How to Detect Virtual Space Using AI
This Knowledge Base article describes how to use Appdome’s AI in your CI/CD pipeline to continuously deliver plugins that Detect Virtual Space in Android apps.
What Is Virtual Space?
Virtual Space enables multiple instances of Android to run within a controlled virtual environment rather than on physical devices. While virtualization has legitimate uses, such as app testing and development, attackers exploit it to bypass app security mechanisms, analyze app behavior, and extract sensitive data. Virtual environments are often used to manipulate app workflows, evade purchase restrictions, and automate fraudulent activities, such as mass account creation or in-app transaction exploits. These attacks pose significant risks to app integrity, financial security, and user data. Detecting and managing virtualization is critical for mitigating these threats and complying with security standards like PCI DSS, which require secure environments for apps handling sensitive data.
How Appdome Protects Mobile Apps Against Virtual Space?
Appdome’s dynamic Detect Virtual Space plugin identifies and blocks apps from running in virtualized environments. By analyzing system properties, app behavior, and virtual instance identifiers, Appdome ensures that unauthorized virtualization tools cannot bypass app security. This defense protects against attacks such as automated fraud, purchase evasion, and data extraction, maintaining app integrity in secure environments. Mobile developers can use Appdome’s Threat-Events™ to gather data on virtualization events and create customized responses when such threats are detected.
Prerequisites for Using Appdome's Detect Virtual Space Plugins:
To use Appdome’s mobile app security build system to Detect Virtual Space , you’ll need:
- Appdome account (create a free Appdome account here)
- A license for Detect Virtual Space
- Mobile App (.apk or .aab for Android)
- Signing Credentials (see Signing Secure Android apps and Signing Secure iOS apps)
How to Implement Detect Virtual Space in Android Apps Using Appdome
On Appdome, follow these 3 simple steps to create self-defending Android Apps that Detect Virtual Space without an SDK or gateway:
-
Designate the Mobile App to be protected.
-
Upload an app via the Appdome Mobile Defense platform GUI or via Appdome’s DEV-API or CI/CD Plugins.
-
Android Formats: .apk or .aab
-
Detect Virtual Space is compatible with: Java, JS, C++, C#, Kotlin, Flutter, React Native, Unity, Xamarin, Cordova and other Android apps.
-
-
Select the defense: Detect Virtual Space.
-
-
Follow the steps in Sections 2.2-2.2.2 of this article to add the Detect Virtual Space feature to your Fusion Set via the Appdome Console.
-
When you select the Detect Virtual Space you'll notice that the Fusion Set you created in step 2.1 now bears the icon of the protection category that contains Detect Virtual Space.
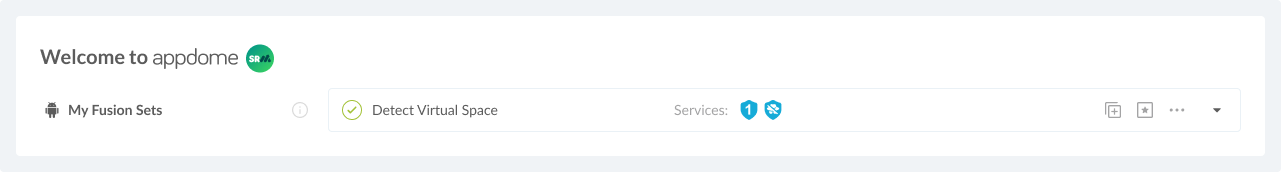
Figure 2: Fusion Set that displays the newly added Detect Virtual Space protection
Note: Annotating the Fusion Set to identify the protection(s) selected is optional only (not mandatory). -
Open the Fusion Set Detail Summary by clicking the “...” symbol on the far-right corner of the Fusion Set. Copy the Fusion Set ID from the Fusion Set Detail Summary (as shown below):
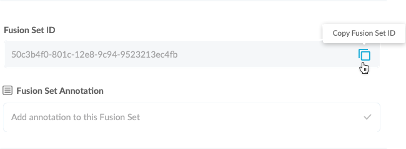
Figure 3: Fusion Set Detail Summary
-
Follow the instructions below to use the Fusion Set ID inside any standard mobile DevOps or CI/CD toolkit like Bitrise, Jenkins, Travis, Team City, Circle CI or other system:
-
Refer to the Appdome API Reference Guide for API building instructions.
