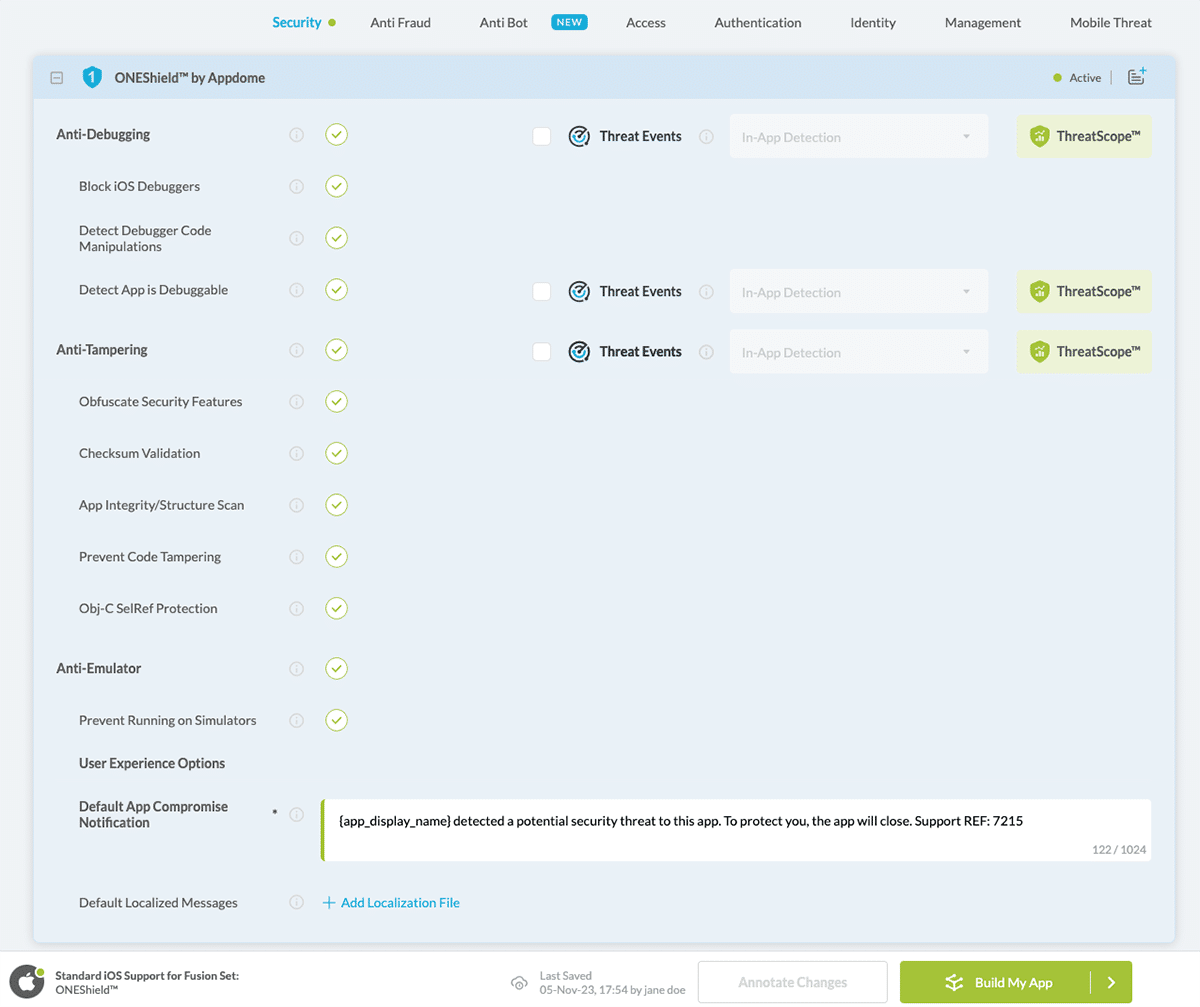
ONEShield™ App Shielding/Hardening (RASP)
- Anti-Debugging – Protects the app against malicious debugging.
