How to Make Mobile Apps Work with NTLM Authentication
Learn how to Make Mobile Apps Work with Microsoft NTLM Authentication – no code, no SDK.
What is NTLM?
NTLM is an Authentication Protocol used in Microsoft Windows environments for authentication between clients and servers. NTLM uses a challenge-response mechanism for authentication, in which clients are able to prove their identities without sending their password to the server. Mobile Authentication to industry-standard Microsoft Active Directory (AD) using NTLM has always posed challenges as many mobile apps don’t speak NTLM natively.
This knowledge base article demonstrates how to add NTLM capabilities to any mobile app to authenticate with Microsoft Active Directory without coding or development.
Adding NTLM to Mobile Apps for Authentication to Microsoft AD
Appdome is a no-code mobile app security platform designed to add security features and 3rd party services like Microsoft ADFS to Android and iOS apps without coding. This KB shows mobile developers, DevSec and security professionals how to use Appdome’s simple ‘click to build’ user interface to quickly and easily make mobile apps work with Microsoft authentication.
Mobile apps usually don’t support webviews at the authentication point and don’t have a mechanism to receive and store external cookies from the AD server. Active Directory and NTLM services also don’t have a framework to share authentication state among apps on a device.
Using Appdome, authentication to Microsoft AD from Android and iOS apps can be accomplished even if the original app does not support AD, NTLM or Kerberos. With Appdome, developers and enterprises can integrate NTLM to mobile apps providing seamless and true SSO authentication for mobile users.
Prerequisites for Adding NTLM to Mobile Apps
There is no prerequisite that the mobile app, or its server, to support SAML, OAuth, OAuth 2.0, OpenID Connect or other standards prior to using Appdome. For more information on how Appdome gets, retrieves and stores Active Directory cookies in mobile apps, please review the data sheet on No Code Microsoft Authentication in Mobile Apps.
In order to use Appdome’s no code implementation of Microsoft authentication on Appdome, you’ll need:
- Appdome account
- Mobile App (.ipa for iOS, or .apk for Android)
- AD Hub URL
- Authentication Successful URI on AD
- Application protected resource URL
- Signing Credentials (e.g., signing certificates and provisioning profile)
A Few Easy Steps to Make Mobile Apps Work with NTLM Authentication
Upload a Mobile App to Your Account
Please follow these steps to add a mobile app to your Appdome account.
If you don’t have an Appdome account, click here to create an account.
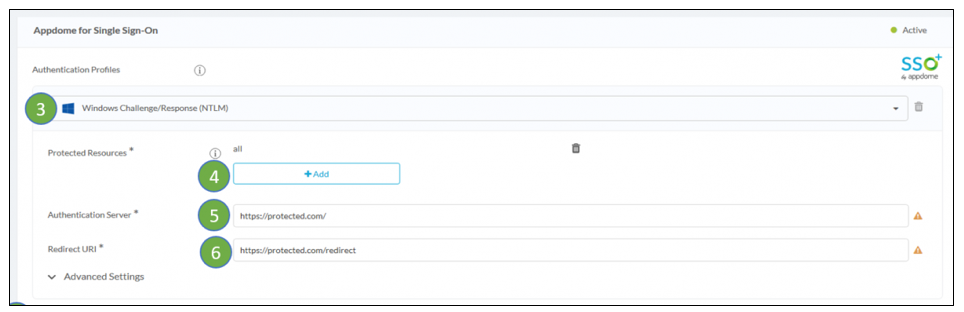
- From the “Build” tab, go to the Authentication tab.
- Enable Authentication Profiles
- Select Windows Challenge/Response (NTLM)
- If you want to set specific resources that require the SSO authentication, change the “Protected Resource” from “all” to any URL you want, you can add several addresses.
- Add the Authentication Server URL.
- Add the Redirect URI.
- Click Build My App
The technology behind Build My App has two major elements – (1) a microservice architecture filled with 1000s of code sets needed for mobile integration, and (2) an adaptive code generation engine that can recognize the development environment, frameworks and methods in each app and match the app to the relevant code-sets needed to add Microsoft AD to the mobile app in seconds (instead of requiring mobile developers to manually modify source code to implement the required authentication functionality or framework).
Congratulations! You now have a mobile app fully integrated with Microsoft AD/NTLM.
No Coding Dependency
How to Sign & Publish Secured Mobile Apps Built on Appdome
After successfully building your app using Appdome, there are several available options to complete your project, depending on your app lifecycle or workflow. These include:
- Signing Secure iOS and Android apps
- Customizing, Configuring & Branding Secure Mobile Apps
- Deploying/Publishing Secure mobile apps to Public or Private app stores
Or, see this quick reference Releasing Secured Android & iOS Apps built on Appdome.
How to Learn More
Appdome provides additional alternatives for No Code Microsoft Authentication in Mobile Apps. Appdome also has other no code implementations for MicroVPN and enterprise mobility, all of which can be combined with Microsoft Authentication on Appdome or implemented in a standalone manner.
To zoom out on this topic, please visit our Mobile Identity page.
If you have any questions, please send them our way at support@appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project. If you don’t already have an account, you can sign up for free.