How to Use Appdome MobileBOT™ Defense
How Traditional Anti-Bot Offerings Work
Traditional anti-bot offerings have struggled to keep pace with the evolving diversity and sophistication of mobile applications. They often try to force-fit bot defense methods designed for web applications onto mobile frameworks. This mismatch often requires mobile app developers to change the mobile application network stack, remove valuable TLS-protecting network connections, or limit bot defense to singular hosts. The result of an increasingly mobile app-driven economy is that larger parts of the mobile infrastructure are left vulnerable to mobile bot attacks, fraud, ATOs, API abuse, credential stuffing, and more.
What is Appdome MobileBOT™ Defense?
The new MobileBOT™ Defense solution offers mobile brands unparalleled bot detection, comprehensive intelligence, and rapid defense against malicious bots, credential stuffing, and ATOs in mobile app business lines.
Appdome’s MobileBOT™ combines several defense methods to address these weaknesses and provide a robust solution for securing mobile apps against malicious bots. MobileBOT™ offers full support for all mobile languages and frameworks, including Obj-C, Java, JS, C#, C++, Swift, Kotlin, Flutter, React Native, Unity, Maui, Xamarin, Cordova, and more. Integration with your mobile apps is facilitated through a No-Code, No-SDK, and Fully Automated Delivery built to integrate seamlessly with mobile DevOps pipelines.
Prerequisites for using Appdome’s MobileBOT™ Defense:
To use Appdome’s mobile app security build system for Mobile Bot Defense, you’ll need:
- Appdome account (create a free Appdome account here)
- A license for MobileBOT™
- Mobile App (.ipa for iOS device or .apk or .aab for Android)
- Signing Credentials (see Signing Secure Android apps and Signing Secure iOS apps)
- A license for Threat-Event™ Meta-Data
- A license for ThreatScore™ Data
Overview of Appdome MobileBOT™ Defense Features
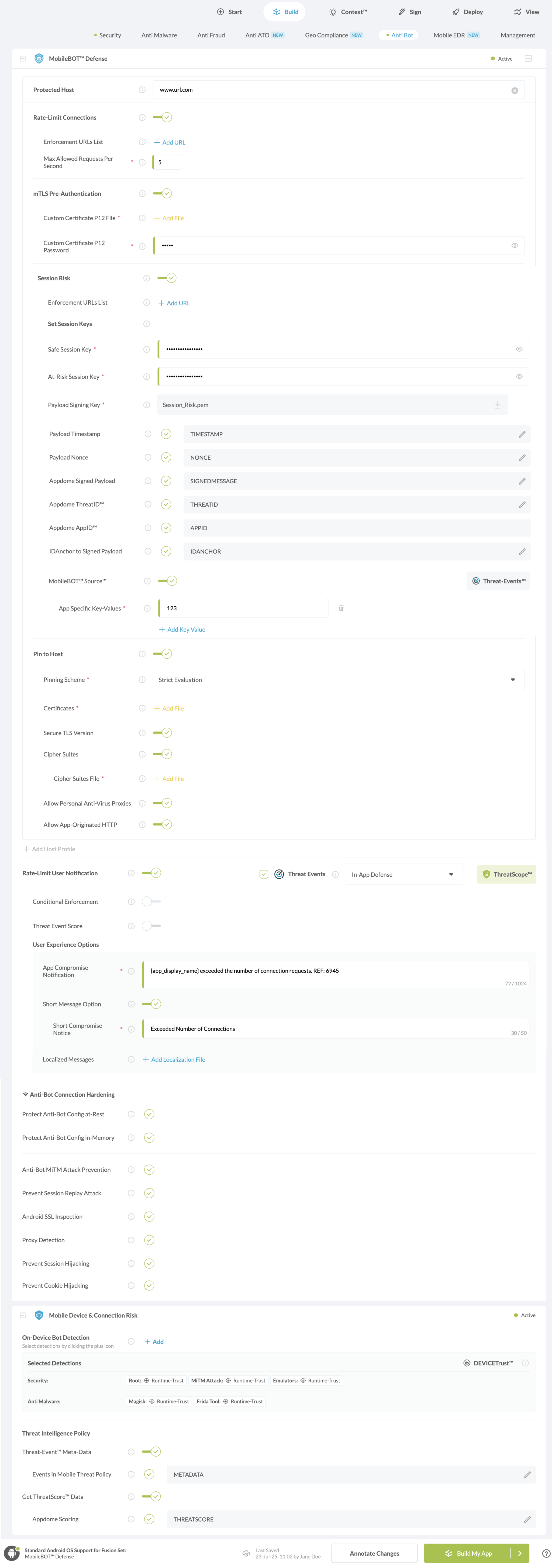
MobileBOT™ Defense
Protected Host
The Mobile AntiBot solution is configured to allow the addition of multiple protected hosts. Each host is individually fortified with several security features such as mTLS Pre-Authentication, Session Risk, and Secure Certificate Pinning.