-
Block iOS Debuggers – Enable Appdome’s anti-debugging methods to protect the app from debugging attempts.
- Detect Debugger Code Manipulations – Actively detects dynamic injection code manipulations performed by debuggers at run-time.
-
Detect App is Debuggable– Detect if the app has been re-signed with a certificate with debug entitlements.
- Anti-Tampering – Protects the app from unauthorized changes.
- Obfuscate Security Features – Obfuscate sources and strings of Appdome-build code.
- Checksum Validation – Performs a checksum validation on the app to verify app integrity (to ensure the app has not been modified since it was published).
- App Integrity/Structure Scan – Performs a structure scan of the app to validate proper app structure and integrity
- Prevent Code Tampering – Detect permanent application main executable code changes.
- Obj-C SelRef Protection – Perform checksum validation on the application’s main executable selref section.
- Anti Reversing – Encrypts key logical elements and resources within your application such as methods, strings, and assets.
- Prevent Running on Simulators/Emulators – Protects the app by restricting execution to physical mobile devices only. Mobile simulators and emulators are software applications used on a computer as a virtual machine of a mobile device. They are often used to create virtual environments for hackers to scale their attacks, obtain/elevate root permissions, and perform reverse engineering, and hack mobile games.
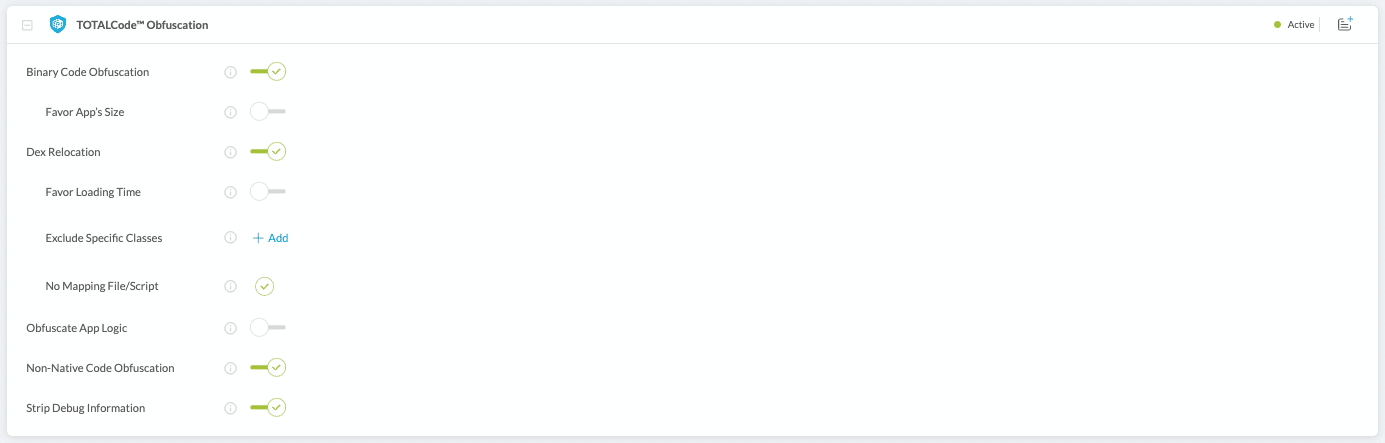
TOTALCode™Obfuscation:
- Binary Code Obfuscation – Obfuscates native code and libraries at the binary level.
- Flow Relocation – Obfuscates control flows and business logic across the app binary to prevent dynamic and static analysis, tracing the source code etc.
- Non-Native Code Obfuscation – Obfuscates non-native code and libraries including JavaScript and/or DLL files for React Native, Cordova, Maui, Xamarin apps.
- Strip Debug Information – This feature removes source code file names, line numbers, and variable names, symbols.