-
Look for sample APIs in Appdome’s GitHub Repository.
-
Create and name the Fusion Set (security template) that will contain the Detect Virtual Space feature as shown below: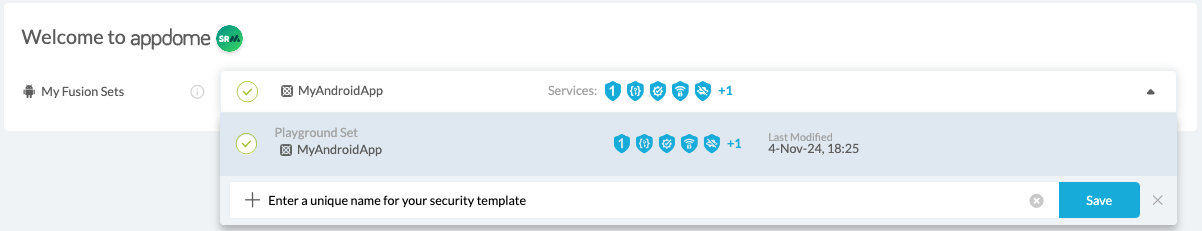
Figure 1: Fusion Set that will contain the Detect Virtual Space feature
-
-
Add the Detect Virtual Space feature to your security template.
-
Navigate to Build > Anti Fraud tab > Mobile Fraud Detection section in the Appdome Console.
-
Toggle On > Detect Virtual Space.
(a) Choose to monitor this attack vector by checking the Threat Events checkbox associated with Detect Virtual Space as shown below.
(b) To receive mobile Threat Monitoring, check the ThreatScope™ box as shown below. For more details, see our knowledge base article on ThreatScope™ Mobile XTM.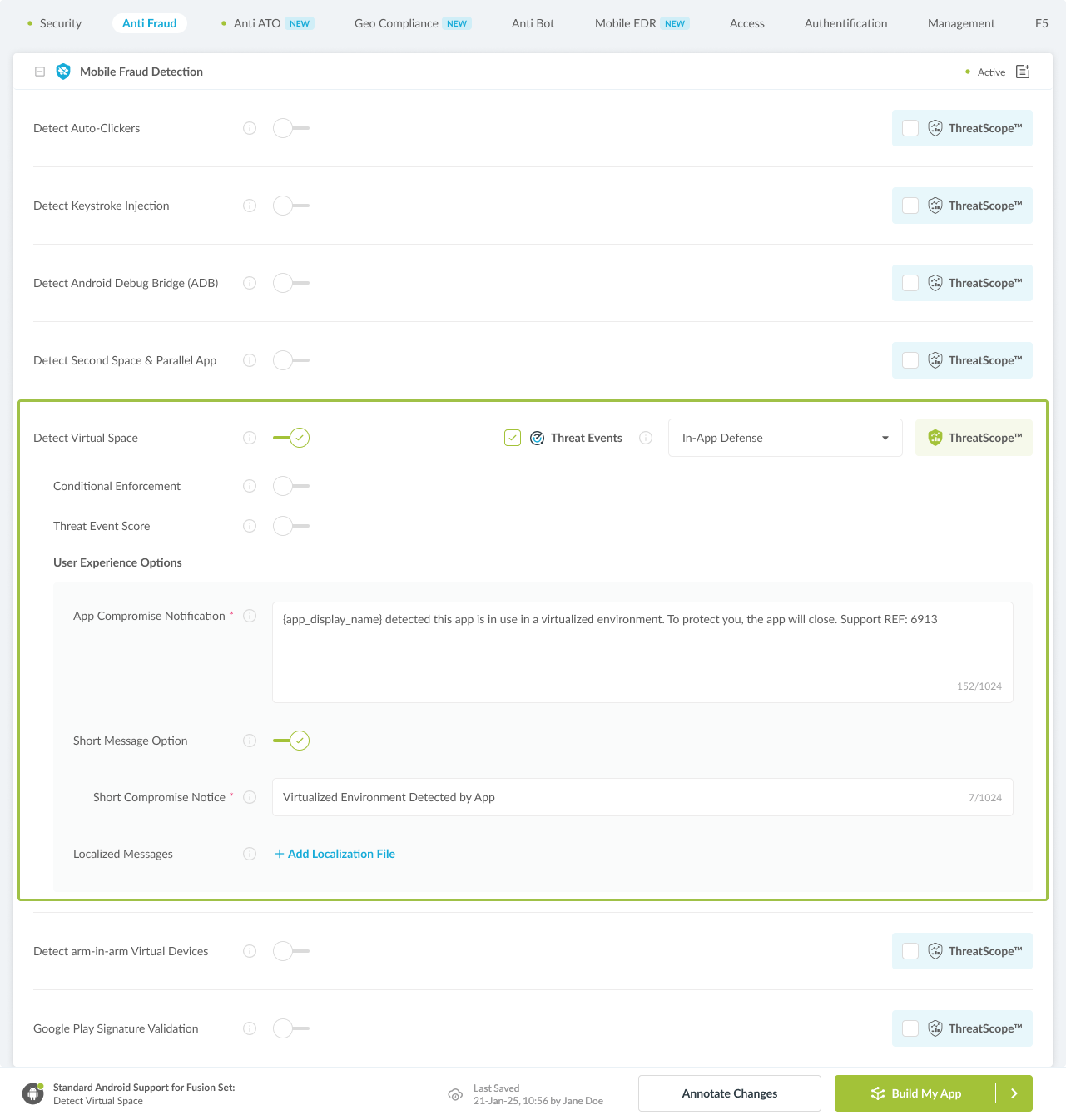
Figure 4: Selecting Detect Virtual Space
Note: The Appdome Platform displays the Mobile Operation Systems supported by each defense in real-time. For more details, see our OS Support Policy KB. -
Select the Threat-Event™ in-app mobile Threat Defense and Intelligence policy for Detect Virtual Space:
-
Threat-Events™ OFF > In-App Defense
If the Threat-Events™ setting is not selected. Appdome will detect and defend user and app by enforcing Detect Virtual Space.
-
Threat-Events™ ON > In-App Detection
When this setting is used, Appdome detects a virtualized environment in use with the mobile app and passes Appdome’s Threat-Event™ attack intelligence to the app’s business logic for processing, enforcement, and user notification. For more information on consuming and using Appdome Threat-Events™ in the app, see section Using Threat-Events™ for Detect Virtual Space Intelligence and Control in Mobile Apps.
-
Threat-Events™ ON > In-App Defense
When this setting is used, Appdome detects and defends against Virtual Space (same as Appdome Enforce) and passes Appdome’s Threat-Event™ attack intelligence to the app’s business logic for processing. For more information on consuming and using Appdome Threat-Events™ in the app, see section Using Threat-Events™ for Detect Virtual Space Intelligence and Control in Mobile Apps.
-
-
Configure the User Experience Options for Detect Virtual Space:
With Threat-Events™ OFF, Appdome provides several user experience options for mobile brands and developers.- App Compromise Notification: Customize the pop-up or toast Appdome uses to notify the user when a threat is present while using the protected mobile app.
- Short message Option. This is available for mobile devices that allow a banner notification for security events.
-
Localized Message Option. Allows Appdome users to support global languages in security notifications.
