How to Block Resigning and Repackaging Android Apps
Learn to Prevent App Repacking in Android apps, in mobile CI/CD with a Data-Driven DevSecOps™ build system.
What is App Repackaging?
App repacking involves hackers manipulating an app’s original code or injecting harmful code into it, subsequently repackaging this altered app for distribution. By actively preventing app repacking, you not only preserve the authenticity and originality of your app but also ensure the continuous safety and trust of your users.
To ensure your app is protected against unauthorized changes or any modification that can compromise them is critical. Some examples are:
- Repackaging the app
- Resigning the application
- Modifying the application’s executable
- iOS: Main executable (see structure of an iOS application)
- Android: DEX files (see structure of an Android application)
- Attempting to Modify the Appdome adapter
- Moving the application’s sandbox under the name of a different package
Why Prevent App Repacking in Android Apps??
Tamper prevention against app repackaging protects your app against unwanted changes, mods, and hacks that can negative impact or compromise your mobile business application including financial and data loss, intellectual privacy & repetitional damage. Appdome prevents all this without adding development work or time to your release cycles. This is done by sealing your app and actively detecting modifications during initialization and at multiple other points during run-time.
Prerequisites for Using Prevent App Repacking:
To use Appdome’s mobile app security build system to Prevent App Repacking , you’ll need:
- Appdome account (create a free Appdome account here)
- A license for Prevent App Repacking
- Mobile App (.apk or .aab for Android)
- Signing Credentials (see Signing Secure Android apps and Signing Secure iOS apps)
Prevent App Repacking on Android apps using Appdome
On Appdome, follow these 3 simple steps to create self-defending Android Apps that Prevent App Repacking without an SDK or gateway:
-
Upload the Mobile App to Appdome.
-
Upload an app to Appdome’s Mobile App Security Build System
-
Upload Method: Appdome Console or DEV-API
-
Android Formats: .apk or .aab
-
Prevent App Repacking Compatible With: Java, JS, C++, C#, Kotlin, Flutter, React Native, Unity, Xamarin, Cordova and other Android apps
-
-
Build the feature: Prevent App Repacking.
-
Building Prevent App Repacking by using Appdome’s DEV-API:
-
Create and name the Fusion Set (security template) that will contain the Prevent App Repacking feature as shown below:
-
Follow the steps in Sections 2.2.1-2.2.2 of this article, Building the Prevent App Repacking feature via Appdome Console, to add the Prevent App Repacking feature to this Fusion Set.
-
Open the Fusion Set Detail Summary by clicking the “...” symbol on the far-right corner of the Fusion Set, as shown in Figure 1 above, and get the Fusion Set ID from the Fusion Set Detail Summary (as shown below):
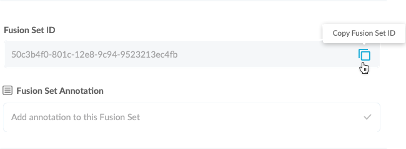
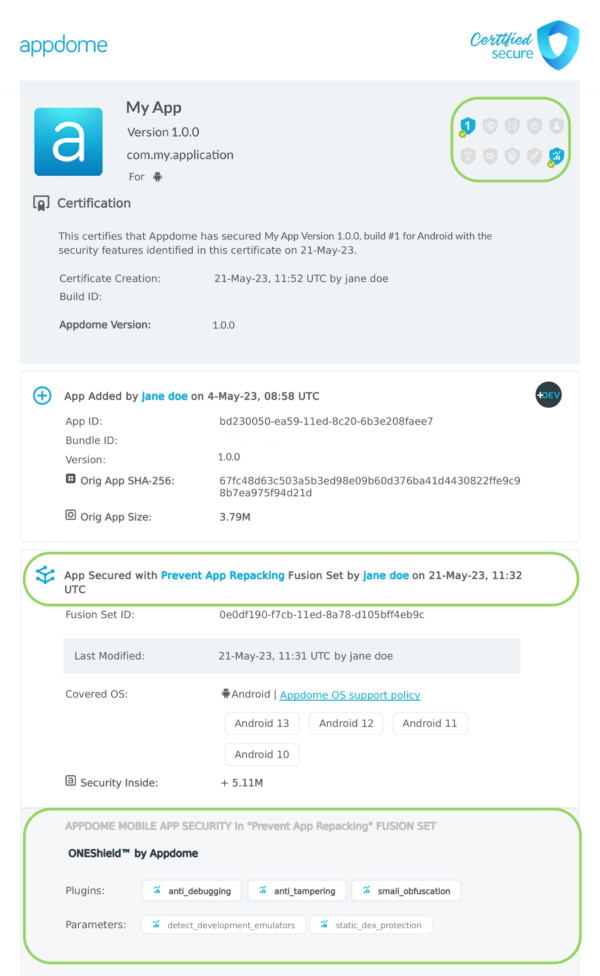
Figure 2: Fusion Set Detail Summary
Note: Annotating the Fusion Set to identify the protection(s) selected is optional only (not mandatory). -
Follow the instructions below to use the Fusion Set ID inside any standard mobile DevOps or CI/CD toolkit like Bitrise, App Center, Jenkins, Travis, Team City, Cirlce CI or other system:
-
Build an API for the app – for instructions, see the tasks under Appdome API Reference Guide
-
Look for sample APIs in Appdome’s GitHub Repository
-
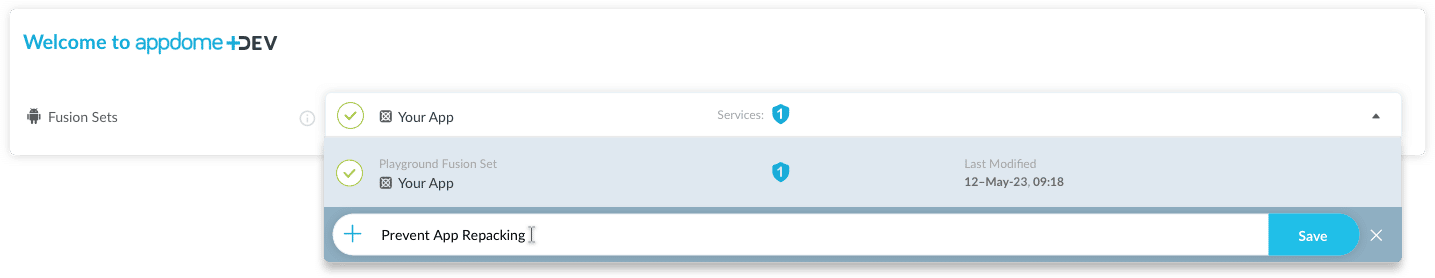
Figure 1: Fusion Set that will contain the Prevent App Repacking feature
Note: Naming the Fusion Set to correspond to the protection(s) selected is for illustration purposes only (not required). -
-
Building the Prevent App Repacking feature via Appdome Console
To build the Prevent App Repacking protection by using Appdome Console, follow the instructions below.