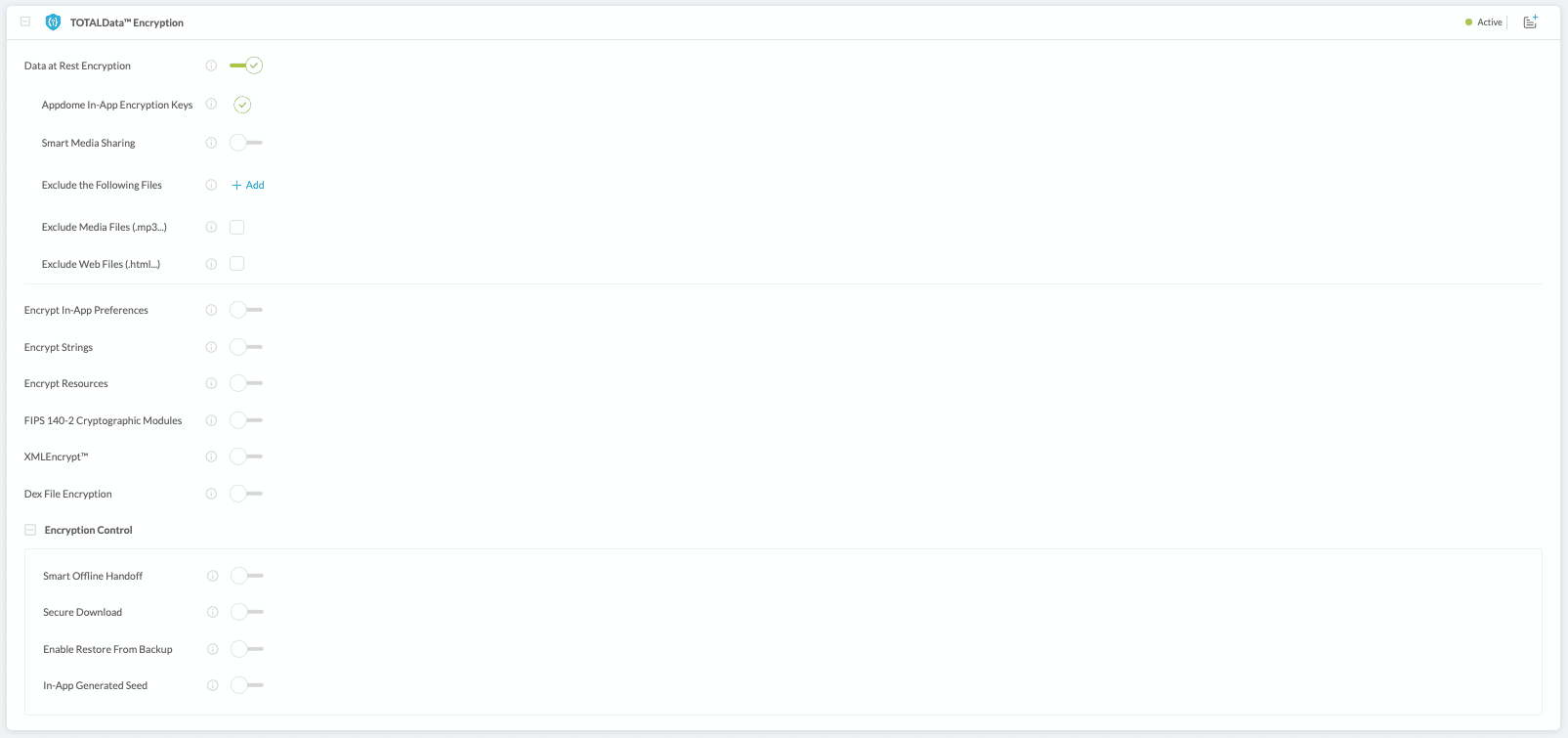
TOTALDataTM Encryption
- Data at Rest Encryption – Protects the data the application creates on the device. It will also create a secure data container that will prevent other applications from accessing the app’s encrypted data and prevent the same application on a different device to open this encrypted data as well.