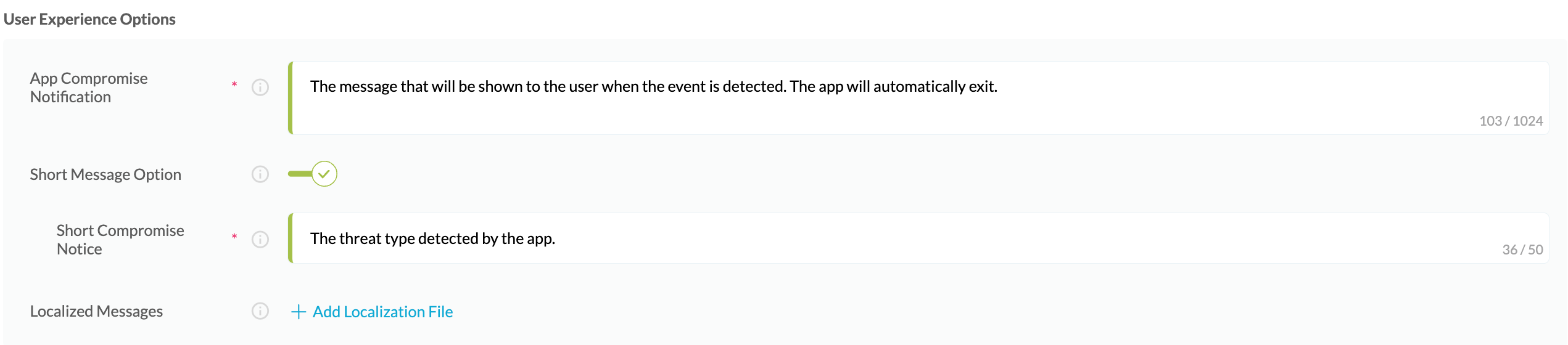
Figure 5: Default User Experience Options for Appdome’s Virtual Space
-
Detect Virtual Space Threat Code™. Appdome uses AI to generate a unique code each time Detect Virtual Space is triggered by an active threat on the mobile device. Use the code in Appdome Threat Resolution Center™ to help end users identify, find and resolve active threats on the personal mobile devices.
-
Congratulations! The Detect Virtual Space protection is now added to the mobile app -
-
Certify the Detect Virtual Space feature in Android Apps
After building Detect Virtual Space, Appdome generates a Certified Secure™ certificate to guarantee that the Detect Virtual Space protection has been added and is protecting the app. To verify that the Detect Virtual Space protection has been added to the mobile app, locate the protection in the Certified Secure™ certificate as shown below:
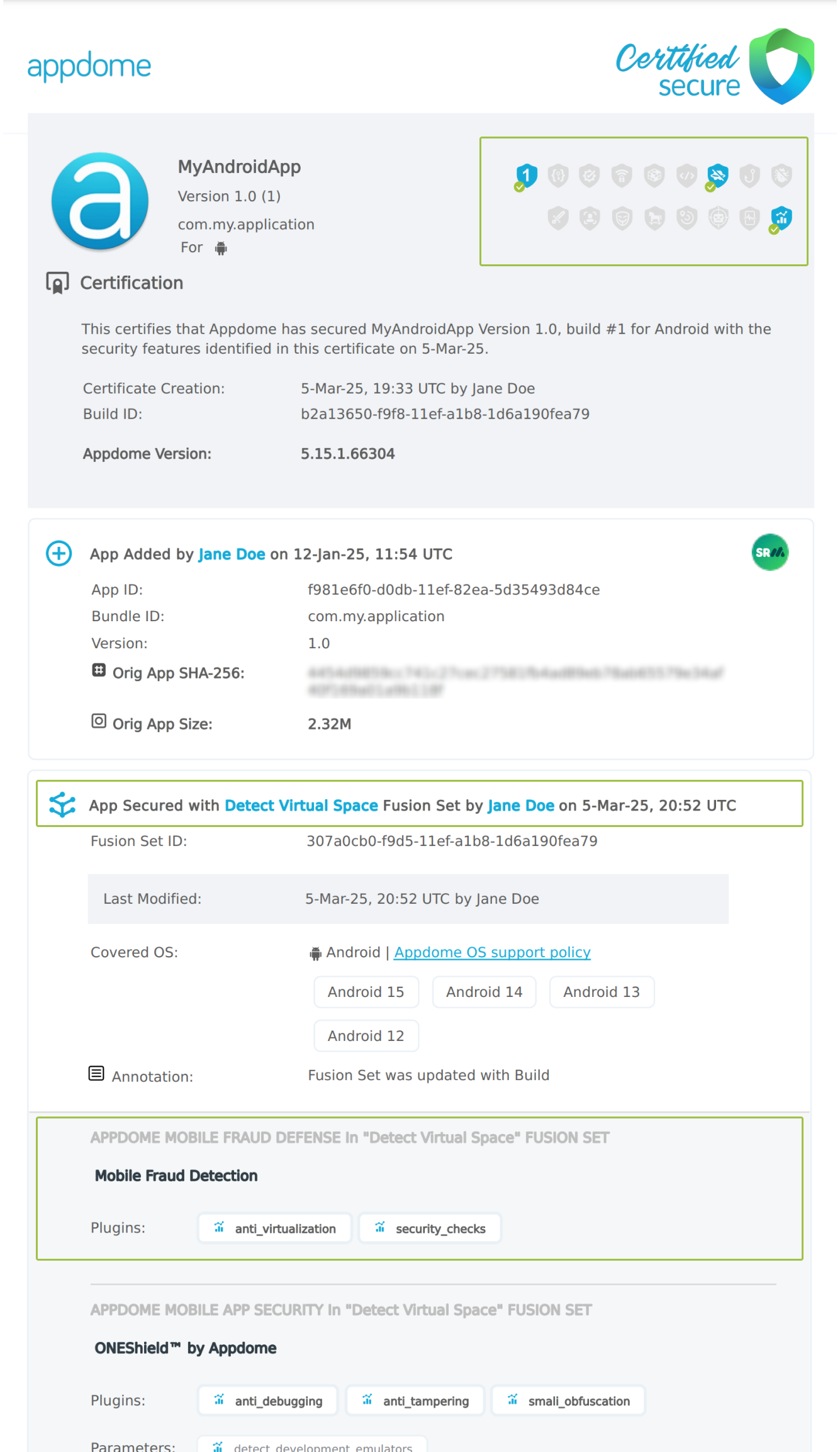
Figure 6: Certified Secure™ certificate
Each Certified Secure™ certificate provides DevOps and DevSecOps organizations the entire workflow summary, audit trail of each build, and proof of protection that Detect Virtual Space has been added to each Android app. Certified Secure provides instant and in-line DevSecOps compliance certification that Detect Virtual Space and other mobile app security features are in each build of the mobile app.
Using Threat-Events™ for Virtual Space Intelligence and Control in Android Apps
Appdome Threat-Events™ provides consumable in-app mobile app attack intelligence and defense control when Virtual Space is detected. To consume and use Threat-Events™ for Virtual Space in Android Apps, use registerReceiver in the Application OnCreate, and the code samples for Threat-Events™ for Virtual Space shown below.
The specifications and options for Threat-Events™ for Virtual Space are:
| Threat-Event™ Elements | Detect Virtual Space Method Detail |
|---|---|
| Appdome Feature Name | Detect Virtual Space |
| Threat-Event Mode | |
| OFF, IN-APP DEFENSE | Appdome detects, defends and notifies user (standard OS dialog) using customizable messaging. |