-
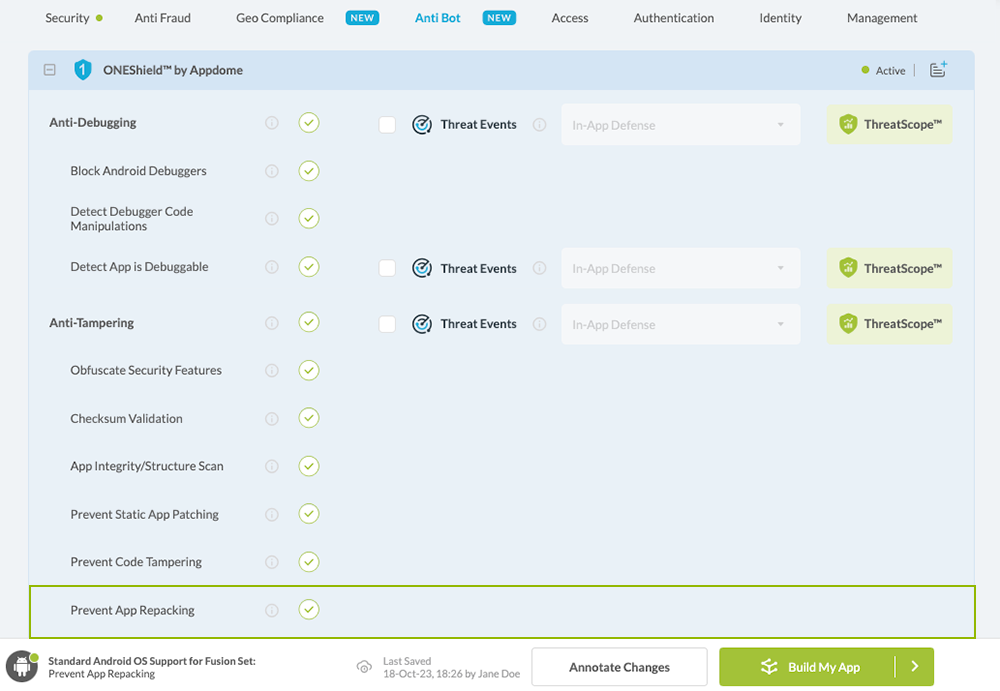
Where: Inside the Appdome Console, go to Build > Security Tab > ONEShield™ section.
-
When you select the Prevent App Repacking you'll notice that your Fusion Set you created in step 2.1.1 now bears the icon of the protection category that contains Prevent App Repacking
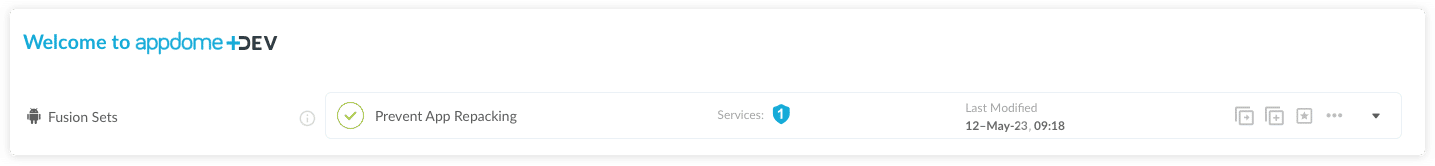
Figure 4: Fusion Set that displays the newly added Prevent App Repacking protection
-
Click Build My App at the bottom of the Build Workflow (shown in Figure 3).
-
Congratulations! The Prevent App Repacking protection is now added to the mobile app -
Using Appdome, there are no development or coding prerequisites to build secured Android Apps by using Prevent App Repacking. There is no SDK and no library to code or implement in the app and no gateway to deploy in your network. All protections are built into each app and the resulting app is self-defending and self-protecting.
Releasing and Publishing Mobile Apps with Prevent App Repacking
After successfully securing your app by using Appdome, there are several available options to complete your project, depending on your app lifecycle or workflow. These include:
- Customizing, Configuring & Branding Secure Mobile Apps
- Deploying/Publishing Secure mobile apps to Public or Private app stores
- Releasing Secured Android & iOS Apps built on Appdome.
Related Articles:
- How to Block Runtime Code Manipulations in Android & iOS Apps
- How to Prevent Debuggable Android & iOS Apps in Production
- Running a Checksum Validation of Android & iOS Apps
- How to Prevent Android Apps from Running on Emulators
- How to Prevent iOS Apps from Running on Emulators
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.