-
Encrypt and decrypt media files– With this option enabled, Android MediaPlayer can access encrypted media files, regardless of how the application accesses its files.
- Exclude Media Files -With this option enabled, media files can be shared to leverage external media apps and browsers
- Exclude Web Files – With this option enabled, local web file caching is enabled and will not be encrypted for web-intense apps.
-
- Encrypt In-App Preferences – Encrypt all configuration files under/shared-prefs in Android and specific keys under NSUserDefaults in iOS.
- Encrypt Stings and Resources – Encrypts all CFStrings in iOS apps and all Java strings and the assets folder in Android.
- Secure Offline Access to encrypted data – With this option enabled, Apps developers that require authentication can enable non-authenticated access to some of the files that the app generates.
- In addition, Appdome offers encryption controls for different app needs:
- Smart Offline Handoff – With this option enabled, Appdome will decrypt the app’s data only after authentication with a remote server. Additionally, the developer can specify a folder for offline file access, and specify restriction for offline access to that folder.
- Enable Restore From Backup – With this option enabled, the encryption key will be independent of device data, so migrating or restoring the device will not affect access to encrypted data.
- In-App Generated Seed – With this option enabled, the app will seed the TotalData-Encryption-Key via event. Until the key is seeded, no files will be encrypted.
- FIPS 140-2 Cryptographic Modules – Uses FIPS140-2 certified cryptographic modules to handle all data in transit
- Encrypt Java Classes (.DEX files) – Obfuscates and encrypts compiled Java code (ie: Java Classes, aka .DEX files). Only decrypts it during the run time while the app is used, then encrypts it again after use. APPCode Packer is compatible with mobile apps built with any development environment including Maui, Xamarin, Cordova, native Android apps, React Native, Ionic, and more app environments.
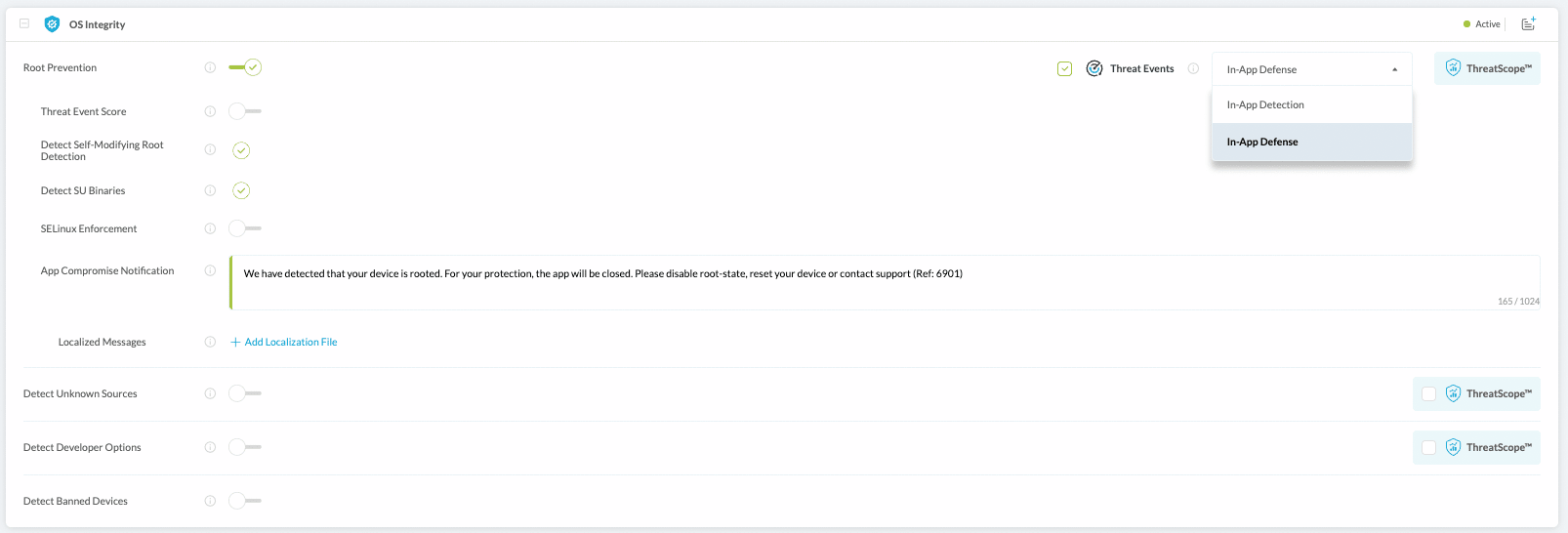
OS Integrity
- Root or Jailbreak Prevention – prevents users from running apps on devices that have been jailbroken (iOS) or rooted (Android).
