How to Sign Secured iOS Apps Using Appdome's Auto-Dev Private Signing Script
Code signing is a prerequisite for installing any app on a mobile iOS device. A valid signature, which uses an Apple-issued certificate, ensures the integrity of an app and stands as proof that the app comes from a known and approved source and has not been tampered with. By enforcing mandatory code signing, Apple ensures that no third-party app loads unsigned code resources or uses self-modifying code.
During the Appdome app build process, adapters are added to the app to achieve the functionality requested. As a result, the app’s original signature is invalidated and must be resigned to allow deploying the app on mobile devices.
Appdome allows signing an app via the Sign tab using any of the following methods:
- On Appdome
Allowing Appdome to take care of the entire signing process. You only need to provide the signing credentials. For details, see the topic How to Sign Secured iOS Apps without Xcode.
- Private Signing
Gives you full responsibility for handling the entire signing process. For further information and in-detail instructions, see the topic How to Privately Code Sign Sealed iOS Apps using DevSecOps Build System.
- Auto-DEV Private Signing
Allows you to sign the app without uploading the signing certificate to Appdome’s cloud service.
Appdome provides you with a script (.sh file), which runs on your trusted environment and signs the app by using your credentials (certificate and password) as input. For details, see the topic How to Automate Secure iOS App Code Signing in DevOps CI/CD.
As part of the Appdome signing process of secured iOS apps, by using either Auto-dev Private Signing or Signing on Appdome, you are required to extract and upload a Provisioning Profile and an entitlement file for each executable in the app, and when using signing on Appdome, a P12 certificate and its password.
This article provides instructions for automating secure iOS App code signing in DevOps CI/CD.
Prerequisites for Using Appdome’s Auto-DEV Private Signing Script
- Appdome account – IDEAL or Higher.
- Appdome-DEV access
- iOS Mobile App
- Signing Credentials (namely, P12 certificate and its password, entitlement files, and provisioning profile) – verify that the certificate was added to your local Keychain.
- Mac OS X computer with:
- Python software (version 2.7 or higher)
- Codesign – Apple utility that adds the signature directly to the executable file (Xcode version 10.1 or higher). You can check if the tool is available to you simply by running “which codesign” on your terminal.
How to Securely Automate iOS App Signing In CI/CD
With Appdome, you can Securely Automate iOS App Signing within a CI/CD without uploading the signing certificate to Appdome’s cloud service.
Appdome’s Auto-Dev Private Signing iOS Apps script allows users to sign built-in apps locally without uploading the signing certificate to Appdome’s cloud service. The unsigned app is embedded in the script generated by Appdome. Running the script in a trusted environment extracts and signs the app using a certificate in your key chain.
3 Easy Steps to Securely Automate iOS App Signing In CI/CD
Follow these step-by-step instructions to securely automate iOS app signing in CI/CD:
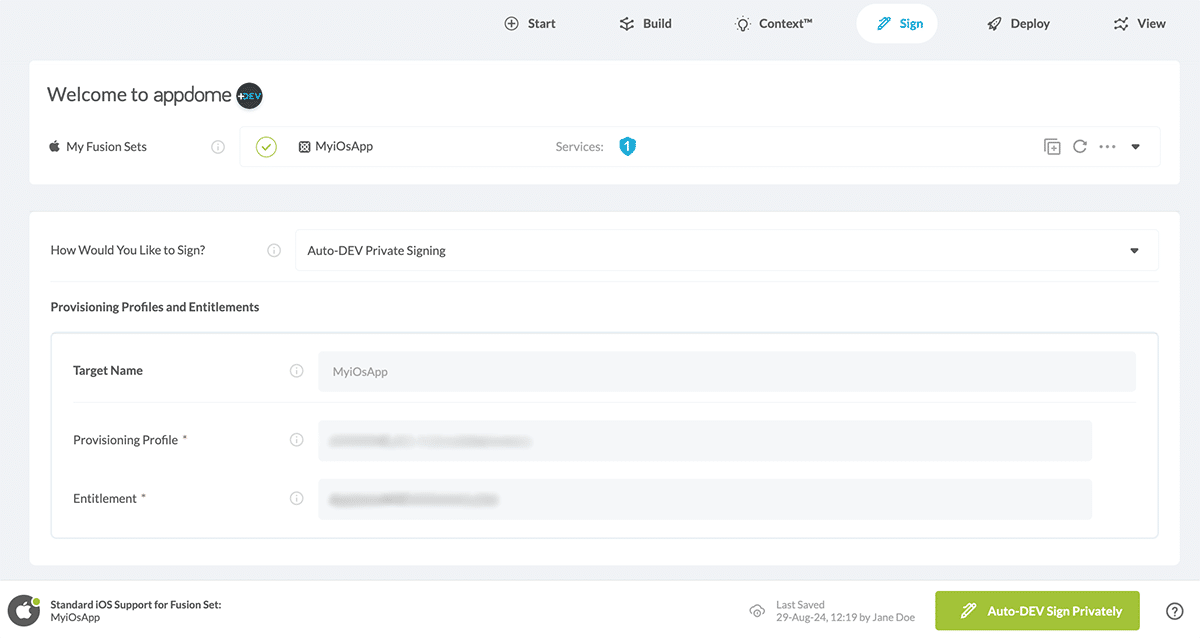
- From within the Sign tab, select the signing method Auto-DEV Private Signing.