| ON, IN-APP DETECTION | Appdome detects the attack or threat and passes the event in a standard format to the app for processing (app chooses how and when to enforce). |
| ON, IN-APP DEFENSE | Uses Appdome Enforce mode for any attack or threat and passes the event in a standard format to the app for processing (gather intel on attacks and threats without losing any protection). |
| Certified Secure™ Threat Event Check | |
| Visible in ThreatScope™ | |
| Developer Parameters for Detecting Virtual Space Threat-Event™ | |
| Threat-Event NAME | RunningInVirtualSpace |
| Threat-Event DATA | reasonData |
| Threat-Event CODE | reasonCode |
| Threat-Event REF | 6801 |
| Threat-Event SCORE | |
| currentThreatEventScore | Current Threat-Event score |
| threatEventsScore | Total Threat-events score |
| Threat-Event Context Keys | |
|---|---|
| Timestamp | The exact time the threat event was triggered, recorded in milliseconds since epoch |
| message | Message displayed for the user on event |
| externalID | The external ID of the event which can be listened via Threat Events |
| osVersion | OS version of the current device |
| deviceModel | Current device model |
| deviceManufacturer | The manufacturer of the current device |
| fusedAppToken | The task ID of the Appdome fusion of the currently running app |
| kernelInfo | Info about the kernel: system name, node name, release, version and machine. |
| carrierPlmn | PLMN of the device. Only available for Android devices. |
| deviceID | Current device ID |
| reasonCode | Reason code of the occurred event |
| deviceBrand | Brand of the device |
| deviceBoard | Board of the device |
| buildUser | Build user |
| buildHost | Build host |
| sdkVersion | Sdk version |
| threatCode | The last six characters of the threat code specify the OS, allowing the Threat Resolution Center to address the attack on the affected device. |
| virtualSpaceApp | Package name of the virtual space app |
With Threat-Events™ enabled (turned ON), Android developers can get detailed attack intelligence and granular defense control in Android applications and create amazing user experiences for all mobile end users when Virtual Space is detected.