Rate Limit Connections
Learn more about How to Enforce Rate Limiting in MobileBOT™ Defense
mTLS Pre-Authentication
Appdome’s mTLS Pre-Authentication can be used as the fourth verification layer before the Anti-Bot payload is sent to the WAF using a P12 client certificate in the TLS handshake. mTLS Re-Authentication is a quick and easy way to identify good mobile app requests from bad ones.
Learn more about How to Sign Secured iOS Apps Using P12 Distribution Certificate
Heartbeat Solution
The Heartbeat Solution is an advanced security framework by Appdome designed to safeguard application sessions. It comprises four main elements: Session Risk, Safe Sessions, At-Risk Sessions, and a Payload Signing Key.
Note: The heartbeat solution does not include secure certificate pinning, rate limiting, or client certificates.
Session Risk
Appdome’s session risk employs a multi-layered approach with application fingerprinting to guarantee not only a tamper-proof payload but also to enhance the WAF’s ability to thwart session replay attacks. This structure offers the WAF insight into the security status of the device running the protected app. Moreover, the WAF can obtain data on threats identified by the protected app and can accurately differentiate between attacks coming from various devices.
To guarantee that the anti-bot signal cannot be spoofed by an attacker, Appdome protects all data in transit with pre-packaged and optional features like Secure Certificate Pinning to the (WAF), TLS Session hardening, active MitM Defense, and optional WAF encryption for the Session Risk Payload (over and above the RSA Key).
Note: Please be aware that Security Certificate Pinning and the Anti Bot Pin to Host are mutually exclusive. Implementing them together will result in a conflict within the engine. Ensure to use only one method at a time to avoid potential issues.
Note: All protections available under “Standard Device & Connection Risk” are only accessible when the “Session Risk” feature is enabled.
Enforce URLs List: Enter Specific URLs to be protected by MobileBOT™ Defense. You can add hosts by clicking the `+ Add URL ‘ button.
Safe Session
Represents sessions that are determined to be safe or not at risk of any threat.
At Risk Session
Represents sessions that are potentially under threat or have detected anomalies.
Payload Signing Key
The public key that Appdome uses to encrypt the payload.
Payload Timestamp
Learn more about How to Use Payload Timestamps In Mobile Bot Defense
Appdome ThreatID™
Learn more about How to Use Appdome ThreatID™ In Mobile Bot Defense
Payload Nonce
Learn more about How to Validate a Nonce Payload with Appdome MobileBOT™ Defense
Appdome Signed Payload
Ensures data integrity and security by verifying the digital signature of each payload before connection.
Appdome AppID™
Learn more about How to Use Appdome AppID In Mobile Bot Defense
Pin to Host
Learn more about How to Secure Android & iOS Apps with Pin to Host
Anti-Bot Connection Hardening
To eliminate hijacking and replay attacks, Appdome’s MobileBOT™ Defense solution protects all data-in-rest with pre-packaged features such as data-at-rest encryption for all Anti-Bot configurations, secrets, keys, IDs, etc., as well as a protected memory space for all Anti-Bot functions.
MitM Attack Prevention enables the performance of mTLS pre-authentication, monitors connections for MitM attacks, and safeguards connections and anti-bot payload in transit between the anti-bot solution and any industry standard WAF.
Protect Anti-Bot Config at Rest
Encrypts all Mobile Anti-Bot configurations, including host, keys, certificates, etc., at rest to prevent the harvesting.
Protect Anti-Bot Config in-Memory
Prevents attackers from harvesting Mobile Anti-Bot configurations, including host, keys, certificates, etc., in memory.
Prevent Session Replay Attack
Appdome detects and prohibits session replay attacks and reclaims SessionID for stale TLS sessions so that hackers cannot reuse them in their attacks.
Prevent Session Hijacking
Appdome detects, prohibits, and protects app connections from session hijacking by validating the server SSL certificate chain’s authenticity and providing authenticity proof to the server on behalf of the client.
Prevent Cookie Hijacking
Appdome detects, prohibits, and protects app connections against cookie hijacking by validating the server SSL certificate chain’s authenticity and providing authenticity proof to the server on behalf of the client.
Malicious Proxy Detection
Appdome detects any attempt to connect to or from unknown, untrusted, or malicious proxies or other intermediary devices.
Deep Proxy Detection
Appdome performs a deep inspection of proxies and proxy techniques, including header manipulation and redirects.