- Detect SELinux Enforcement – Prevents users from running your Appdome built app on devices with no SELinux enforcement.
- Detect Unknown Sources – Prevents users from running your built app when they’ve enabled “allow app install from unknown sources” native OS setting is enabled on the device.
- Detect Developer Options – Prevents apps with “developer options” OS setting on their devices they will not be able to run your app.
- Detect Banned Devices – detects if the app is running on untrusted or banned devices.
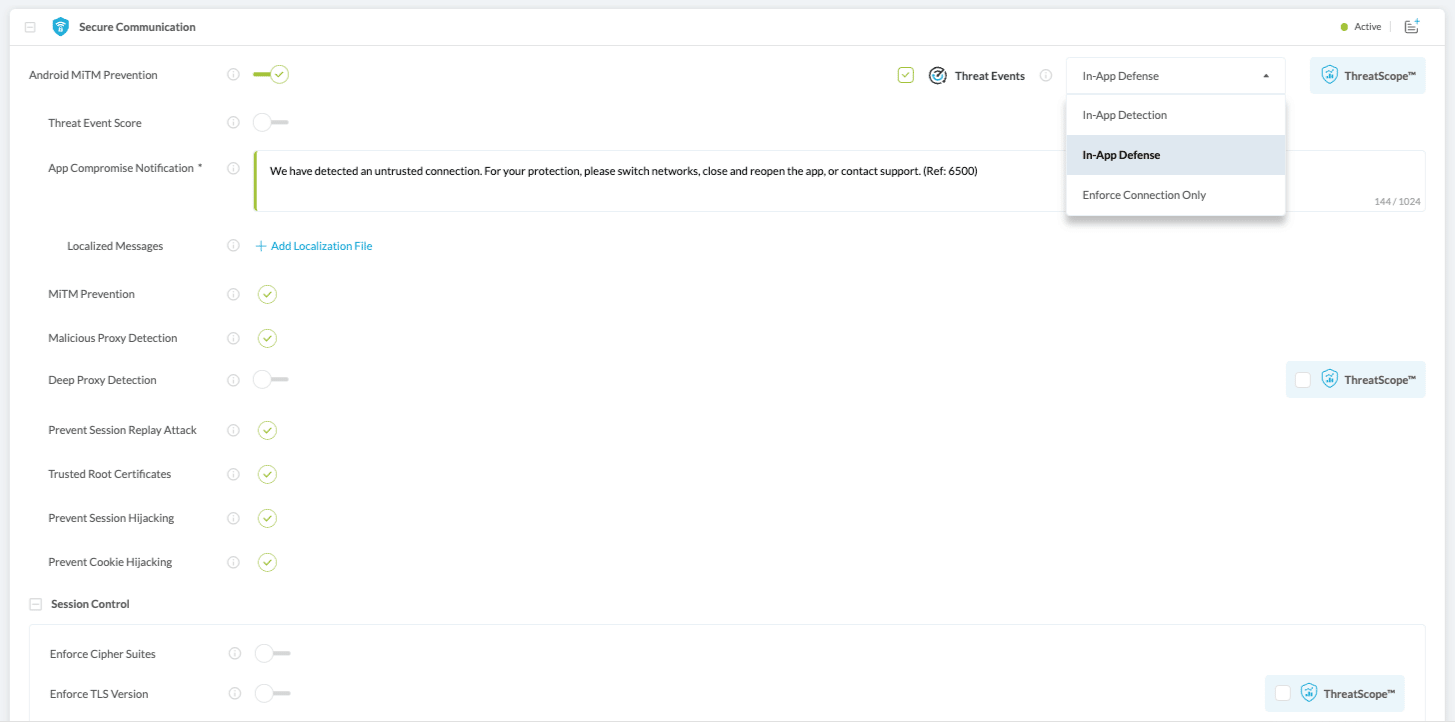
- Appdome-Threat Events – Lets developers change the default enforcement action upon detected threats. Appdome can pass enriched events or event metadata back to the app so that the app’s own internal event structure, or a 3rd party threat response tool can handle the enforcement action after Appdome detects a threat. When In-App Event handling is enabled (ie: the toggle switch is ON), the event is handled by a mechanism within your app. When In-App Event Handling is OFF, the Appdome Security engine handles the event (usually resulting in the app Exiting after displaying a notification to the end-user).
Secure Communication
-
- MitM Prevention – Performs automatic session validation on all attempted connections with the mobile app. Actively validates the session state machine, TLS certificates.
- Malicious Proxy Detection – detects and prevents MItM attacks on the application by preventing connections to unknown, untrusted, malicious proxies, or other intermediary devices.
- Prohibit Stale Sessions – detects and prohibits reused sessions and reclaimed SessionIDs.
- Trusted Root Certificates – In-app list of worldwide trusted CAs, independent from any CAs manually added to the device (you can add CAs to this list with Trusted CA Pinning).
- FIPS 140-2 Encryption Modules – implement FIPS 140-2 Compliant Cryptographic Modules in the communication.
- Appdome also offers additional controls to manages the mobile app’s communication sessions:
- Secure Certificate Pinning – Pin trusted certificates to the app, that will be added to the session validation.
- Enter the Service Domain, Pinning Scheme, and Certificates for SecureAPI to verify certificates for these domains on all network connections in the app.
- Enforce Cipher Suites – Limit allows cipher suites to a pre-defined list.
- Enforce TLS Version – Limit communication to TLS version 1.2.
- Enforce Strong RSA Signature – enforces leaf and intermediary certificates received from the server to be signed with a Rivest-Shamir-Adleman (RSA) key with a length of at least 2048 bits.
- Enforce Strong ECC Signature – enforces leaf and intermediary certificates received from the server to be signed with an Elliptic-Curve Cryptography (ECC) key with a size of at least 256 bits.
- Enforce SHA256 Digest – enforce server certificate signatures to use at least a SHA256 certificate hashing algorithm.
- Enforce Certificate Roles – Protect against MitM attacks using certificates signed by unauthorized leaf certificates.
- IP Address Visibility – Make real IP addresses visible to the built app.
- Permit DNS over TCP – allow DNS connections requests over TCP (rather than UDP) to pass undisrupted.
- Static Client Pinning – Pin a static client certificate to authenticate connections.
- Secure Certificate Pinning – Pin trusted certificates to the app, that will be added to the session validation.
- URL Whitelisting – Ensures that the built app can only connect to a trusted set of destinations or hosts, that you must specify in the URL List setting.
Appdome’s App Security Suite is perfect for mobile developers to help them release secure apps from the first use. Building apps on Appdome don’t impact your app functionality or add time to your development cycle. It’s fast, easy, and non-intrusive.
How Do I Learn More?
Please view our video on building app(s) with security end-to-end here.
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform or request a demo at any time.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project. If you don’t already have an account, you can sign up for free.