The following is a code sample for native Android apps, which uses all values in the specification above for Detect Virtual Space:
Important! Replace all placeholder instances of <Context Key> with the specific name of your threat event context key across all language examples. This is crucial to ensure your code functions correctly with the intended event data. For example, The <Context Key> could be the message, externalID, OS Version, reason code, etc.
xxxxxxxxxxIntentFilter intentFilter = new IntentFilter();intentFilter.addAction("RunningInVirtualSpace");BroadcastReceiver threatEventReceiver = new BroadcastReceiver() { public void onReceive(Context context, Intent intent) { String message = intent.getStringExtra("message"); // Message shown to the user String reasonData = intent.getStringExtra("reasonData"); // Threat detection cause String reasonCode = intent.getStringExtra("reasonCode"); // Event reason code // Current threat event score String currentThreatEventScore = intent.getStringExtra("currentThreatEventScore"); // Total threat events score String threatEventsScore = intent.getStringExtra("threatEventsScore"); // Replace '<Context Key>' with your specific event context key // String variable = intent.getStringExtra("<Context Key>"); // Your logic goes here (Send data to Splunk/Dynatrace/Show Popup...) }};if (Build.VERSION.SDK_INT >= Build.VERSION_CODES.TIRAMISU) { registerReceiver(threatEventReceiver, intentFilter, Context.RECEIVER_NOT_EXPORTED);} else { registerReceiver(threatEventReceiver, intentFilter);}xxxxxxxxxxval intentFilter = IntentFilter()intentFilter.addAction("RunningInVirtualSpace")val threatEventReceiver = object : BroadcastReceiver() { override fun onReceive(context: Context?, intent: Intent?) { var message = intent?.getStringExtra("message") // Message shown to the user var reasonData = intent?.getStringExtra("reasonData") // Threat detection cause var reasonCode = intent?.getStringExtra("reasonCode") // Event reason code // Current threat event score var currentThreatEventScore = intent?.getStringExtra("currentThreatEventScore") // Total threat events score var threatEventsScore = intent?.getStringExtra("threatEventsScore") // Replace '<Context Key>' with your specific event context key // var variable = intent?.getStringExtra("<Context Key>") // Your logic goes here (Send data to Splunk/Dynatrace/Show Popup...) }}if (Build.VERSION.SDK_INT >= Build.VERSION_CODES.TIRAMISU) { registerReceiver(threatEventReceiver, intentFilter, Context.RECEIVER_NOT_EXPORTED)} else { registerReceiver(threatEventReceiver, intentFilter)}xxxxxxxxxxconst { ADDevEvents } = NativeModules;const aDDevEvents = new NativeEventEmitter(ADDevEvents);function registerToDevEvent(action, callback) { NativeModules.ADDevEvents.registerForDevEvent(action); aDDevEvents.addListener(action, callback);}export function registerToAllEvents() { registerToDevEvent( "RunningInVirtualSpace", (userinfo) => Alert.alert(JSON.stringify(userinfo)) var message = userinfo["message"] // Message shown to the user var reasonData = userinfo["reasonData"] // Threat detection cause var reasonCode = userinfo["reasonCode"] // Event reason code // Current threat event score var currentThreatEventScore = userinfo["currentThreatEventScore"] // Total threat events score var threatEventsScore = userinfo["threatEventsScore"] // Replace '<Context Key>' with your specific event context key // var variable = userinfo["<Context Key>"] // Your logic goes here (Send data to Splunk/Dynatrace/Show Popup...) );}x
RegisterReceiver(new ThreatEventReceiver(), new IntentFilter("RunningInVirtualSpace")); class ThreatEventReceiver : BroadcastReceiver{ public override void OnReceive(Context context, Intent intent) { // Message shown to the user String message = intent.GetStringExtra("message"); // Threat detection cause String reasonData = intent.GetStringExtra("reasonData"); // Event reason code String reasonCode = intent.GetStringExtra("reasonCode"); // Current threat event score String currentThreatEventScore = intent.GetStringExtra("currentThreatEventScore"); // Total threat events score String threatEventsScore = intent.GetStringExtra("threatEventsScore"); // Replace '<Context Key>' with your specific event context key // String variable = intent.GetStringExtra("<Context Key>"); // Your logic goes here (Send data to Splunk/Dynatrace/Show Popup...) }}x