Mobile Device & Connection Risk
Mobile Anti-Bot Policy
On-Device Bot Detection enables mobile developers to configure which on-device threats—such as Root, Magisk, Emulators, Jailbreak, Fake Location, and more—will contribute to session risk classification in the app. For each detection, developers define a DEVICETrust™ level: Zero-Trust, which delays connection until checks are complete, or Runtime-Trust, which allows assessment during connection. For example, when adding Detect Fake Location as a detection, the session will be classified as compromised based on location spoofing. This configuration feeds into Mobile Device & Connection Risk, which tags each session as Safe or At-Risk and enables WAFs and backend systems to validate session authenticity in real time.
Note: Please be aware that the MitM Prevention and Mobile Anti Bot Policy features are mutually exclusive. Implementing them together will result in a conflict within the engine. To avoid potential issues, ensure that you use only one method at a time.
Threat Intelligence Policy
Threat-Event Meta-Data is an optional configuration in Mobile Device & Connection Risk that enriches mobile bot detection payloads with additional environmental context, including operating system, device model, manufacturer, and SSL certificate metadata. These metadata fields are used by WAFs to assess whether the mobile session originates from a legitimate safe or at-risk endpoint.
ThreatScore is another optional configuration that adds a numeric risk score to each user and device session, helping backend systems quantify and respond to bot and automation threats. This score reflects the cumulative risk based on detected mobile threats—such as root, Magisk, emulators, or fake location—and provides a simplified value to inform automated policy decisions.
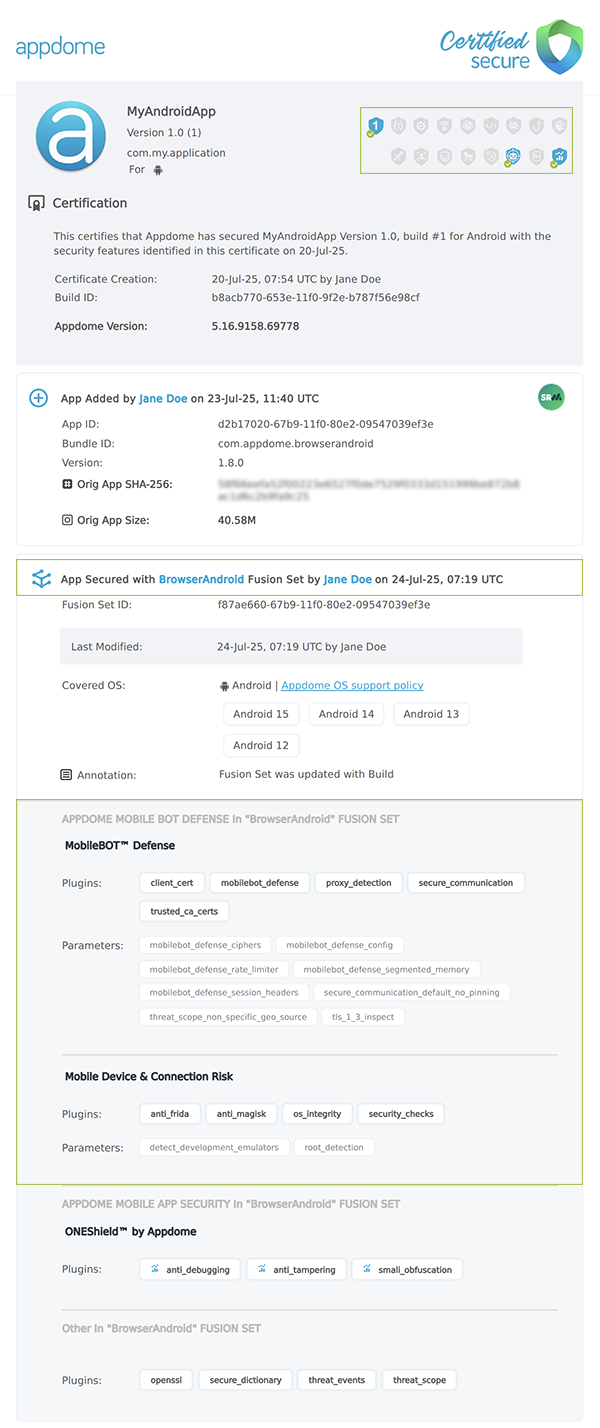
Certify the MobileBOT™ Defense features in Android & iOS Apps.
After building MobileBOT™ Defense features, Appdome generates a Certified Secure™ certificate to guarantee that the MobileBOT™ Defense protection has been added and is protecting the app. To verify that the MobileBOT™ Defense protection has been added to the mobile app, locate the protection in the Certified Secure™ certificate as shown below:
Related Articles:
- How to Use Session Risk in Mobile Bot Defense
- How to Secure Android & iOS Apps with Pin to Host
- How to use MobileBOT Source™ with Mobile Bot Defense
- How to use DEVICETrust™ with MobileBOT™ Defense
How Do I Learn More?
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project. If you don’t already have an account, you can sign up for free.