- Upload the Provisioning Profile that matches your signing certificate, wait for Appdome to verify the signing parameters, and then click on the Auto-DEV sign Privately button.
Note: If your application contains multiple executable files, you must upload a provisioning profile for each file.
Optional: Toggle ON the option Manual Entitlements Matching if you want to set an entitlement plist file to use when signing an app on Appdome.
When this feature is off, Appdome creates an entitlements file based on the entitlements used to sign the non-protected app.
For further details and an in-depth manual on obtaining the entitlement file for your app, see the topic “How to Extract and Use iOS Entitlements Files for Signing Secure iOS Apps.” -
When the Signing Script Generation is complete, click Next.
-
Click Download My Built App to download the automatic private signing script (sign.sh).
Your Appdome-Built unsigned app is embedded in this script.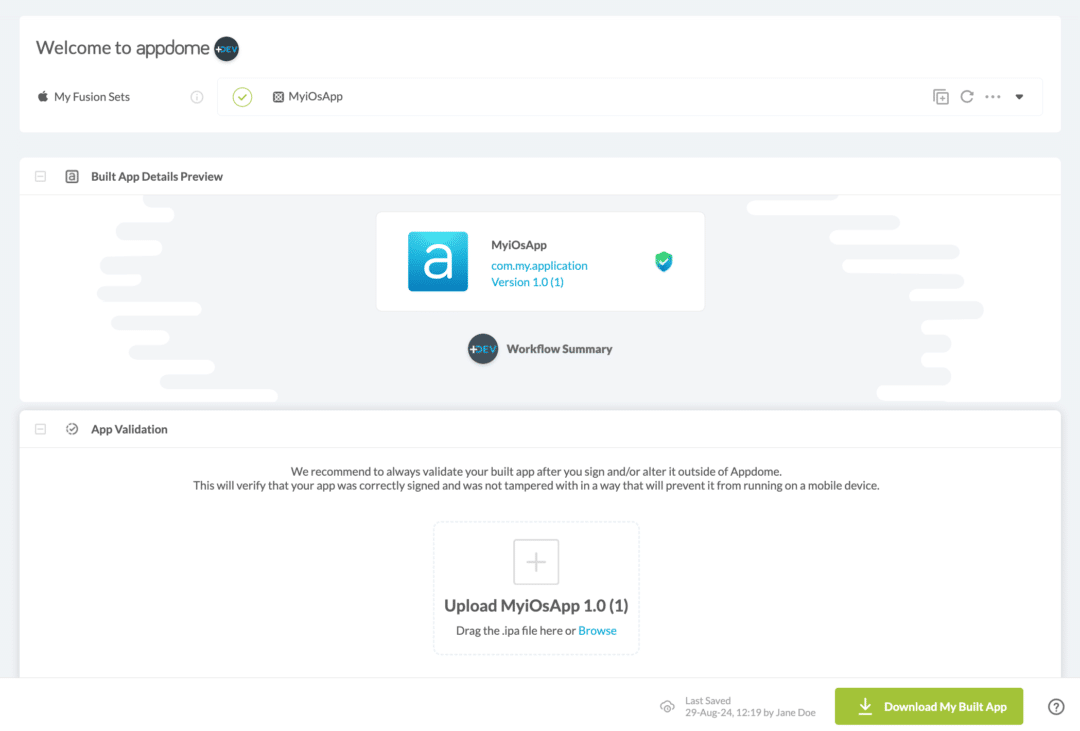
Optional: Save or Remove Signing Credentials
Appdome allows saving signing credentials to streamline future signing processes.