NSNotificationCenter.DefaultCenter.AddObserver( (NSString)"RunningInVirtualSpace", // Threat-Event Identifier delegate (NSNotification notification) { // Message shown to the user var message = notification.UserInfo.ObjectForKey("message"); // Threat detection cause var reasonData = notification.UserInfo.ObjectForKey("reasonData"); // Event reason code var reasonCode = notification.UserInfo.ObjectForKey("reasonCode"); // Current threat event score var currentThreatEventScore = notification.UserInfo.ObjectForKey("currentThreatEventScore"); // Total threat events score var threatEventsScore = notification.UserInfo.ObjectForKey("threatEventsScore"); // Replace '<Context Key>' with your specific event context key // var variable = notification.UserInfo.ObjectForKey("<Context Keys>"); // Your logic goes here (Send data to Splunk/Dynatrace/Show Popup...) });xxxxxxxxxxwindow.broadcaster.addEventListener("RunningInVirtualSpace", function(userInfo) { var message = userInfo.message // Message shown to the user var reasonData = userInfo.reasonData // Threat detection cause var reasonCode = userInfo.reasonCode // Event reason code // Current threat event score var currentThreatEventScore = userInfo.currentThreatEventScore // Total threat events score var threatEventsScore = userInfo.threatEventsScore // Replace '<Context Key>' with your specific event context key // var variable = userInfo.<Context Keys> // Your logic goes here (Send data to Splunk/Dynatrace/Show Popup...)});x
import 'dart:async';import 'package:flutter/material.dart';import 'package:flutter/services.dart';class PlatformChannel extends StatefulWidget { const PlatformChannel({super.key}); State<PlatformChannel> createState() => _PlatformChannelState();}class _PlatformChannelState extends State<PlatformChannel> { // Replace with your EventChannel name static const String _eventChannelName = "RunningInVirtualSpace"; static const EventChannel _eventChannel = EventChannel(_eventChannelName); void initState() { super.initState(); _eventChannel.receiveBroadcastStream().listen(_onEvent, onError: _onError); } void _onEvent(Object? event) { setState(() { // Adapt this section based on your specific event data structure var eventData = event as Map; // Example: Accessing 'externalID' field from the event var externalID = eventData['externalID']; // Customize the rest of the fields based on your event structure String message = eventData['message']; // Message shown to the user String reasonData = eventData['reasonData']; // Threat detection cause String reasonCode = eventData['reasonCode']; // Event reason code // Current threat event score String currentThreatEventScore = eventData['currentThreatEventScore']; // Total threat events score String threatEventsScore = eventData['threatEventsScore']; // Replace '<Context Key>' with your specific event context key // String variable = eventData['<Context Keys>']; }); } // Your logic goes here (Send data to Splunk/Dynatrace/Show Popup...)}Using Appdome, there are no development or coding prerequisites to build secured Android Apps by using Detect Virtual Space. There is no SDK and no library to code or implement in the app and no gateway to deploy in your network. All protections are built into each app and the resulting app is self-defending and self-protecting.
Releasing and Publishing Mobile Apps with Detect Virtual Space
After successfully securing your app by using Appdome, there are several available options to complete your project, depending on your app lifecycle or workflow. These include:
- Customizing, Configuring & Branding Secure Mobile Apps.
- Deploying/Publishing Secure mobile apps to Public or Private app stores.
- Releasing Secured Android & iOS Apps built on Appdome.
Related Articles:
- How to Block Auto-Clicking & Fake Events, Protect Android Apps
- How to Block Android Debug Bridge (ADB) Exploits, Protect Android Apps
- Block ARM-in-ARM Virtual Devices for Android & iOS Apps
How Do I Learn More?
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.