Additionally, if the signing credentials are no longer needed or need to be updated, they can be removed directly from the Sign Tab by clicking the Remove Signing Credentials button.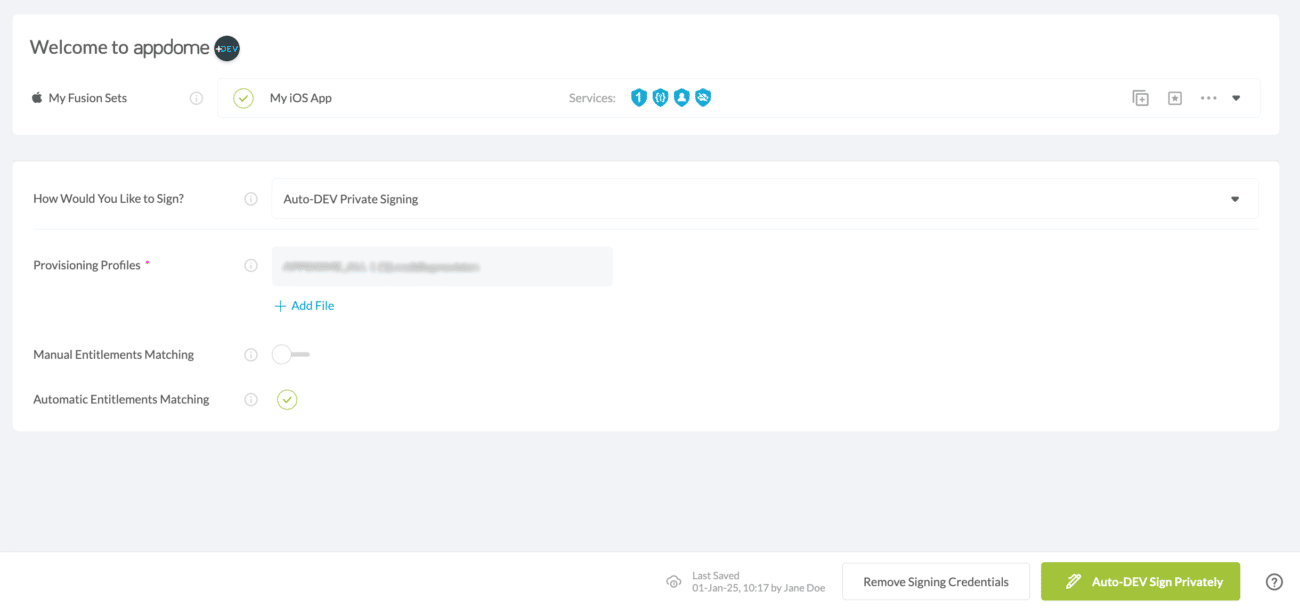
How to Run Auto-DEV Private Script:
To run the automatic private signing script, execute the following command:
./sign.sh --signer <"Signer Identity" or sha-1 hash> --output <signed_app_name>.ipa
For additional details about signer identities and P12 files, see topic P12 certificate and its password.
If you need help finding the value to enter for the Signer Identity, you can run this command:
./sign.sh --help
Note!
In some environments, you may be required to grant executable permissions to the signing script (using chmod +x command):
chmod +x sign.sh
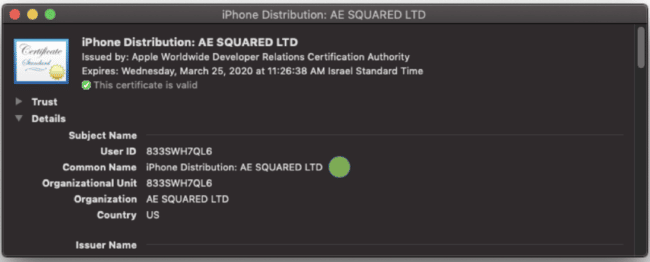
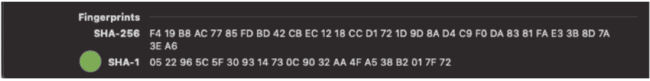
The Signer Identity is how the script identifies the certificate in the work stations Keychain Access. You can use either the certificate’s common name (marked with double quotes) or its SHA-1 fingerprint.
To extract the certificate common name / SHA-1 fingerprint:
- On your computer, open the Keychain Access app.
- Select the certificate you would like to add.
- Open the options menu (left click) and select Get info.
- Get the certificate common name / SHA-1 fingerprint.
Important Note!
Codesign needs authorized access to your signing certificate in the Keychain. The password for your keychain is normally your user’s password (the one used for logging in to your computer). To ensure that the automatic private signing script runs without interruptions, you are strongly advised to set the option “Always Allow for authorized access to the Keychain.”
Now, you can run the automatic private signing script with your Signer Identity value.
Troubleshooting
If you have multiple certificates with the same common name, the script prompts you to use the SHA-1 fingerprint (which is always unique). If you enter invalid identifiers (type or non-existent certificate), the script will display an error and print all of the valid identities:
$ ./sign.sh --signer <invalid_singer> --output signed_app.ipa >>> ERROR: The identity: invalid_signer was not found in the keychain. Valid identities by name are: iPhone Distribution: Valid identities by sha-1 are:
The script notifies whether the Signer Identity you are trying to use does not match the provisioning profile that is used for sealing the app and shows you the valid identities:
$ ./sign.sh --signer <mismatched_singer> --output signed_app.ipa >>> 'INFO: Successfully matched certificate SHA-1 fingerprint [] in keychain ERROR: The input certificate doesn"t match the provisioning profile. Valid certificates are: Cert: [iPhone Distribution: ], with fingerprint: []
How Do I Learn More?
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Related Articles:
- How to Privately Code Sign Sealed iOS Apps
- How Appdome Enables Signing Secured iOS Apps without Xcode
- Automated App Signing of Secured Android & iOS Apps on Appdome
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project. If you don’t already have an account, you can sign up for free.